Facebook has more than three billion active users. That scale makes it one of the most valuable data repositories on the planet, and one of the most targeted.
Over the past decade, the platform has been at the center of some of the most significant data breaches in internet history. Hundreds of millions of phone numbers, email addresses, passwords, and personal records have been exposed, leaked, and traded across dark web forums, often without users ever being notified.
Some breaches were the result of external attacks. Others came from decisions made within the company. The Cambridge Analytica scandal didn’t involve a hacker breaking through a firewall; it involved Facebook’s own data-sharing policies being exploited at scale. The 2021 breach that exposed 533 million records wasn’t a fresh attack at all; it was scraped data sitting on a public hacker forum, free for anyone to download.
That pattern, repeated exposure, delayed disclosure, and minimal accountability, is what makes the Facebook data breach story worth understanding in full.
This guide covers every major breach in Facebook’s history, what data was exposed and when, how to check if your information was part of any leak, and what your legal options are if it was. Whether you’re here after seeing a news headline or checking whether your account was affected, you’ll find everything you need to know in one place.
What Is the Facebook Data Breach?
The term “Facebook data breach” doesn’t refer to a single event. It’s a recurring pattern, a series of separate incidents spanning more than a decade in which user data was exposed, stolen, or misused without the knowledge or consent of the people it belonged to.
Some incidents involved external attackers exploiting security vulnerabilities. Others involved third-party apps harvesting data through Facebook’s own developer platform. A few were the direct result of internal negligence, insecure data storage, overly loose access controls, or policies that prioritized growth over privacy.
What connects all of them is the same outcome: real people’s personal information ended up somewhere it was never supposed to be.
How Facebook Collects and Stores User Data
Every interaction on Facebook generates data. When you create a profile, you hand over your name, email address, phone number, date of birth, and location. But that’s just the starting point.
Facebook tracks what you like, what you share, how long you pause on a post, which ads you click, which apps you connect to, and who you communicate with. It stores device information, IP addresses, browsing behavior across third-party websites, and in some cases, data from offline sources tied back to your identity through its advertising infrastructure.
This data is stored across Facebook’s server infrastructure and, until significant regulatory pressure forced changes, was routinely shared with third-party developers and advertising partners with very limited oversight. The breadth of what Facebook holds on any individual user is what makes each breach consequential. It’s rarely just a username and password. It’s a detailed profile.
Why Facebook Has Been a Repeated Target
The answer is straightforward: the data is worth too much.
A single Facebook profile can contain enough information to impersonate someone, reset account passwords across other platforms, run targeted phishing campaigns, or build synthetic identities for financial fraud. At the scale of hundreds of millions of users, that data becomes extraordinarily valuable to cybercriminals, data brokers, and state-level threat actors alike.
But volume alone doesn’t explain the repetition. Facebook has also been a repeated target because its platform was built for openness. The same APIs that allowed developers to build apps on top of Facebook’s ecosystem also created exposure points that bad actors could, and did, exploit. For years, the company prioritized platform growth over access controls, and the data breaches that followed are a direct consequence of those priorities.
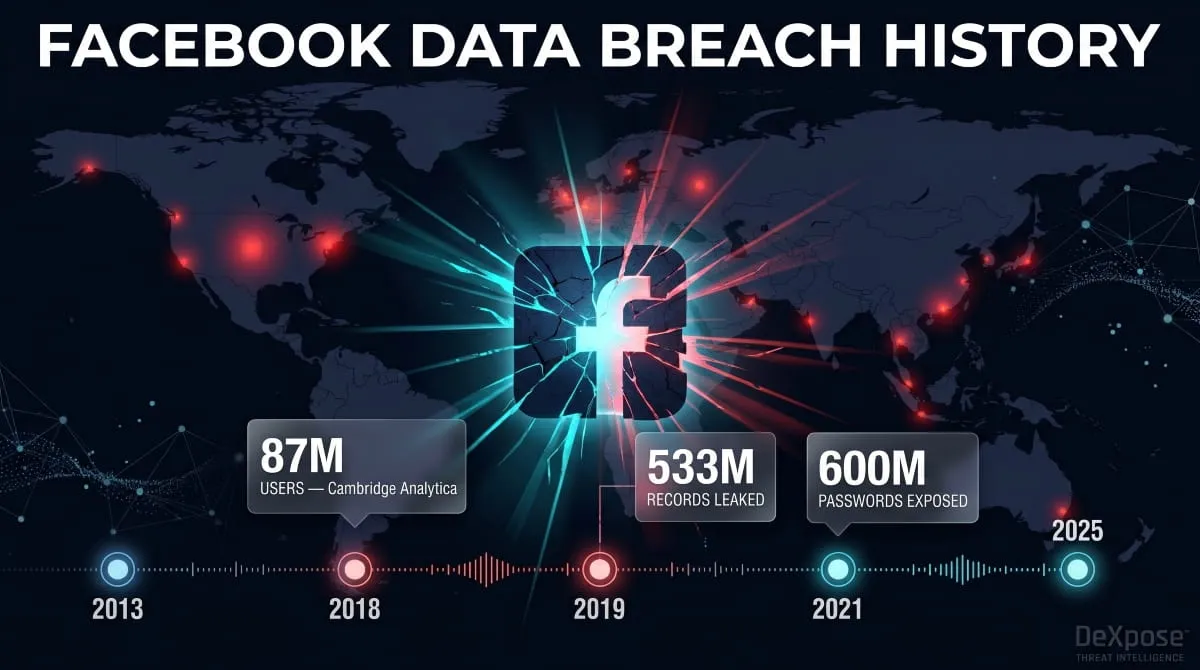
Full Timeline of Facebook Data Breaches (2013–2025)
Facebook’s data breach history isn’t a single chapter; it’s a long record of compounding failures, each one revealing a new dimension of how poorly user data was being protected. Here are all the major incidents, in order.

