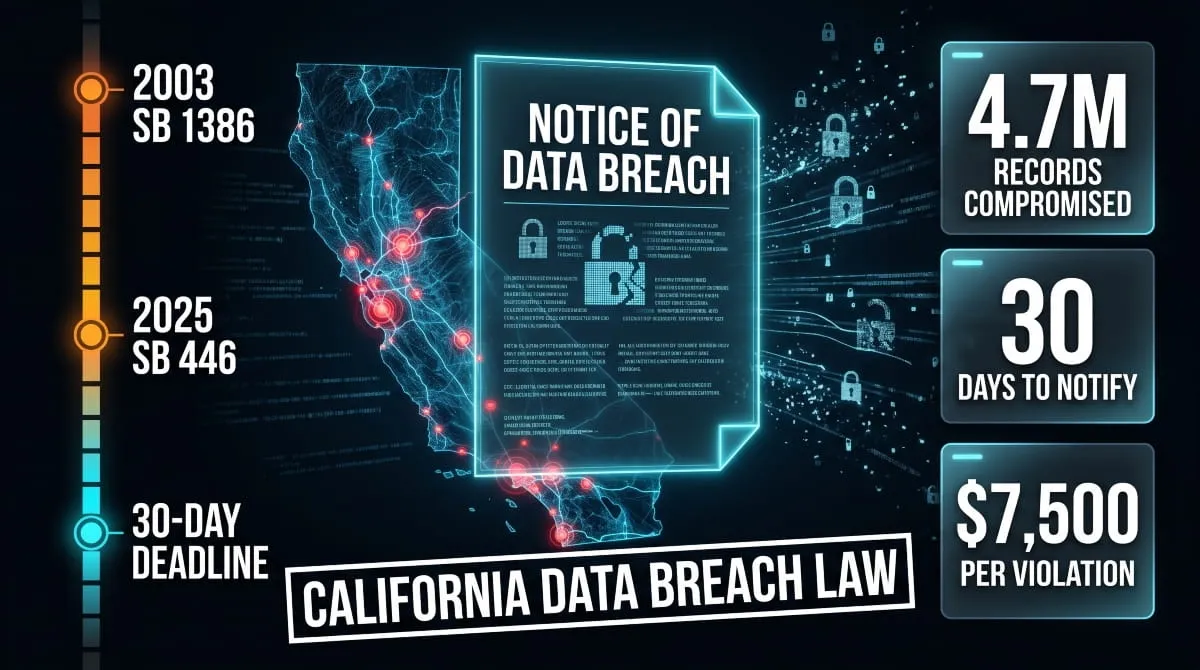
California was the first state in the nation to require businesses to notify consumers when their personal information was compromised. That was 2003. Two decades later, the law has grown sharper, stricter, and significantly more consequential, and in 2025, it got its most important update yet.
Today, the California data breach notification law, codified under Civil Code 1798.82, sets the legal standard for how organizations must respond when a breach occurs. It defines what counts as a breach, who must be notified, what the notification must say, and now, exactly how fast it must happen.
For businesses operating in California, or holding data on California residents anywhere in the world, this law is not optional, not negotiable, and not forgiving of delays.
The stakes have never been higher. A single breach event can expose millions of records, trigger regulatory enforcement, and land an organization on the California Department of Justice’s public breach list. The 2025 passage of SB 446 introduced a firm 30-day notification deadline, replacing the previous “expedient” standard that many organizations quietly stretched into months.
This guide covers everything you need to know: what the law requires, what changed in 2025 and what’s ahead in 2026, how real California breaches were handled, and what your organization should be doing right now, before a breach forces the question.
What Is the California Data Breach Notification Law?
The California data breach notification law is a state statute that requires any person or organization, public or private, to notify California residents when their unencrypted personal information has been acquired, or is reasonably believed to have been acquired, by an unauthorized party. At its core, it is a transparency law: it exists to ensure that individuals know when their data has been compromised, so they can take action to protect themselves.
The law is primarily governed by Civil Code 1798.82, which applies to businesses, and its companion provision Civil Code 1798.29, which applies to government agencies. Together, they form the foundation of California’s data breach notification framework, one of the most comprehensive and frequently cited breach laws in the United States.
California Civil Code 1798.82, Full Text Summary
Civil Code 1798.82 requires any business that owns, licenses, or maintains personal information about California residents to disclose a security breach to those residents in the most expedient time possible, and under the 2025 amendment, within 30 days of discovering the breach.
The statute defines personal information broadly. It covers names combined with Social Security numbers, driver’s license or state ID numbers, financial account information, medical and health insurance information, login credentials, and biometric data, among others. Encrypted data that is compromised alongside the encryption key is also covered.
The notification must be written in plain language, identify the type of information breached, describe what happened and when, explain what the business is doing in response, and provide contact information for affected individuals to ask questions. If the breach affects more than 500 California residents, the business must also submit a copy of the notification to the California Attorney General’s office.
