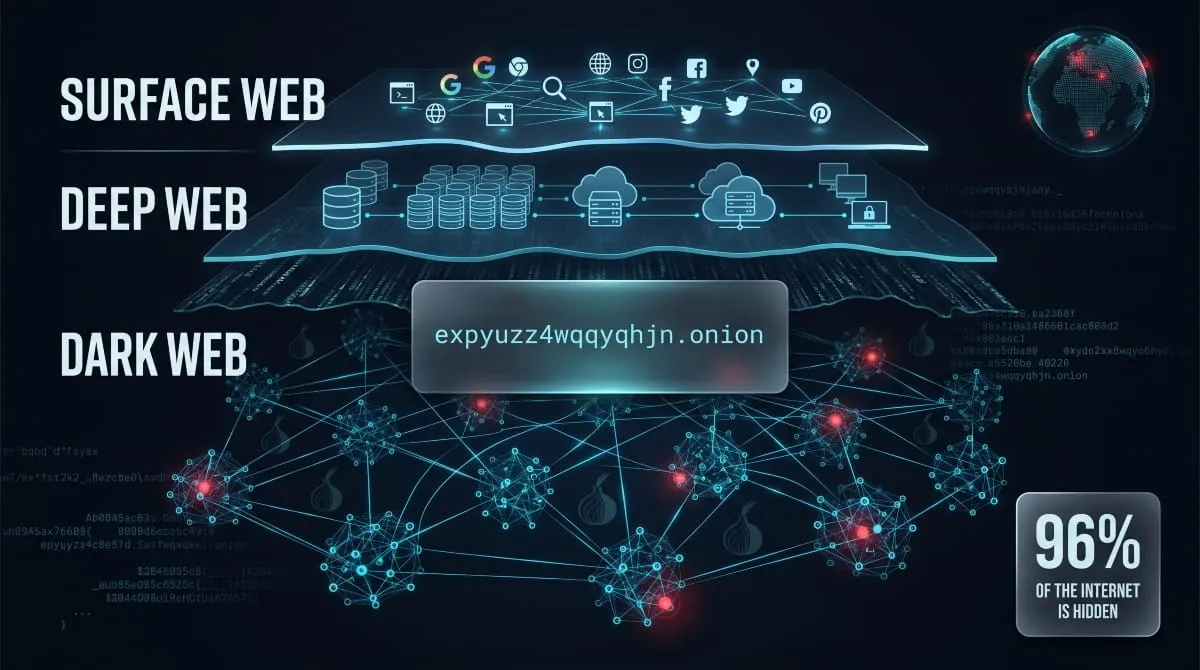
Every day, billions of people use the internet without ever knowing that the websites they visit represent less than 5% of what actually exists online. Beneath the surface web sits an entirely separate layer, one that standard browsers can’t reach, search engines don’t index, and most people only hear about in headlines involving data breaches, cybercrime investigations, or leaked government documents.
That layer is the dark web, and it runs on a completely different addressing system. Instead of the familiar .com or .org domains you’re used to, dark web links use .onion addresses, long, encrypted strings of characters that only resolve inside the Tor network. These aren’t broken URLs or coding errors. They’re intentional, privacy-engineered addresses built to be anonymous, untraceable, and inaccessible by design.
But here’s what most guides won’t tell you: the dark web isn’t a single, unified place. It’s a fragmented ecosystem of search engines, link directories, forums, marketplaces, news mirrors, and intelligence resources, each with its own address, purpose, and risk level. Some dark web links lead to legitimate privacy tools and journalist platforms. Others lead to the kind of infrastructure that threat analysts, cybersecurity researchers, and platforms like DeXpose monitor around the clock to protect businesses and individuals from exposure.
This guide covers what dark web links actually are, how .onion addresses work, which directories and search engines are real, and what the most notable sites in this ecosystem mean for your security. Whether you’re a cybersecurity professional, a researcher, or simply someone who wants to understand what’s out there, and whether your data has ended up there, this is the most complete, up-to-date resource available in 2026.
What Are Dark Web Links? (.onion URLs Explained)
A dark web link is not like any web address you’ve encountered before. It doesn’t end in .com, .net, or .org. It can’t be typed into Chrome or Safari and resolved into a page. And it certainly won’t appear in a Google search result. Dark web links are purpose-built addresses that exist exclusively within the Tor network, a privacy infrastructure originally developed by the U.S. Naval Research Laboratory and now maintained as an open-source anonymity tool used by journalists, activists, researchers, and, unfortunately, cybercriminals alike.
At their core, dark web links are simply the addressing system for hidden services, websites, and servers deliberately configured to operate outside the visible internet. Understanding them isn’t about learning how to access them. It’s about understanding the architecture of a part of the internet that directly affects data security, threat intelligence, and cybercrime, whether you visit it or not.
How Dark Web Links Differ from Surface Web URLs
On the surface web, a URL like https://dexpose.io follows a predictable structure: a protocol, a domain name, and an extension registered through a public domain authority. That domain resolves to an IP address through the global DNS system, which means the server behind it has a known, traceable location.

Dark web links operate on an entirely different logic. They bypass the public DNS system entirely. Instead of resolving through centralized registrars, .onion addresses are self-authenticated, meaning the address itself is derived from the site’s cryptographic public key. There is no registrar, no IP lookup, and no central authority that knows where the server physically sits. The Tor network routes traffic through a chain of encrypted relays, making both the visitor and the server location effectively anonymous to outside observers.
This is the fundamental difference: surface web URLs are transparent by design, dark web links are anonymous by design.
What Does a .onion Address Look Like?
A modern .onion address, introduced with Tor’s v3 protocol, looks something like this:
http://dreadytofatroptsdj6io7l3xptbet6onoyno2yv7jicoxknyazubrad.onion
That 56-character string isn’t random noise. It’s a Base32-encoded representation of the site’s Ed25519 public key, truncated and formatted for use as an address. Earlier v2 .onion addresses were only 16 characters long, but they were deprecated in 2021 due to weaker cryptographic standards. Today, any legitimate dark web link you encounter should be a 56-character v3 address.