2013–2015, Early Exposure Events
The problems started earlier than most people realize. Between 2013 and 2015, a vulnerability in Facebook’s search and contact import features allowed malicious actors to systematically scrape user data, phone numbers, email addresses, and profile information by querying the platform with known contact details and harvesting the results.
Facebook was aware of the issue. Rather than disclosing it publicly, the company quietly patched the vulnerability and said nothing about it. This decision would ultimately define the 2021 breach because the data collected during this window was the same dataset that surfaced years later on hacker forums.
2018, Cambridge Analytica Scandal (87 Million Users)
This is the breach that changed everything, not just for Facebook, but for the public conversation around data privacy.
Cambridge Analytica, a British political consulting firm, gained access to the personal data of up to 87 million Facebook users without their explicit consent. The mechanism was a third-party personality quiz app called “thisisyourdigitallife,” built by researcher Aleksandr Kogan. The app collected data not only from users who installed it, but also from all their Facebook friends, exploiting a loophole in Facebook’s developer API that enabled this kind of cascading data harvesting.
That data was then passed to Cambridge Analytica and allegedly used to build psychographic voter profiles for political campaigns, including the 2016 U.S. presidential election and the Brexit referendum.
Facebook knew about the data transfer as early as 2015 and asked for the data to be deleted. It was not. The company chose not to inform affected users or regulators. When the story broke publicly in March 2018 through investigative reporting by The Guardian and The New York Times, the fallout was immediate: congressional hearings, a $5 billion FTC fine, and a fundamental shift in how the world viewed Facebook’s relationship with user data.
2018, Security Breach: 50 Million Accounts Exposed
Just months after Cambridge Analytica dominated headlines, Facebook disclosed a separate and technically distinct security breach. In September 2018, attackers exploited a vulnerability in the platform’s “View As” feature, a tool that allowed users to see how their profile appeared to others.
The flaw allowed attackers to steal access tokens, the digital keys that keep users logged into Facebook without requiring repeated password entry. With those tokens, an attacker could take full control of an account. Facebook confirmed that approximately 50 million accounts were directly affected, with another 40 million potentially at risk.
It was the largest security breach in the company’s history at that point, and it forced Facebook to reset access tokens for nearly 90 million accounts. The Irish Data Protection Commission, Facebook’s lead GDPR regulator, opened an investigation that would drag on for years.
In 2019, Millions of passwords were stored in Plaintext.
In March 2019, Facebook acknowledged that it had been storing hundreds of millions of user passwords in Plaintext, meaning they were readable by Facebook employees without any encryption. The issue affected between 200 million and 600 million users across Facebook and Instagram, with some records dating back to 2012.
Passwords should never be stored in a readable format. It is one of the most fundamental rules of data security. Facebook’s admission that this had been happening for years and that thousands of employees could search those records was damaging not because of external exploitation, but because of what it revealed about internal data-handling practices.
In 2021, 533 million records were leaked on Hacker Forums.
In April 2021, a dataset containing the personal information of 533 million Facebook users was posted freely on a hacker forum. The data included phone numbers, full names, email addresses, dates of birth, locations, and biographical information across users from 106 countries.
Facebook’s response was notable for what it lacked. The company confirmed the data was real but stated it was “old”, collected through the scraping vulnerability that had been patched back in 2019. It declined to notify affected users directly and announced it had no plans to do so.
Security researchers pushed back hard. The data may have been old, but it was new to the forum. For the hundreds of millions of people whose phone numbers and personal details were now publicly searchable, the age of the breach was irrelevant; the exposure was happening in real time.
2021, The 858 Million Data Broker Breach
Later in 2021, reports emerged of a separate dataset compiled by a data broker containing records on approximately 858 million Facebook users. Unlike the April leak, this dataset was not the result of a single scraping event. It appeared to be an aggregated collection built over time from multiple sources, combining scraped Facebook data with information from other platforms and public records.
The 858 million figure made it one of the largest Facebook-related data exposures ever recorded. It illustrated a broader problem: even when Facebook patches a vulnerability, the data already collected doesn’t disappear. It circulates, gets combined with other datasets, and resurfaces in new forms across dark web marketplaces and data broker networks.