History: From SB 1386 (2003) to SB 446 (2025)
California’s breach notification law didn’t emerge from a vacuum; it was a direct response to a growing crisis. In 2002, the California Legislature passed SB 1386, which took effect in July 2003 and made California the first state in the country to mandate data breach notifications. At the time, no federal equivalent existed. The law was groundbreaking.
Over the following two decades, the Legislature steadily strengthened it. The definition of personal information was expanded multiple times to reflect the evolving digital landscape, adding medical records, biometric data, and login credentials as these categories became increasingly targeted by attackers. Notification requirements became more specific, and the rights of affected individuals were reinforced.
The most significant update came in 2025 with the passage of SB 446. Before SB 446, the law required notification “in the most expedient time possible and without unreasonable delay”, language that was deliberately vague and routinely exploited. Organizations would take 60, 90, even 120 days to notify affected residents, often citing ongoing investigations. SB 446 ended that ambiguity by setting a hard 30-day deadline from the date of discovery. The clock now starts the moment a breach is known.
What Counts as a “Data Breach” Under California Law
Under California law, a breach is defined as the unauthorized acquisition of computerized data that compromises the security, confidentiality, or integrity of personal information. The keyword is unauthorized. If someone who had no right to access the data obtained it, that is a breach, regardless of whether they used it.
Not every security incident triggers notification obligations. If the compromised data was encrypted and the encryption key was not also exposed, notification may not be required. Similarly, good-faith access by an employee or agent of the organization, where the data is not further disclosed, may not constitute a breach under the statute.
What consistently triggers the law: ransomware attacks that exfiltrate data, phishing campaigns that harvest login credentials, unauthorized third-party database access, and accidental public exposure of files containing personal information. In practice, if there is any reasonable belief that personal data was accessed without authorization, the notification process should begin.
Who Must Comply, Businesses, Government, Nonprofits
The California data breach notification law applies broadly. Any business, regardless of size or industry, that owns, licenses, or simply maintains personal information about California residents is covered. This includes companies headquartered outside California. If your database contains the personal information of even one California resident, you fall within the law’s jurisdiction.
Government agencies at the state and local level are covered under the companion statute, Civil Code 1798.29, which mirrors the requirements of 1798.82. Healthcare organizations must comply with both California’s breach law and federal HIPAA requirements, and where the two conflict, the stricter standard applies, which is frequently California’s.
Nonprofits, educational institutions, financial services firms, and technology companies are all subject to the same obligations. There is no small-business exemption. There is no industry carve-out. If you hold California residents’ personal data, you are accountable under the law.
What the Law Requires, Notification Obligations Explained
Knowing a breach occurred is only the beginning. What follows is a defined legal process, and under California law, how you execute that process matters as much as the fact that you execute it at all. Civil Code 1798.82 doesn’t just say “tell people.” It specifies who gets told, what they’re told, and how the notification must be structured. Getting any part of this wrong exposes an organization to regulatory scrutiny and civil liability.

What Personal Information Is Protected
California’s breach notification law protects personal information defined as a combination of an individual’s first name (or first initial) and last name, paired with one or more of the following data elements, when either the name or the data element is unencrypted:
- Social Security number
- Driver’s license or California ID card number
- Financial account, credit, or debit card number combined with any required security code or password
- Medical information or health insurance information
- Username or email address combined with a password or the answer to a security question
- Biometric data
- Tax identification number, passport number, or military ID number
- Unique identifiers used to authenticate an individual
California law also covers a standalone category: login credentials for an online account belonging to a California resident, even without a name attached, are protected if compromised. This reflects the modern reality that credential theft is one of the most common and damaging breach types.
Who Must Be Notified
When a breach triggers notification obligations, two parties must be informed: the affected individuals and, in larger breaches, the California Attorney General’s office.
Every California resident whose unencrypted personal information was, or is reasonably believed to have been, acquired by an unauthorized person must receive direct notification. This means individual written notice, either by mail, email (if the affected person has consented to electronic communication), or through a substitute method if direct contact is impossible.
Substitute notice is permitted only when the cost of direct notification exceeds $250,000, the number of affected individuals exceeds 500,000, or the organization simply doesn’t have sufficient contact information. In those cases, the organization must post a conspicuous notice on its website and notify major statewide media.
When a single breach affects more than 500 California residents, the organization must also submit a sample copy of the breach notification to the California Attorney General. This requirement feeds the DOJ’s public breach database, a searchable record that journalists, regulators, and researchers actively monitor. Being listed there carries reputational consequences well beyond the legal obligation itself.
What a Compliant Breach Notification Letter Must Include
California law is specific about what a breach notification must contain. A letter that omits required elements is not a compliant notification, and a non-compliant notification is treated the same as no notification at all. Under Civil Code 1798.82, a proper notification must include:
- The name and contact information of the reporting business
- A list of the types of personal information that were, or are reasonably believed to have been, breached
- The date or estimated date range of the breach, if known
- Whether notification was delayed at the request of law enforcement
- A general description of the breach incident
- The toll-free numbers and addresses of the major credit reporting agencies, if the breach involved Social Security numbers or financial account information
- Guidance on what affected individuals can do to protect themselves.