What this means practically: you cannot guess a dark web link, you cannot stumble onto one, and you cannot search for one in a conventional browser. You either know the address, find it in a dark web directory, or discover it through a search engine that runs on the Tor network itself.
Why Dark Web Links Change Frequently
This is one of the most misunderstood aspects of the dark web link ecosystem. Users searching for working dark web links in 2025 or 2026 often find that addresses they previously saved no longer load, and there are several reasons for this.
First, dark websites have no hosting obligation. A server can go offline at any moment, voluntarily or otherwise, with no notice and no forwarding address. Law enforcement seizures, exit scams, and simple abandonment are common causes of sudden link death.
Second, operators frequently rotate their .onion addresses as a security measure. Generating a new cryptographic key pair produces a new address, allowing a site to relocate without any physical infrastructure changes, essentially. From a threat intelligence perspective, tracking these migrations is a significant part of dark web monitoring work.
Third, distributed denial-of-service attacks are common on dark web infrastructure, forcing sites to move or temporarily go dark to avoid disruption.
The result is a constantly shifting landscape where even well-known dark web links have a limited lifespan. Reliable, up-to-date directories and active monitoring, rather than static link lists, are the only way to track what’s live accurately, what’s moved, and what’s been taken down.
How to Access Dark Web Links Safely in 2026
Accessing dark web links isn’t technically complicated. What makes it dangerous isn’t the process, it’s the decisions made before, during, and after. The Tor network itself is legal to use in most countries, and the browser required to access it is free to download. But the absence of technical barriers doesn’t mean there’s no risk. Poor setup, misplaced trust in unverified links, and basic operational errors are responsible for the vast majority of incidents involving exposure to the dark web.

If you’re a researcher, security professional, or someone verifying whether your organization’s data has surfaced somewhere it shouldn’t, this section covers exactly what you need to do it responsibly.
What You Need Before Clicking Any Dark Web Link (Tor Browser Setup)
The only legitimate way to access .onion links is through the Tor Browser, a hardened, privacy-configured version of Firefox maintained by the Tor Project. It routes your traffic through at least three encrypted relays before reaching its destination, masking your IP address and preventing exit node surveillance from being traced back to you.
Download it exclusively from the official source: torproject.org. Any other source, third-party site, file-sharing platform, or Telegram channel claiming to offer “faster” versions should be treated as a potential malware-delivery mechanism. Fake Tor browsers have been documented distributing credential stealers and keyloggers to users who didn’t verify the source.
Before opening any dark web link, a few baseline practices significantly reduce your exposure. Keep JavaScript disabled inside the Tor Browser’s security settings, set to the “Safest” level. Never resize the browser window, as doing so leaks screen resolution data that can be used for fingerprinting. Never log into personal accounts, open documents downloaded from .onion sites in an online environment, or use your real email address on any dark web platform. For higher-risk research, running Tor inside a dedicated virtual machine or using the Tails operating system adds another layer of separation between your activity and your primary device.
How to Open Dark Web Links on Android and iPhone
Mobile access to dark web links is possible, but it comes with significant limitations compared to desktop.
On Android, the Tor Project offers an official app called Tor Browser, available on the Google Play Store and verified directly on torproject.org. It provides the same relay-based anonymity as the desktop version and can resolve .onion addresses natively. A second option is Orbot, a Tor proxy that routes your entire device’s traffic through the Tor network, which can be paired with other privacy browsers for broader protection.
On iPhone and iPad, the situation is more constrained. Apple’s App Store policies prevent true Tor Browser integration at the same level as Android. The most commonly recommended option is Onion Browser, an open-source app endorsed by the Tor Project. However, it operates with some limitations due to iOS restrictions on how apps handle network traffic.
Regardless of platform, mobile dark web browsing carries additional risks. Device identifiers, background app activity, and iOS/Android telemetry can all potentially compromise the anonymity that the Tor network provides at the network level. For sensitive research, mobile access should be a last resort rather than a primary method.
Can You Open Dark Web Links in Google Chrome? (The Truth)
No. And no extension, plugin, or workaround changes that.
Chrome resolves addresses through the public DNS system and routes traffic in ways that are fundamentally incompatible with how .onion addresses work. Even if you install a Tor proxy extension, Chrome’s architecture still leaks DNS requests, browser fingerprint data, and potentially your real IP address through WebRTC. This well-documented vulnerability has exposed users who believed they were browsing anonymously.
Some users attempt to configure a SOCKS5 proxy to point to their local Tor process and browse .onion links in Chrome or Firefox. While this technically resolves some .onion addresses, it strips away most of the protections that make Tor meaningful; it’s like wearing body armor but leaving your helmet at home.
The Tor Browser isn’t just a browser with Tor enabled. It’s a specifically hardened environment designed to prevent the dozens of passive and active fingerprinting techniques that standard browsers are vulnerable to. No shortcut replicates that protection.
Dark Web Links That No Longer Work, and Why
If you’ve followed a link from a forum, a research article, or even a recent guide and found that it no longer loads, you’re in the majority. Link rot is endemic to the dark web, and it happens faster and more completely than anywhere else on the internet.
The reasons are structural. Dark websites have no domain registrar, no hosting contract, and no accountability to stay online. A marketplace can vanish overnight following a law enforcement operation, as has happened repeatedly with major platforms over the past decade. A forum administrator can simply walk away. A server can be seized, burned, or migrated to a new .onion address without prior notice.
Beyond deliberate shutdowns, Tor’s relay network introduces its own connectivity variability. A site may be online but temporarily unreachable due to relay congestion, DDoS attacks, or guard node issues on your specific circuit. Reloading with a new Tor circuit, or trying again later, sometimes resolves what appears to be a dead link.
For threat intelligence purposes, distinguishing between a truly dead link and a temporarily unreachable one matters. Platforms that continuously crawl and re-index dark web infrastructure, rather than relying on static lists compiled months ago, are the only reliable way to track what’s genuinely active versus what’s gone for good.
The Best Dark Web Search Engines & Directories (Updated 2026)
Finding anything on the dark web isn’t as simple as typing a query into Google. There is no single authoritative index of .onion sites, no universal crawler with complete coverage, and no algorithm sophisticated enough to map a network that’s deliberately designed to resist discovery. What exists instead is a loose ecosystem of dark web search engines, curated directories, and community-maintained link lists, each with varying coverage, philosophies, and reliability.

What follows is an accurate, up-to-date overview of the legitimate search tools that researchers, journalists, and security professionals actually use to navigate the dark web. None of these are endorsements to visit the sites they index. They are documented here because understanding the dark web’s navigation infrastructure is essential to understanding how threat actors operate, how data surfaces after a breach, and how platforms like DeXpose track exposure across hidden infrastructure.
Torch, The Oldest Dark Web Search Engine
Torch holds the distinction of being the longest-running search engine on the dark web, operating continuously since 1996. For most of the dark web’s formative years, it was the default starting point for anyone looking for .onion links, the equivalent of AltaVista in the pre-Google era of the surface web.
Its index is broad but unfiltered. Torch crawls and lists .onion sites without editorial curation, which means results range from privacy tools and news mirrors to content that has no place being indexed at all. For researchers, its value lies in raw coverage rather than quality; it surfaces links that more conservative directories deliberately exclude.
Torch is accessible only through the Tor Browser. It has maintained a consistent .onion address through multiple network transitions, making it one of the few dark web search engines with genuine institutional continuity.
Ahmia, The Surface-Accessible Onion Index
Ahmia occupies a unique position in the dark web search engine landscape: it’s one of the very few tools that indexes .onion sites while remaining accessible from a standard browser at ahmia.fi. This makes it particularly useful for researchers and analysts who need to query dark web link data without operating inside the Tor network itself.
The key differentiator is editorial filtering. Ahmia explicitly blocks sites hosting illegal content, particularly child sexual abuse material, and maintains a publicly accessible blocklist. This makes it one of the more defensible tools to reference in a professional or academic context, and it’s frequently cited in cybersecurity research for that reason.
For threat intelligence work, Ahmia’s surface-web accessibility is genuinely useful: it allows security teams to monitor whether specific .onion addresses are indexed and discoverable without requiring a full Tor environment for every query.
Haystack, The Largest Dark Web Index
Haystack claims to maintain the largest index of dark web links of any search engine on the Tor network, with a crawl database reported to be in the billions of pages. Whether that figure is independently verifiable is another matter; the dark web doesn’t publish audited statistics, but Haystack’s coverage is consistently cited as broader than most alternatives.
Its interface is deliberately minimal, and like Torch, it operates without heavy editorial filtering. The search results reflect the dark web as it actually is, rather than a curated version, which makes Haystack a more complete research tool but a less appropriate one for casual use. For security professionals mapping dark web infrastructure or tracking the spread of specific content across hidden services, the breadth of its index is its primary value.
Not Evil, Candle & Excavator, Alternative Search Tools
These three search engines serve a similar purpose but approach indexing differently, making them useful as cross-reference tools rather than primary sources.
Not Evil was designed as a direct philosophical counterpoint to Torch’s unfiltered approach. Its name references Google’s motto, and its moderation policy aims to exclude overtly illegal content from search results. Coverage is narrower than that of Torch or Haystack, but what it surfaces tends to be more relevant to legitimate research queries.
Candle is a minimalist dark web search engine with a deliberately narrow index, modeled visually after early Google. It prioritizes simplicity over comprehensiveness, making it a reasonable first stop for basic .onion link discovery without wading through the noise generated by larger indexes.
Excavator takes a different approach by focusing on freshness over volume, prioritizing recently discovered or recently updated .onion links rather than maintaining a static historical index. For tracking newly emerging dark web infrastructure, Excavator’s recency bias makes it a useful complement to the broader indexes above.
Daniel’s Onion Link List, Curated Directory
Daniel’s site is one of the most referenced human-curated dark web link directories still in operation. Unlike automated search engines, Daniel’s list is manually maintained and categorized, which means the links it contains have been reviewed rather than simply crawled and indexed.
The directory organizes .onion links by category, forums, search engines, email services, privacy tools, and more, with uptime indicators showing which links are currently live. That last feature makes it particularly practical: rather than clicking through dead links, users can see at a glance which .onion addresses are actually resolving before attempting to visit them.
For researchers building a map of the dark web’s legitimate infrastructure, Daniel’s list serves as a reliable baseline, not comprehensive, but consistently maintained and cross-referenced against known active sites.
DuckDuckGo on Tor, Private Search Without Indexing
DuckDuckGo is the default search engine built into the Tor Browser, and its role in the dark web link ecosystem is frequently misunderstood. DuckDuckGo does not index .onion sites. Searching for a dark web link through DuckDuckGo will not return .onion results; it will return surface web results about the dark web, which is a meaningful distinction.
What DuckDuckGo provides inside the Tor Browser is a privacy-respecting surface web search experience: no tracking, no personalized results, no behavioral profiling. Its .onion mirror (duckduckgogg42xjoc72x3sjasowoarfbgcmvfimaftt6twagswzczad.onion) allows users to run surface web searches entirely within the Tor network, preventing even the exit node from seeing the search destination.
For navigating to actual dark web links, DuckDuckGo is not the right tool. For researching dark web topics, threat actors, or breach incidents within a protected Tor environment, it’s exactly what it’s designed for.
Hidden Wiki & Link Directories, What They Are and How to Use Them
Before dark web search engines became more sophisticated, the primary way anyone navigated .onion space was through manually maintained link directories, and none became more synonymous with that function than the Hidden Wiki. For anyone researching dark web links, understanding what these directories are, how they’ve evolved, and why blind trust in them is a serious mistake is foundational knowledge.