The notification must be written in plain language. California law explicitly prohibits burying critical disclosures in legal jargon or making the nature of the breach difficult to understand. The title or subject line must include the words “Notice of Data Breach”; this is a statutory requirement, not a stylistic suggestion.
California Data Breach Notification Letter, Sample Template
The following is a compliant template structure aligned with the requirements of Civil Code 1798.82. Organizations should have legal counsel review any notification before it is sent.
NOTICE OF DATA BREACH What Happened On [date or approximate date range]? We discovered that [brief, plain-language description of the incident, e.g., an unauthorized party gained access to our systems and may have accessed certain customer records]. What Information Was Involved The information involved may include: [list specific categories, e.g., names, Social Security numbers, financial account information]. What We Are Doing: We have taken the following steps in response: [describe containment measures, security improvements, and law enforcement involvement, if applicable]. What You Can Do: We recommend that you [place a fraud alert or credit freeze, monitor your accounts, consider identity theft protection services]. You may contact the major credit reporting agencies at:
-
Equifax: 1-800-685-1111
-
Experian: 1-888-397-3742
-
TransUnion: 1-888-909-8872
For More Information: If you have any questions, please get in touch with us at [toll-free number/email/mailing address]. [Company Name] [Date of Notice]
This structure satisfies California’s statutory requirements. However, if the breach also triggers HIPAA notification obligations, as it would for healthcare organizations, additional federal disclosure requirements apply and must be layered in accordingly.
California’s 30-Day Data Breach Notification Deadline (2025–2026 Law Update)
For years, California’s breach notification law carried a standard that sounded rigorous but functioned as a loophole: notify affected individuals “in the most expedient time possible and without unreasonable delay.” In practice, that language gave organizations enormous flexibility, and many used it. Notifications that arrived 60, 90, or even 120 days after a breach was discovered were common. Affected individuals spent months unaware that their data was circulating on dark web forums, being sold in credential marketplaces, or used to open fraudulent accounts in their name.

SB 446 closed that loophole. Effective in 2025, California now operates under one of the strictest breach notification timelines in the country.
What SB 446 Changed: The New 30-Day Rule
SB 446 amended Civil Code 1798.82 to establish a hard 30-calendar-day deadline for breach notifications. From the moment an organization discovers, or reasonably should have discovered, that a breach occurred, the clock is running. Thirty days to investigate, draft, review, and deliver notification to every affected California resident.
The law does not distinguish between small breaches and large ones. A breach affecting 50 records carries the same 30-day obligation as one affecting 5 million. The only recognized exception is a formal, documented request from law enforcement to delay notification because it would impede an active criminal investigation. Even then, the delay is not indefinite, notification must proceed as soon as law enforcement confirms it will not compromise the investigation.
This amendment reflects a broader legislative philosophy: the harm caused by delayed notification is not hypothetical. Every day an affected individual goes uninformed is another day their compromised credentials can be weaponized.
When the Clock Starts: Discovery vs. Occurrence
One of the most consequential, and frequently misunderstood, aspects of the 30-day rule is precisely when it begins. The deadline is triggered by discovery, not by the date the breach actually occurred.
These two dates are often weeks or months apart. The average organization takes considerably longer than 30 days just to detect that a breach has happened, let alone investigate its scope. Under California law, the notification clock starts when the organization knew or reasonably should have known about the breach, meaning willful ignorance or inadequate detection infrastructure does not pause the timer.
In practical terms, this means organizations that lack real-time monitoring, dark web surveillance, or rapid incident response capabilities face a compounding problem: they may already be behind before they even know there is a problem. The 30-day window is not generous when factored against the time needed to contain the incident, assess what data was affected, identify all impacted individuals, draft a compliant notification, and obtain legal review.
Previous Timeframe vs. Current Requirements
Before SB 446, California’s notification standard was deliberately flexible. The “most expedient time possible” language was borrowed from early breach notification frameworks that predated the modern threat landscape, a time when breaches were relatively rare, typically involved physical records, and affected far fewer individuals.
As the volume and velocity of cyberattacks accelerated, that flexibility became a liability for consumers rather than a protection. Studies consistently showed that organizations were taking an average of 60 to 80 days to notify affected individuals, and in some high-profile cases, significantly longer. During that window, compromised data was actively traded, and victims had no opportunity to protect themselves.
The 30-day rule represents a fundamental shift in how California balances organizational convenience and consumer protection. The Legislature’s message is clear: the burden of speed falls on the organization that failed to protect the data, not on the individual whose data was exposed.
Consequences of Missing the Notification Deadline
Failing to notify within 30 days is not a technical violation that regulators look past. Under California law, any business that fails to comply with Civil Code 1798.82 can be sued by the California Attorney General, a district attorney, a city attorney, or a county counsel. Civil penalties can reach $2,500 per violation for unintentional noncompliance and $7,500 per violation for intentional noncompliance, and each affected individual can constitute a separate violation.
Beyond regulatory penalties, affected individuals have a private right of action. They can sue directly for damages resulting from the failure to notify, including costs associated with identity theft, credit monitoring, and financial losses tied to the breach. Class action exposure in large breaches can be substantial.