What Is the Hidden Wiki?
The Hidden Wiki is a community-edited wiki hosted as a .onion site that functions as a directory of dark web links, organized by category. Think of it as an early-internet web ring, a manually compiled list of addresses pointing to other sites, maintained by anonymous contributors with no central editorial authority.
It first appeared around 2007 and quickly became the default entry point for new Tor users seeking a starting point in an otherwise unmapped environment. At its peak, it was the most linked-to resource in dark web link discussions, referenced across forums, Reddit threads, and early cybersecurity publications as the go-to index of .onion addresses.
The important nuance is that “the Hidden Wiki” is not a single, stable entity. Because the original wiki was copied, forked, and relaunched dozens of times over the years by different operators with different content policies and agendas, there are now multiple sites operating under the Hidden Wiki name or presenting themselves as the “official” version. There is no official version. There never was. The name itself has become a brand that anyone can apply to any link directory they choose to host on a .onion address, which has significant implications for how much trust any version of it deserves.
Are Hidden Wiki Links Safe or Scams?
The direct answer: a significant portion of Hidden Wiki links, across most versions of the directory, are either dead, misleading, or actively dangerous.
This isn’t a recent development. Because Hidden Wiki entries are community-edited and unmoderated on most forks, the directory has historically been infiltrated by operators listing fraudulent services, fake marketplaces, phishing clones of legitimate sites, and honeypots designed to collect visitor data. Scam entries advertising counterfeit goods, fake document services, or “anonymous” financial transactions are endemic to the format. The anonymity that protects legitimate contributors equally protects bad actors who want to weaponize the directory itself as a traffic source for fraud.
Beyond active scams, link rot is severe. The Hidden Wiki was never designed for real-time uptime monitoring, which means a large proportion of links in any given version were compiled months or years ago and have since gone offline, been seized, or migrated to new addresses. A user clicking through a Hidden Wiki list without verification is navigating by a map that may be entirely outdated.
For cybersecurity researchers, the Hidden Wiki is useful as an artifact, a snapshot of how dark web link infrastructure was organized at a particular point in time, and a source of historical .onion addresses worth monitoring. As a live navigation tool, it requires extensive cross-referencing and verification before any link in it can be considered reliable.
How to Verify a Dark Web Link Before Visiting
Verification matters more on the dark web than anywhere else on the internet. Phishing clones of legitimate .onion sites are common, visually identical copies hosted on slightly different addresses, designed to capture credentials or deliver malware to users who didn’t check what they were actually clicking.
The first and most important step is cross-referencing. Any dark web link worth visiting should be verifiable across multiple independent sources, ideally a search engine index like Ahmia, a curated directory like Daniel’s list, and community references on forums like Dread. If an address only appears in one place, that’s a signal worth taking seriously.
Second, check the address character by character against known verified versions. .onion addresses are long and deliberately difficult to memorize, which is exactly what phishing operators exploit. A single character substitution in a 56-character v3 address is nearly impossible to catch by eye at speed, but it routes you to an entirely different server. Copy-pasting from a verified source and confirming the full string is the only reliable method.
Third, consult uptime-monitoring tools where available. Daniel’s directory, for example, displays real-time status indicators for listed links. If a site you’re trying to reach shows as offline across multiple monitoring sources, it’s likely down or gone, not a reason to try alternate addresses that claim to be mirrors; these are frequently fraudulent.
Finally, treat any unsolicited dark web link shared via Telegram, a forum DM, a social media post, or email with maximum skepticism. Legitimate dark web resources don’t require aggressive distribution. Unsolicited links are one of the most common vectors for delivering malware or redirecting researchers to credential-harvesting clones of sites they already trust.
Notable Dark Web Sites, What Researchers and Analysts Should Know
Not all dark web links lead to the same kind of infrastructure. The dark web hosts a spectrum of sites ranging from legitimate privacy tools and censorship-resistant journalism platforms to active cybercrime marketplaces and data leak forums that security teams monitor around the clock. Understanding the most significant sites in this ecosystem, what they are, what they did, and what their current status means for threat intelligence is essential context for anyone working in cybersecurity, data protection, or breach response.

This section is not a directory. It’s an analytical overview of the sites that have shaped the dark web’s history and continue to define its present threat landscape.
Dread, The Dark Web’s Reddit Equivalent
Dread is the closest thing the dark web has to a functioning social forum. Launched in 2018 by a pseudonymous administrator known as HugBunter, it was built explicitly to fill the void left by Reddit’s ban on its darknet market communities. Structurally, it mirrors Reddit almost exactly, with upvotes, subforums called “subdreads,” user reputation systems, and threaded discussions.
What makes Dread significant from an intelligence perspective is its role as the dark web’s primary communication layer. Marketplace administrators post announcements there. Vendors discuss exit scams. Law enforcement actions get analyzed in real time by the community they target. When a major dark web marketplace goes offline, Dread is typically where the first credible explanation appears, whether that’s a seizure notice, an administrator statement, or community speculation piecing together what happened.
For threat analysts, Dread is a primary target for monitoring. The forum surfaces early indicators of marketplace migrations, newly emerged threat actors, and active fraud campaigns well before those activities become visible in breach data or law enforcement reports.
Silk Road, The Marketplace That Changed Everything (Historical)
No single site has shaped public understanding of the dark web more than Silk Road. Launched in 2011 by Ross Ulbricht, operating under the pseudonym “Dread Pirate Roberts”, it was the first large-scale dark web marketplace to demonstrate that .onion infrastructure combined with Bitcoin could create a functioning anonymous economy.
At its peak, Silk Road processed an estimated $1.2 billion in transactions across its two-year operational life. It wasn’t simply a marketplace; it was a proof-of-concept. It demonstrated that dark web links could sustain complex, multi-party commercial ecosystems with reputation systems, dispute resolution, and vendor accountability, all operating entirely outside the reach of conventional financial and legal oversight.
The FBI seized Silk Road in October 2013 and arrested Ulbricht, who was subsequently sentenced to life in prison. A successor platform, Silk Road 2.0, launched within weeks of the original’s takedown and was itself seized in 2014. The pattern that followed, marketplace seizure, rapid successor emergence, and community migration, became the defining operational cycle of dark web markets for the decade that followed.
AlphaBay, Empire, Versus, Vice City, Marketplace History
Silk Road’s takedown didn’t shrink the dark web marketplace ecosystem. It expanded it. Each successive generation of markets grew larger, more sophisticated, and harder to dismantle than the last.
AlphaBay became the largest dark web marketplace in history before its coordinated international takedown in 2017, processing an estimated $600,000 to $800,000 in daily transactions at its peak. Its administrator, Alexandre Cazes, was arrested in Thailand and died in custody days later. AlphaBay was relaunched in 2021 by a surviving administrator and remains active, one of the few markets to survive a law enforcement operation and re-emerge.
Empire Market operated from 2018 to 2020 and became the dominant marketplace following AlphaBay’s original takedown, accumulating hundreds of thousands of users before its administrators conducted an exit scam in August 2020, disappearing with an estimated $30 million in user funds. The Empire’s collapse became one of the most studied examples of marketplace fraud in dark web history.
Versus Market ran from 2019 to 2022, positioning itself as a security-focused alternative with stricter vendor vetting. It voluntarily shut down after a critical vulnerability was discovered that could have exposed the server infrastructure to law enforcement.
Vice City Market emerged in the post-Empire landscape and operated as a mid-tier marketplace before going offline. Its significance lies less in scale than in pattern; it represents the continuous churn of dark web market infrastructure that threat intelligence platforms must track to maintain accurate coverage of where illicit activity migrates after each disruption.
BreachForums, BidenCash, Joker’s Stash, Cybercrime Forums Tracked by Threat Intel
While marketplaces dominate the public narrative around the dark web, the sites with the most direct relevance to corporate cybersecurity and data breach response are the forums and shops where stolen data is bought, sold, and leaked.
BreachForums emerged as the successor to RaidForums following its seizure in 2022 and quickly became the most prominent English-language data-leak forum on the dark web. It hosted some of the most significant breach disclosures of recent years, including the theft of databases from major corporations, government entities, and financial institutions. The platform has experienced multiple law enforcement actions, administrator arrests, and relaunches, each iteration drawing scrutiny from security researchers tracking where exfiltrated data surfaces after an incident.
BidenCash is a carding marketplace specializing in stolen payment card data. It became notable for its aggressive promotional tactic of releasing millions of stolen card records for free. This strategy generated significant visibility in the threat intelligence community and directly impacted financial institutions worldwide.
Joker’s Stash was, until its voluntary shutdown in early 2021, the largest and most established carding shop on the dark web, responsible for selling billions of stolen payment card records over its operational lifetime. Its closure was announced by its administrator and represented a rare example of a major dark web platform exiting on its own terms rather than via seizure.
These platforms are not historical footnotes. BreachForums and its successors remain active monitoring targets for any organization serious about understanding where their data goes after a breach.
Intel Exchange & Recon, Intelligence-Focused Resources
Not every notable dark web site is a marketplace or a leak forum. A smaller category of platforms serves the intelligence and research community directly, and two of the most referenced are Intel Exchange and Recon.
Intel Exchange is a dark web forum focused on the discussion and trade of intelligence, geopolitical, financial, and operational information shared among researchers, analysts, and, inevitably, threat actors. It occupies a grey zone: legitimate security researchers use it to track emerging threat narratives, while the same infrastructure hosts discussions that cross into operational planning for criminal activity.
Recon serves a more specific function within the dark web marketplace ecosystem. It aggregates vendor profiles across multiple marketplaces, allowing users to track vendor reputation, transaction history, and cross-platform activity. For threat intelligence analysts, Recon is a useful tool for mapping threat actor behavior across marketplace migrations, when a market goes offline, and vendors scatter to competitors. Recon provides continuity of identity tracking that individual marketplace profiles cannot.
The New York Times, WikiLeaks & Sci-Hub Onion Mirrors
Among the most legitimately significant dark web links are the .onion mirrors of major surface web organizations, platforms that maintain a Tor presence specifically to serve users in censored or surveilled environments.
The New York Times launched its .onion mirror in 2017, making it one of the first major news organizations to do so. The explicit purpose was accessibility: in countries where the NYT is blocked or where reading Western journalism carries legal risk, the .onion address allows readers to access content without exposing their identity or location to state surveillance.
WikiLeaks has maintained a dark web presence since its early years, using .onion infrastructure to both securely receive leaked documents through its SecureDrop-style submission system and ensure its published archive remains accessible regardless of surface web domain seizures or blocks.
Sci-Hub, the academic paper repository that operates in direct conflict with academic publisher copyright enforcement, maintains .onion mirrors as a resilience measure against the domain seizures that have repeatedly taken its surface web addresses offline. For researchers in countries without institutional journal access, the Sci-Hub onion address is a functional academic resource, one of the clearer examples of the dark web serving a purpose that has nothing to do with criminality.
Z-Library’s Dark Web Presence
Z-Library, the world’s largest shadow library of books and academic papers, has one of the more instructive dark web histories among legitimate-use platforms. Following the seizure of its surface web domains by U.S. authorities in November 2022 and the arrest of two alleged administrators, Z-Library migrated its primary access model to the Tor network and introduced personalized .onion addresses for registered users.
The personalized address model is notable from a security architecture perspective. Rather than a single .onion link for all users, Z-Library generates a unique .onion address per account, making bulk blocking significantly more difficult and ensuring that a single domain seizure cannot take the entire service offline.