The reputational consequences are equally significant. Every breach affecting more than 500 California residents is submitted to the California DOJ and added to its publicly accessible breach database. That record is permanent, searchable, and routinely referenced by journalists, regulators, insurers, and enterprise procurement teams evaluating vendor risk. Missing the 30-day deadline doesn’t just create legal exposure, it signals to the market that an organization’s incident response is inadequate.
California Data Breach Law Penalties & Enforcement
Compliance with California’s data breach notification law is not self-enforcing; it is backed by a layered enforcement structure that combines regulatory authority, private litigation rights, and public accountability mechanisms. Organizations that treat notification obligations as optional or consistently delay beyond the statutory deadline face consequences that compound quickly across multiple fronts simultaneously.

Civil Penalties Under Civil Code 1798.82
California’s breach notification law does not set a flat fine for non-compliance. Instead, it operates on a per-violation model, where each affected individual can constitute a separate violation. This structure makes the financial exposure in large-scale breaches enormous.
For unintentional violations, where an organization failed to notify through negligence or oversight rather than deliberate intent, civil penalties reach up to $2,500 per violation. For intentional violations, that ceiling rises to $7,500 per violation. A breach affecting 100,000 California residents that goes unnotified, or is notified far outside the 30-day window, can generate liability in the hundreds of millions of dollars before a single private lawsuit is filed.
California’s courts assess penalties following enforcement actions brought by the Attorney General or local prosecutors. Courts also have the authority to issue injunctive relief, compelling organizations to overhaul their security practices, notification procedures, or both. In cases involving particularly egregious failures, courts can order additional remedies beyond financial penalties.
California AG & DOJ Enforcement Actions
The California Attorney General is the primary enforcement authority for Civil Code 1798.82. The AG’s office actively monitors the breach notification database, investigates complaints from affected individuals, and initiates enforcement actions against organizations that fail to meet their obligations, either by not notifying at all, notifying too late, or submitting notifications that don’t meet the statutory content requirements.
The California DOJ maintains a public breach database that logs all notifications involving more than 500 residents and makes them permanently accessible. This database serves a dual function: it creates public accountability for breached organizations. It provides the AG’s office with a running record to identify patterns of non-compliance across industries and entities.
Enforcement actions by the AG’s office have targeted organizations across healthcare, retail, financial services, and government. The office has also used its authority to issue guidance documents, including model notification language and compliance recommendations, that effectively set the practical standard for a compliant response. Deviation from that standard, when an enforcement action follows, is difficult to defend.
Private Right of Action: Can Individuals Sue?
Yes, and this is one of the features that makes California’s data breach law distinctly powerful compared to breach notification statutes in other states. Civil Code 1798.82 grants affected individuals the right to bring a private civil lawsuit against an organization that fails to comply with notification requirements.
Plaintiffs in these cases can seek actual damages, meaning documented financial harm caused by the failure to notify, such as identity theft losses, fraudulent charges, or costs associated with credit monitoring and remediation. Where actual damages are difficult to quantify, California courts have recognized the right to seek statutory damages in certain circumstances.
The private right of action creates meaningful exposure to class actions. In breaches affecting large numbers of California residents, plaintiff attorneys routinely aggregate individual claims into class actions that dramatically amplify the financial stakes. Organizations that delayed notification, sent non-compliant letters, or failed to report to the AG’s office as required have all faced class action litigation on these grounds.
This means that for any breach involving California residents, legal exposure doesn’t end with the AG’s office. It extends to every individual whose data was compromised and who can demonstrate harm resulting from inadequate or untimely notification.
HIPAA + California Law: Dual Compliance Requirements
Healthcare organizations operating in California face a more complex compliance landscape than most. They must simultaneously satisfy federal requirements under HIPAA’s Breach Notification Rule and California’s requirements under Civil Code 1798.82, and the two frameworks, while aligned in spirit, differ in meaningful ways.
HIPAA requires covered entities to notify affected individuals within 60 days of discovering a breach of unsecured protected health information. California’s updated law now requires notification within 30 days. When both apply, as they do for any HIPAA-covered entity holding data on California residents, the stricter standard governs. That means California’s 30-day deadline effectively supersedes HIPAA’s 60-day window for California residents.
The content requirements also differ. HIPAA notifications must include specific elements not required under California law. At the same time, California’s statute mandates certain disclosures, including credit reporting agency contact information in the event of a financial breach, that HIPAA does not address. A fully compliant dual notification must satisfy both checklists simultaneously.
For healthcare organizations, this dual obligation reinforces the need for breach response protocols built to California’s standards, not HIPAA’s. Defaulting to the federal timeline is a compliance failure under state law, and California regulators have shown no reluctance to treat it as one.