Z-Library’s dark web pivot illustrates a broader pattern: platforms under legal pressure increasingly use .onion infrastructure not because their content is inherently criminal, but because the dark web’s architecture provides resilience against domain-level enforcement actions that are straightforward to execute on the surface web.
Dark Web Links on Telegram, What’s Real and What’s a Scam
Search for dark web links on Telegram, and you’ll find thousands of results, channels claiming to offer exclusive .onion directories, groups promising access to hidden marketplaces, and bots generating fresh dark web links on demand. The volume is striking. The legitimacy is not.

Telegram has become one of the most heavily exploited platforms for dark web-adjacent fraud, and understanding why requires understanding the gap between what Telegram actually is and what these channels claim to offer.
Why Telegram Dark Web Groups Are Mostly Scams
Telegram is a surface web messaging application. It operates on conventional internet infrastructure, uses standard domain resolution, and has no architectural connection to the Tor network. A Telegram channel cannot host a dark website, generate valid .onion addresses, or provide access to anything that doesn’t already exist independently on the Tor network.
What Telegram dark web groups actually provide, almost universally, is one of three things: recycled link lists copied from public directories and repackaged as exclusive content, phishing links disguised as .onion addresses that redirect victims to credential-harvesting pages, or upfront payment demands for “verified” dark web access that deliver nothing.
The scam mechanics are straightforward and effective because they exploit a genuine information gap. Most people searching for dark web links have limited experience with how .onion infrastructure actually works. They don’t know that legitimate dark web resources don’t require a Telegram subscription to access, that no Telegram bot can generate valid .onion addresses, or that any channel demanding payment before sharing links is, by definition, a fraud.
The scale of this ecosystem is significant. Thousands of Telegram channels operate simultaneously under variations of the same premise, cycling through new account names as old ones get reported and removed. The barrier to entry is nearly zero; a Telegram account, a recycled link list, and a convincing channel description are all that’s required to run this operation indefinitely.
How Threat Actors Use Telegram to Distribute Links
The relationship between Telegram and the dark web isn’t entirely fraudulent. Legitimate threat actors, ransomware groups, data brokers, and initial access sellers do use Telegram as a communication and distribution channel, but in ways that are meaningfully different from the scam channels described above.
For established threat actors, Telegram serves as a surface-web-accessible announcement layer. Ransomware groups post victim notifications. Data brokers advertise freshly exfiltrated databases. Initial access brokers list compromised network credentials available for purchase. The actual transactions and the bulk of the operational infrastructure remain on .onion sites. Still, Telegram’s reach, speed, and relative tolerance for this content, compared to more moderated platforms, make it useful for audience building and deal initiation.
Leak channels operated by threat groups have become particularly significant from an intelligence perspective. When a major organization is breached, the first public disclosure frequently appears not on a dark web forum but on a Telegram channel operated by the threat actor or affiliated with the ransomware group responsible. These announcements serve multiple purposes simultaneously: they pressure victims into paying ransoms, they attract buyers for the stolen data, and they build the threat actor’s reputation within the broader criminal ecosystem.
The critical distinction is that these channels are operated by known, tracked threat actors with established reputations, not anonymous accounts claiming to sell dark web access for a few dollars. Identifying and monitoring this category of Telegram activity is a core function of modern threat intelligence operations.
How DeXpose Monitors Telegram Channels for Leaked Data
The same properties that make Telegram attractive to threat actors, speed, reach, and relatively low moderation overhead, make it a high-priority monitoring surface for threat intelligence platforms.
DeXpose continuously monitors Telegram channels, groups, and bots where leaked data, breach announcements, and stolen credential sets are known to surface. This isn’t passive observation. When a threat actor posts a sample database to validate a breach claim, when a ransomware group announces a new victim, or when a data broker lists credentials from a specific industry vertical, DeXpose’s monitoring infrastructure captures that activity and cross-references it against client data to determine whether any exposed records belong to monitored organizations or individuals.
This matters because the timeline between a breach occurring and the data appearing publicly on Telegram is often measured in hours, not weeks. Organizations that rely solely on dark web forum monitoring miss a growing proportion of initial breach disclosures, which now occur on surface-accessible platforms like Telegram before migrating deeper into dark web infrastructure.
For businesses that want to understand their real-time exposure across both dark web and Telegram-based threat actor activity, DeXpose’s monitoring covers both layers, because in 2026, the line between where the dark web ends and where surface platforms begin has never been more deliberately blurred by the people exploiting both.
Are Dark Web Links Dangerous? Risks You Need to Understand
The honest answer is: it depends entirely on what you access, how you access it, and what you do afterward. The dark web itself is not inherently illegal. The Tor network was built by the U.S. government, is used by journalists and activists worldwide, and hosts legitimate privacy infrastructure alongside everything else. But the risk profile of navigating dark web links is meaningfully different from anything on the surface web, and underestimating it has consequences that range from device compromise to criminal prosecution.

Legal Risks of Visiting Dark Web Sites
In most Western jurisdictions, using the Tor Browser and visiting .onion sites is not illegal. Accessing the dark web carries no criminal penalty in the United States, the United Kingdom, the European Union, or most of their peer nations. What becomes illegal, quickly and seriously, is what you do once you’re there.
Purchasing controlled substances, accessing child sexual abuse material, buying stolen financial data, commissioning fraudulent documents, or engaging with sanctioned entities through dark web marketplaces are all criminal acts regardless of the infrastructure used to facilitate them. The dark web doesn’t create a legal exemption. It creates an anonymity layer that some users mistake for one.
The legal complexity increases significantly outside Western jurisdictions. In countries including China, Russia, Belarus, Turkey, and several Gulf states, using Tor itself is either heavily restricted or explicitly illegal, independent of what sites are accessed. Researchers and journalists operating in these environments face legal exposure simply from running the browser.
For corporate security teams conducting threat intelligence research on dark web links, the legal risk extends into a different domain: depending on jurisdiction, accessing certain cybercrime forums or downloading samples of leaked data, even for defensive research purposes, can create liability under computer fraud statutes that don’t distinguish intent as clearly as researchers would prefer. Legal guidance specific to your jurisdiction and use case is not optional in this context.
Malware, Phishing, and Fake Onion Links
If legal risk is the slow threat, technical compromise is the immediate one. The dark web’s anonymity architecture protects malicious operators just as effectively as it protects legitimate users, and the ecosystem reflects that symmetry.
Malware distribution through dark web links is endemic. Executable files, documents, and even images hosted on .onion sites can carry payloads designed to survive the Tor environment and execute on the host machine. The most common delivery mechanisms are fake software downloads, cracked application archives, and document files that exploit viewer vulnerabilities. The Tor Browser’s “Safest” security setting, which disables JavaScript and blocks most active content, eliminates a significant portion of browser-based attack vectors. Still, it doesn’t address files that a user deliberately downloads and opens.
Phishing via fake .onion addresses is arguably more dangerous than conventional phishing because the addresses themselves are so difficult to verify by memory. Fraudulent clones of well-known dark web sites, marketplaces, forums, and exchange services are built to be visually indistinguishable from their legitimate counterparts. A user who bookmarks what they believe is a legitimate .onion address and then returns to find a slightly different URL has likely been redirected to a credential-harvesting operation. This technique, known as address spoofing, is particularly effective against users who don’t cross-reference addresses against multiple verified sources before each visit.
Exit node attacks represent a more sophisticated technical risk. Because Tor traffic must eventually exit the relay network to reach its destination, a malicious exit node operator can intercept unencrypted traffic, a risk that primarily affects surface web browsing through Tor but also affects any .onion connection that doesn’t enforce end-to-end encryption independently.
How Law Enforcement Tracks Dark Web Activity
The persistent myth that the dark web is untraceable has been comprehensively disproven by a decade of successful law enforcement operations. Tor provides strong anonymity under normal conditions, but it has well-documented weaknesses, and law enforcement agencies across multiple jurisdictions have developed sophisticated methods to exploit them.
Traffic correlation attacks are the most technically significant. By monitoring traffic at sufficient points across the Tor relay network, an observer can statistically correlate the timing and volume of traffic entering and exiting the network to de-anonymize specific users. This technique requires substantial surveillance infrastructure, but nation-state law enforcement agencies and intelligence services have demonstrated the capability to deploy it effectively.
Operational security failures, not cryptographic weaknesses, are responsible for the majority of dark web arrests. Ross Ulbricht was identified partly through forum posts he made before Silk Road launched, in which he used his real email address. AlphaBay’s administrator left his personal email address in a server configuration file. These are not sophisticated attacks. They are basic failures of identity discipline that Tor’s architecture cannot compensate for.
Undercover operations and confidential informants remain as effective on the dark web as anywhere else. Law enforcement agencies have successfully infiltrated dark web forums, operated as vendors on major marketplaces, and used seized administrator accounts to gather evidence against platform users. The anonymity of a .onion address does not protect against a compromised human in your supply chain.
Cryptocurrency tracing has also matured significantly. The assumption that Bitcoin transactions on dark web marketplaces were untraceable proved incorrect as blockchain analytics firms developed increasingly sophisticated chain analysis tools. Multiple major dark web prosecutions have relied heavily on cryptocurrency transaction mapping to connect pseudonymous wallet addresses to real identities.
What Happens When Your Data Appears on a Dark Web Link
For most people and organizations, the dangers of the dark web are not encountered by visiting it. It’s something that arrives without warning when their data surfaces.
When a company is breached, the exfiltrated data follows a predictable path. It typically appears first in private channels, is sold to a small number of buyers, or is held for ransom negotiation. If ransom negotiations fail, or if the data’s value is better served by public release, it migrates to dark web forums, leak sites, or Telegram channels where it becomes accessible to a much wider audience. From there, credentials get tested against live services in automated stuffing attacks, financial data moves into carding markets, and personal information gets packaged into identity fraud kits.
The window between a breach occurring and the data being actively exploited is often measured in days. Organizations that discover their data on a dark web link after the fact, through a news report or a user complaint, have typically already missed the period when rapid response could have meaningfully limited the damage.
This is the practical argument for continuous dark web monitoring rather than reactive breach response. Knowing that your organization’s credentials, customer data, or internal documents have appeared on a dark web link within hours of that appearance, rather than weeks or months later, is the difference between containing an incident and managing its aftermath. Running a free dark web report through DeXpose takes minutes and surfaces exposure that most organizations don’t know exists until it’s already been exploited.
How DeXpose Monitors Dark Web Links for Your Protection
Understanding the dark web’s infrastructure is one thing. Having the capability to continuously monitor it at scale across thousands of .onion sites, forums, marketplaces, and Telegram channels simultaneously is an entirely different operational challenge. It’s the gap between knowing the threat exists and knowing the moment it touches you.

DeXpose was built specifically to close that gap.
How Our Crawlers Index Dark Web Sources Continuously
The dark web doesn’t have a Google. There is no single index, no unified crawl schedule, and no notification system that alerts you when your data appears somewhere it shouldn’t. Building meaningful coverage requires purpose-built infrastructure that operates inside the Tor network itself, not scrapers querying surface-web proxies, but active crawlers navigating .onion infrastructure the same way a human researcher would, at a scale and speed no human team could sustain.
DeXpose’s crawling infrastructure continuously indexes dark web forums, data leak sites, paste services, ransomware group blogs, carding markets, and the broader ecosystem of hidden services where stolen data circulates. This isn’t a static database updated periodically. It’s a live monitoring operation that tracks new posts, new leak publications, new forum threads, and new marketplace listings as they appear, because in threat intelligence, information value degrades rapidly over time.