Notable California Data Breaches & How They Were Handled
California’s breach notification law exists in theory, but these incidents show what it looks like in practice. The cases below represent some of the most significant data breaches affecting California residents and institutions in recent years. Each reveals something different about how organizations respond under pressure, where notification processes succeed or fail, and why the law’s enforcement mechanisms exist in the first place. Now I have everything needed to write this section with full factual accuracy. Here it is:

Blue Shield of California Data Breach (2025)
Blue Shield of California’s 2025 breach is the kind of incident that reframes how organizations think about data exposure. On February 11, 2025, Blue Shield discovered that Google Analytics had been configured to share member data with Google Ads for almost three years, from April 2021 to January 2024. No external hacker was involved. The exposure resulted from a misconfigured analytics tool that most large organizations use without a second thought.
Blue Shield confirmed the breach affected 4.7 million members, making it the largest healthcare data breach reported in the United States that year. The types of data potentially disclosed varied by individual but could have included patient names, insurance plan details, city and zip code, account identifiers, medical claims details, and patient financial responsibility.
Blue Shield posted its breach notice on April 9, 2025, and a class action lawsuit was filed the following day. The case highlights a compliance reality that many organizations overlook: a breach doesn’t require a sophisticated attacker. An unreviewed configuration setting can expose millions of records over years, with no one noticing until it’s too late.
The story didn’t end there. A separate incident was reported in February 2026, when Blue Shield’s vendor, Conduent Business Services, was hit by a cyberattack, with an unauthorized third party accessing its environment from October 2024 to January 2025 and obtaining Blue Shield-related files. Two major breach events in less than 18 months, both originating through third-party relationships, a pattern that has become one of the defining characteristics of modern data exposure.
California DMV Data Breach
The California DMV breach stemmed from a ransomware attack on Automatic Funds Transfer Services (AFTS), a Seattle-based contractor the DMV used to verify vehicle registration addresses. The attack may have compromised the last 20 months of California vehicle registration records, containing names, addresses, license plate numbers, and vehicle identification numbers.
The breach potentially affected all Californians who had registered a vehicle within the last 20 months, an estimated 38 million records. The DMV’s own systems were not directly compromised. The vulnerability existed entirely within a vendor’s infrastructure, one that had unfiltered access to a massive pool of government-held personal data.
The Cuba ransomware group was identified as the likely attacker, and the group stated it intended to sell the stolen data. The incident is a textbook illustration of supply chain risk: the DMV had no breach in its own systems, yet millions of California residents faced potential exposure because a contractor lacked adequate security controls.
Delta Dental of California Data Breach
With nearly 7 million dental plan members affected, the Delta Dental of California data breach stands as one of the largest healthcare-related MOVEit breaches ever reported, and it originated not from an attack on Delta Dental’s own infrastructure, but from a zero-day vulnerability in widely used third-party file transfer software.
Delta Dental learned about the compromise on June 1, 2023. Five days later, following an internal investigation, it confirmed that the Russia-linked Clop ransomware group had accessed and stolen data between May 27 and May 30, 2023, before a patch for the vulnerability had been applied. The stolen data included names, addresses, Social Security numbers, driver’s license numbers, financial account information, and health information.
The notification timeline became a significant point of legal scrutiny. Attorneys in multiple class action lawsuits argued that Delta Dental waited 5 months after discovering the incident to notify affected individuals, with breach notification letters not sent until December 15, 2023. This is precisely the delayed-notification pattern that California’s SB 446 was designed to prevent, and the Delta Dental case was among the high-profile incidents that informed the legislative push for a hard deadline.
University of California Data Breach
The University of California was caught in the same MOVEit wave. Delta Dental of California served as UC’s dental insurance carrier, and the breach compromised the personal identifying information of approximately 190,000 UC employees, retirees, and dependents, including names, addresses, Social Security numbers, dates of birth, and health information.
When UC was made aware of the breach in July 2023, it immediately partnered with Delta Dental to notify impacted employees and offered them two years of complimentary identity monitoring services. The UC case is notable because the university itself was entirely downstream from the breach, its data was exposed through its insurance carrier’s vendor, two layers removed from the institution whose community members were affected. This layered third-party exposure is increasingly the norm, underscoring why breach notification obligations extend to any entity that maintains personal data, not just those that directly manage it.
State Bar of California Data Breach
The State Bar of California’s breach was unusual in both its cause and its victims. The incident was not a malicious hack, instead, a previously unknown security vulnerability in the Tyler Technologies Odyssey case management portal allowed nonpublic records to be unintentionally swept up by a third-party website called judyrecords when it attempted to access public records.
The exposed records were particularly sensitive. They included confidential attorney discipline complaints, matters legally nonpublic under California law, and information about witnesses and individuals involved in closed investigations. Although the State Bar is not bound by California consumer privacy law, it voluntarily utilized the definition of personal information contained in Civil Code sections 1798.29 and 1798.82 to guide its review and notification process.
The case demonstrates a fundamental truth about data breach notification obligations: the spirit of California’s law extends beyond technical compliance. Even organizations not strictly bound by Civil Code 1798.82 face the same institutional and reputational obligations when personal information is exposed, and the State Bar’s decision to voluntarily apply the statutory framework reflects that reality.
California Department of Corrections Data Breach
In early 2022, the California Department of Corrections and Rehabilitation discovered a potential data breach following routine maintenance on one of its information systems. The breach potentially included medical information on everyone tested for COVID-19 by the department from June 2020 through January 2022, including staff, visitors, and others, as well as mental health information for the incarcerated population in the Mental Health Services Delivery System dating back to 2008.