The technical challenge isn’t simply reaching these sites. It’s maintaining coverage as the landscape shifts. Dark web links change. Sites go offline and re-emerge under new addresses. Forums migrate after law enforcement actions. Ransomware groups rebrand. DeXpose’s infrastructure is built to track these migrations, correlate identities across platform changes, and maintain coverage continuity even as the underlying addresses constantly evolve.
What We Look For: Breached Credentials, Leaked Documents, Brand Mentions
Dark web monitoring is only as useful as the specificity of what’s being monitored. Generic crawling produces noise. Targeted monitoring produces intelligence.
DeXpose monitors for three primary categories of exposure, each with direct implications for organizational security.
Breached credentials are the most immediately actionable. When employee email addresses, passwords, or session tokens surface in a dark web dump, whether from a direct breach of your organization or from a third-party service your employees use, the window between that appearance and an active account takeover attempt is often measured in hours. DeXpose identifies credential exposure at the point of appearance, not after the attack has already succeeded.
Leaked documents and data fall under the broader category of sensitive organizational information: internal communications, financial records, customer databases, intellectual property, and source code that appear on dark web leak sites or in forum posts. Ransomware groups routinely publish partial data samples as leverage in negotiations before releasing full datasets publicly. Identifying your organization’s data in these early-stage publications is critical to response timing.
Brand mentions and infrastructure references capture a different category of risk, the early indicators of a planned attack rather than a completed one. When threat actors discuss targeting a specific organization, when phishing kits impersonating your brand are for sale, or when your domain infrastructure is referenced in initial access broker listings, that intelligence has significant value before any breach occurs. DeXpose monitors for these signals across dark web forums and Telegram channels where attack planning activity is most visible.
Run a Free Dark Web Report, Check If Your Data Is Exposed
Most organizations discover their dark web exposure one of two ways: through a third-party notification after the damage is done, or through a proactive check that surfaces what’s already out there. The second option is available right now, at no cost.
DeXpose’s Free Dark Web Report scans across indexed dark web sources and returns a clear picture of what’s currently exposed and where. It takes minutes to run and consistently surfaces credential exposure, leaked records, and data appearances that organizations had no prior awareness of, not because the data wasn’t there, but because no one had looked.
For individuals, the Email Data Breach Scan provides the same visibility at the personal level, checking whether your email address and associated credentials have appeared in known breach datasets currently circulating on dark web markets and forums.
If your organization has specific Oracle infrastructure, the Oracle Breach Check provides targeted scanning against the Oracle-related breach data that has been particularly active across dark web sources in recent cycles.
These aren’t marketing exercises. They’re starting points for understanding an existing exposure profile, whether you’ve checked for it or not.
Dark Web Monitoring for Businesses and MSPs
For organizations that need continuous monitoring rather than a one-time check, DeXpose’s core Dark Web Monitoring service provides ongoing coverage across the full landscape of dark web sources, with alerting, reporting, and the contextual intelligence needed to act on what’s found rather than simply knowing it exists.
Beyond credential and data monitoring, DeXpose’s Brand Protection service extends coverage to the indicators that precede breaches: phishing infrastructure, impersonation campaigns, and dark web discussions referencing your organization’s assets before an attack is executed.
For Managed Service Providers, DeXpose’s MSP Partnership Program is built around the operational reality of managing dark web monitoring across multiple client environments simultaneously. Rather than running separate monitoring operations per client, MSP partners access a unified platform with the depth of coverage and alerting infrastructure to deliver dark web intelligence as a managed service, with a margin structure that makes it commercially viable.
The dark web monitoring landscape has matured significantly. The question for most organizations is no longer whether continuous monitoring is necessary; it is whether they can afford it. It’s whether the platform doing it has the coverage, infrastructure, and depth of intelligence to be genuinely useful when something surfaces, or whether it’s simply checking a compliance box. DeXpose is built for the former.
Frequently Asked Questions (FAQ’s)
What Is the Most Popular Dark Web Link Directory in 2026?
The Hidden Wiki remains the most widely referenced dark web link directory, though its many unofficial forks make reliability inconsistent. For curated, verified listings, Daniel’s Onion Link List is the most trusted, actively maintained directory, with real-time uptime indicators for each listed .onion address.
Are There Working Dark Web Links in 2026?
Yes, many legitimate .onion sites remain active and accessible through the Tor Browser in 2026. However, link rot is endemic to the dark web, meaning any static list of addresses can become outdated within weeks as sites migrate, go offline, or are seized by law enforcement.
How Do I Find Verified Dark Web Links?
The most reliable method is cross-referencing an address across multiple independent sources, dark web search engines like Ahmia, curated directories like Daniel’s list, and established community forums like Dread. Any link that appears only once, especially via Telegram or unsolicited messages, should be treated as unverified.
Is It Illegal to Visit Dark Web Links?
In most Western countries, accessing the dark web through the Tor Browser is entirely legal. What becomes illegal is the content you interact with, purchasing illicit goods, accessing prohibited material, or engaging with sanctioned entities, which are criminal acts regardless of the network used to reach them.
What’s the Difference Between Tor Links and Regular Dark Web Links?
They refer to the same thing. Dark web links are .onion addresses that resolve exclusively within the Tor network; “Tor links” is simply another way of describing them. Both terms refer to hidden services hosted on the Tor infrastructure, accessible only through a Tor browser or a conventional DNS system.
Why Do So Many Dark Web Links Stop Working?
Dark websites have no hosting obligations, no domain registrars, and no forwarding infrastructure; they can disappear without notice due to law enforcement seizures, administrator exit scams, voluntary shutdowns, or simple server abandonment. Operators also frequently rotate .onion addresses as a security measure, making previously saved links permanently unreachable.
Can I Access Dark Web Links on Mobile?
Yes. Android users can access .onion links through the official Tor Browser for Android or via Orbot. iPhone users can use Onion Browser, endorsed by the Tor Project, though iOS restrictions limit full Tor integration compared to desktop or Android. For sensitive research, mobile access is generally considered less secure than a dedicated desktop environment running the full Tor Browser.