The breach was reported as affecting 236,000 individuals, making it one of the largest HIPAA breaches ever reported by a state correctional facility. Critically, CDCR was unable to confirm whether any specific data had actually been accessed or exfiltrated, the breach was discovered during routine maintenance, and the investigation could not definitively determine the scope of unauthorized access.
A class action lawsuit was filed on behalf of affected individuals, and on April 25, 2025, a Sacramento state court gave final approval to a $1.8 million settlement. The CDCR case illustrates a compliance challenge that many organizations face. When a breach is discovered, but the extent of unauthorized access cannot be confirmed, California law still requires notification. Uncertainty is not an exemption.
PowerSchool Data Breach, California Impact
PowerSchool, headquartered in Folsom, California, is one of the largest providers of K–12 education software in North America. In December 2024, the company disclosed a cybersecurity breach that exposed personally identifiable information for millions of students and educators. According to court documents published in May 2025, the breach ultimately compromised the personal information of approximately 62 million individuals.
The breach stemmed from vulnerabilities in PowerSchool’s customer support portal, PowerSource, due to a lack of multifactor authentication. An attacker used a compromised employee’s password to gain access to privileged functions and millions of sensitive records. PowerSchool paid a ransom to the attacker, who provided a video allegedly showing the deletion of the stolen data, however, as recently as May 2025, attackers were sending extortion emails to schools that included samples of the stolen data.
The California Attorney General’s office issued guidelines for impacted families, including credit freezes and enrollment in PowerSchool’s free monitoring service. Class action lawsuits alleged that PowerSchool failed to provide timely notice to affected users, consequently preventing them from taking protective action. The PowerSchool breach is among the most consequential education-sector incidents in history, and its California connection makes it a landmark case for how the state’s notification law applies to edtech vendors handling children’s data.
California DOJ Data Breach List 2025, Full Overview
Every breach affecting more than 500 California residents must be reported to the California Attorney General’s office, and those reports are added to a publicly accessible database. The California DOJ’s breach list contains sample copies of breach notices sent to California residents, searchable by the organization that submitted the notification.
The list functions as a running historical record of breach notifications across industries, healthcare, retail, financial services, government, education, and technology. For 2025, the database reflects the combined impact of the MOVEit wave, healthcare tracking-pixel disclosures, ransomware campaigns targeting public-sector infrastructure, and supply-chain attacks on widely used software platforms.
For organizations, the database serves as a benchmark: it shows what a compliant notification looks like, how peers in the same industry have handled similar incidents, and, critically, which organizations are conspicuously absent from the list despite known breaches, a pattern that regulators actively monitor. For consumers and researchers, it remains one of the most comprehensive and transparent breach disclosure mechanisms in the country.
How to Respond to a Data Breach in California, Step-by-Step
When a breach occurs, the decisions made in the first 72 hours define everything that follows, the legal exposure, the regulatory response, and the reputational damage. California law doesn’t just require notification; it requires a disciplined, documented response that begins the moment a breach is discovered. Organizations that have a plan execute it. Organizations that don’t improvise, and improvisation under a 30-day deadline, are where compliance failures happen.

Step 1, Contain and Assess the Breach
Before any notification can be drafted, the breach must be contained. This means immediately isolating affected systems to prevent further unauthorized access, preserving all logs and forensic evidence, and engaging a qualified incident response team, whether internal or third-party. The goal at this stage is not to fix everything; it is to stop the bleeding and understand the scope.
The assessment must answer four questions: What systems were affected? What data was exposed? How many individuals are potentially impacted? And when did the breach begin? That last question matters more than most organizations realize. Under California law, the 30-day notification clock starts when discovery occurs. Still, if an investigation reveals the breach began weeks or months earlier, the organization must be prepared to explain that timeline to regulators and, potentially, to a court.
Do not delay containment while waiting for certainty. California law does not require confirmed data theft to trigger notification obligations. Reasonable belief that an unauthorized party accessed personal information is sufficient. Acting quickly on an incomplete picture is far safer, legally and operationally, than waiting for perfect information that may never arrive.
Step 2: Determine Notification Obligations
Once the scope of the breach is understood, the next step is a legal assessment of who must be notified and under what framework. Not every security incident triggers California’s data breach notification requirements, but the threshold is low, and erring on the side of notification is almost always the safer posture.
The key questions at this stage are whether the compromised data qualifies as personal information under Civil Code 1798.82, whether the data was unencrypted or whether the encryption key was also exposed, and whether there is any reasonable belief that an unauthorized party acquired it. If the answer to all three is yes, notification obligations are triggered.
For organizations subject to additional regulatory frameworks, HIPAA-covered entities, financial institutions under GLBA, or companies subject to the CCPA, this step must evaluate all applicable obligations simultaneously. California’s 30-day deadline will typically govern, but the content and distribution requirements of federal frameworks must be layered in. Legal counsel should be involved at this stage, not at the stage of drafting the notification.
If the breach involves more than 500 California residents, the obligation to notify the California Attorney General is also triggered. Flag this early, it affects the documentation and review process that follows.
Step 3, Draft Your Notification Letter
A breach notification letter is a legal document, not a public relations exercise. The instinct to minimize, soften, or delay the disclosure of what happened is understandable, and almost always counterproductive. California law specifies exactly what the letter must contain, and regulators reviewing notification letters look first for what is missing.
The letter must use plain language. It must be titled “Notice of Data Breach.” It must identify the specific categories of personal information involved, describe what happened and when, explain what the organization is doing in response, and provide contact information for affected individuals to ask questions. If Social Security numbers or financial account information were involved, credit reporting agency contact details must be included.
Before the letter is finalized, it must be reviewed by legal counsel for statutory compliance. This is not optional. The California AG’s office has previously taken enforcement action against organizations for misleading or incomplete breach notifications, in one case securing a $6.75 million penalty against a software company for downplaying the full scope of a breach in its public notification. The notification letter is not just communication; it is the primary record of the organization’s compliance.
Once approved, the letter must be delivered to affected individuals within 30 days of discovery. If the breach affects more than 500 California residents, a sample copy must be submitted to the California Attorney General at the same time.
Step 4, Notify the California DOJ
Submitting a breach notification to the California Department of Justice is a statutory obligation, not a courtesy. Any breach affecting more than 500 California residents requires a sample copy of the notification to be submitted to the AG’s office at the same time it is sent to affected individuals.
The submission is made through the AG’s online breach notification portal. The notice is reviewed for content compliance, added to the publicly accessible California DOJ breach database, and used by the AG’s office to monitor patterns of non-compliance across industries. There is no grace period beyond the 30-day deadline, and there is no informal process for submitting late. Late notifications are logged as such.
Organizations should treat the DOJ submission with the same rigor as the individual notification. The AG’s office has used information from submitted notices to initiate enforcement investigations, particularly when the described incident is inconsistent with the organization’s security disclosures, the notification omits required elements, or the timing of the submission suggests the 30-day deadline was missed.
Step 5, Post-Breach Security Measures
Notification closes the immediate legal obligation. It does not close the incident. Once affected individuals and the AG’s office have been notified, the work of preventing recurrence begins, and regulators, courts, and insurers will all want to see evidence of it.
The priority is a root cause analysis: a documented investigation into exactly how the breach occurred, what controls failed, and what changes are required to prevent a similar incident. This analysis forms the foundation for every remediation decision that follows, whether that means patching a vulnerability, rearchitecting access controls, replacing a vendor, or overhauling credential management practices.
Specific post-breach measures that California regulators and courts look favorably upon include implementing or expanding multi-factor authentication across all systems that handle personal information, conducting a full audit of third-party vendor access and contractual security obligations, deploying real-time monitoring capable of detecting unauthorized access before it becomes a multi-month exposure, and providing mandatory security training to all personnel who handle personal data.
Organizations should also review and update their incident response plan in light of what the breach revealed. The most common finding in post-breach reviews is not that the plan was absent; it is that the plan hadn’t been tested, or that it assumed a faster detection timeline than reality delivered. A breach that takes 60 days to detect cannot be remediated and notified within 30 days of discovery. Closing that gap is the most important post-breach investment an organization can make.
Is Your Organization’s Data Already Exposed on the Dark Web?
Most organizations discover a data breach one of two ways: an attacker tells them, or a regulator does. Neither is a position you want to be in, especially under California law, where the clock starts the moment you discover the breach, regardless of how long the data has already been circulating elsewhere.

The uncomfortable reality is that compromised data rarely stays private. Credentials harvested in a breach appear on dark web forums within hours. Databases get packaged and sold. Sensitive records end up in credential marketplaces, ransomware leak sites, and threat actor communities long before any internal alarm is triggered. By the time most organizations realize they have a problem, they are already behind, legally, operationally, and reputationally.
Why Dark Web Monitoring Matters After a Breach
California’s 30-day notification deadline assumes an organization knows when a breach occurred. But detection gaps, the time between when a breach happens and when an organization discovers it, routinely stretch into weeks or months. During that window, the organization has no legal obligation to notify because it does not know the matter. The affected individuals, however, have no protection.
Dark web monitoring closes that gap. By continuously scanning dark web forums, credential marketplaces, ransomware leak sites, and threat actor channels for an organization’s data, monitoring tools surface evidence of exposure before it becomes a discovered breach under the law. That warning changes everything: it gives organizations time to contain the incident, assess the scope, and prepare a compliant notification response, rather than scrambling to meet a deadline they just learned about.
It also changes the nature of the breach itself. An organization that detects compromised credentials on the dark web before an attacker uses them can invalidate those credentials, close the access vector, and potentially prevent the deeper intrusion that would have triggered far larger notification obligations. In this context, dark web monitoring is not just a compliance tool; it is a breach prevention mechanism.
How DeXpose Detects Breach Data Before You’re Legally Liable
DeXpose monitors the dark web continuously, scanning across hidden forums, encrypted messaging channels, ransomware group leak pages, and breach databases for your organization’s exposed data, before you receive a regulatory inquiry or a threat actor’s ransom demand.
The platform tracks compromised credentials, leaked employee and customer records, exposed intellectual property, and mentions of your organization across threat actor communities. When your data surfaces, DeXpose identifies it, contextualizes it within the broader threat landscape, and alerts your team in time to act, not in time to react.
For organizations operating under California’s data breach notification law, this capability has direct legal value. Early detection means the organization controls the timeline. It can investigate the exposure, determine whether Civil Code 1798.82 notification obligations are triggered, engage legal counsel, and prepare a compliant notification, all within the 30-day window rather than counting down from the moment a breach they never saw coming is finally confirmed.
DeXpose also provides Attack Surface Mapping and Brand Protection monitoring, giving organizations visibility into the full surface area of their exposure, not just the data that has already leaked, but the vulnerabilities and impersonation risks that could lead to the next breach.
Free Dark Web Report, Check Your Organization Now
Before a regulator contacts you. Before an attacker escalates. Before affected customers receive a notification letter explaining that their data was compromised, and that you’re only now finding out.
DeXpose offers a free dark web report that scans for your organization’s exposed data across dark web sources and delivers a clear picture of what’s already out there. No commitment required. No sales process before you see the results.
If your organization holds personal information on California residents, and the odds are high that it does, you have legal obligations the moment a breach is discovered. The question is whether you discover it on your terms or someone else’s.
Check your exposure now:
🔍 Get Your Free Dark Web Report →
For continuous monitoring, real-time breach alerts, and full dark web surveillance tailored to your organization’s risk profile:
🛡️ Explore Dark Web Monitoring by DeXpose →
What California’s Breach Law Is Really Telling You
California didn’t build one of the strictest data breach notification frameworks in the world to create paperwork. It built it because delayed disclosure causes real harm, and the organizations holding personal data are responsible for preventing that harm, not just reporting it after the fact.
Civil Code 1798.82 has a clear message: know your exposure, move fast, and be transparent. The 30-day deadline under SB 446 simply made that message impossible to ignore.
The organizations that handle this well aren’t the ones with the best lawyers on speed dial. They’re the ones that know about a breach before the attacker announces it, because they were watching.
That’s the posture California law rewards. And it’s the posture DeXpose is built to support.
Frequently Asked Questions (FAQ’s)
What is California’s data breach notification law?
California’s data breach notification law requires any business or government agency that owns or maintains personal information about California residents to notify those individuals when their unencrypted data is acquired, or reasonably believed to have been acquired, by an unauthorized party. It is codified primarily under Civil Code 1798.82.
How long does a company have to notify customers of a data breach in California?
As of January 1, 2026, companies have 30 calendar days from the date of discovery to notify affected California residents. This deadline was established by SB 446, signed into law in October 2025, replacing the previous “most expedient time possible” standard.
What is California Civil Code 1798.82?
Civil Code 1798.82 is the primary statute governing data breach notification obligations for businesses in California. It defines what constitutes a breach, specifies what personal information is protected, sets notification requirements, and establishes the penalties for non-compliance.
What are the penalties for violating California’s data breach notification law?
Violations of Civil Code 1798.82 can result in civil penalties of up to $2,500 per unintentional violation and $7,500 per intentional violation, with each affected individual potentially counting as a separate violation. Affected individuals also have a private right of action to sue for damages.
Does California’s breach notification law apply to small businesses?
Yes. California’s data breach notification law applies to any business, regardless of size or industry, that owns, licenses, or maintains personal information about California residents. There is no small-business exemption, and the law applies even to companies headquartered outside California.
What personal information is covered under California’s breach notification requirements?
California law protects an individual’s name combined with sensitive data elements, including Social Security numbers, driver’s license numbers, financial account information, medical or health insurance information, login credentials, and biometric data. Standalone login credentials for online accounts are also covered, even without a name attached.
What changed with California’s 30-day notification rule in 2025?
California’s SB 446, signed in October 2025 and effective January 1, 2026, replaced the vague “without unreasonable delay” standard with a hard 30-calendar-day deadline from the date of breach discovery. The only recognized exception is a formal law enforcement request to delay notification during an active criminal investigation.
How do I report a data breach to the California DOJ?
Any breach affecting more than 500 California residents must be reported to the California Attorney General by submitting a sample copy of the breach notification through the AG’s online portal at the same time it is sent to affected individuals. The submission is added to the publicly accessible California DOJ breach database.
What should a California data breach notification letter include?
A compliant notification must be titled “Notice of Data Breach” and include the types of personal information involved, a description of what happened and when, the organization’s contact information, steps the organization is taking in response, guidance for affected individuals, and, where financial or Social Security data was exposed, contact information for the major credit reporting agencies.
Is California’s breach law stricter than HIPAA?
Yes, in key respects. HIPAA requires covered entities to notify affected individuals within 60 days of a breach of protected health information. California’s updated law requires notification within 30 days, meaning healthcare organizations subject to both frameworks must comply with California’s shorter deadline for California residents, as the stricter standard always governs.