2022–2024, What’s Happened Since
The years following 2021 brought a shift from large singular breaches to a more distributed pattern of exposure. Smaller leaks, scraped datasets, and credential dumps referencing Facebook accounts continued to appear on dark web forums throughout 2022, 2023, and into 2024.
Regulatory consequences also continued to accumulate. In November 2022, Ireland’s Data Protection Commission issued a €265 million fine against Meta, Facebook’s parent company, specifically for the 2021 scraping breach. Meta also faced ongoing litigation across multiple jurisdictions related to Cambridge Analytica, the 2018 security breach, and broader data privacy violations under GDPR and U.S. state laws.
2025, Latest Facebook Security Breach Reports
As of 2025, Facebook and its parent company, Meta, remain under active regulatory scrutiny in both Europe and the United States. Fresh reports of scraped datasets and credential exposure tied to Facebook accounts continue to surface, reflecting the long tail of earlier breaches still cycling through dark web ecosystems.
No single catastrophic new breach on the scale of 2021 has been publicly confirmed at the time of writing, but the threat landscape has not improved. The data from prior breaches remains in circulation, and users who have never checked their exposure status remain at risk from credential stuffing, phishing, and identity fraud driven by information that has been publicly available for years.
The Cambridge Analytica Facebook Data Breach, Case Study
Of every incident in Facebook’s data breach history, Cambridge Analytica remains the most consequential. It wasn’t the largest by record count, and it didn’t involve a technical exploit in the conventional sense. What made it defining was the nature of the misuse, personal data harvested at scale and allegedly deployed to influence democratic elections.

What Data Was Taken and How
The mechanism was deceptively simple. A Cambridge University researcher named Aleksandr Kogan built a Facebook app, a personality quiz called “thisisyourdigitallife”, and made it available on the platform in 2013. Around 270,000 users installed the app and consented to sharing their own profile data as part of the experience.
What those users didn’t know was that Facebook’s developer API at the time permitted something far broader. When someone installed the app, it didn’t just collect their data; it harvested the data of every person in their friends list, without those friends ever installing anything or agreeing to anything. Through this single loophole, Kogan was able to collect detailed profile information on approximately 87 million Facebook users from a base of only 270,000 direct participants.
The data collected included names, locations, birthdays, likes, relationship statuses, and, in many cases, private messages. It was rich, behavioral, and deeply personal, exactly the kind of dataset needed to build psychological profiles at a population scale.
How It Was Used and Who Was Affected
Kogan passed the dataset to Cambridge Analytica, a political data firm with ties to Steve Bannon and Robert Mercer. This transfer violated Facebook’s developer policies, which prohibited the sale or transfer of data collected through its platform to third parties.
Cambridge Analytica used the data to build psychographic models, essentially, a system for categorizing people by personality type based on their Facebook behavior, then targeting them with tailored political messaging. The firm claimed its models could identify psychological vulnerabilities and exploit them through precision-targeted advertising.
The firm’s work touched some of the most consequential political campaigns of the decade. Ted Cruz’s 2016 presidential campaign contracted it, and later Donald Trump’s did. There are also documented links to the Brexit Leave campaign, though the precise extent of Cambridge Analytica’s role there remains disputed.
The 87 million affected users were spread across multiple countries, with the United States accounting for the largest share. Most of them had no idea their data had ever left Facebook’s ecosystem.
Ethical Issues and Public Fallout
The ethical dimensions of this breach go beyond the data theft itself. Facebook had known about the unauthorized transfer since 2015, when a journalist first flagged it. The company asked Cambridge Analytica and Kogan to delete the data and certify that they had done so. Both said they complied. Neither fully did.
Facebook chose not to inform regulators, not to inform users, and not to conduct any meaningful audit to verify the deletion. For three years, the company sat on that knowledge while the data remained in use.
When the story broke publicly in March 2018, through parallel investigations by The Guardian, The New York Times, and Channel 4 News, the response was immediate and global. Mark Zuckerberg testified before the U.S. Senate and the House of Representatives. Regulators in Europe, the United States, Canada, and the United Kingdom launched investigations. The hashtag #DeleteFacebook trended worldwide.
The financial and legal consequences were severe. The FTC fined Facebook $5 billion in 2019, the largest fine ever imposed on a technology company at the time, specifically for privacy violations related to Cambridge Analytica. The UK’s Information Commissioner’s Office fined Facebook £500,000, the maximum possible under laws that predated GDPR.
Cambridge Analytica itself filed for bankruptcy in May 2018, just weeks after the story broke. But the data it collected didn’t disappear when the company did. And the question it forced into public consciousness, about who owns the data you generate on social platforms, and what can be done with it, has never fully been resolved.
The April 2021 Facebook Breach, 533 Million Records
In early April 2021, a dataset containing personal information on 533 million Facebook users was posted freely on a low-level hacker forum. No paywall. No negotiation. Just a publicly accessible file that anyone with a forum account could download.

The scale was staggering, with users from 106 countries, with the United States, Egypt, and the Philippines among the most heavily affected. But what made this breach particularly damaging wasn’t just the size. It was Facebook’s response.
What Information Was Exposed (Phone Numbers, Emails, IDs)
The dataset was not a collection of passwords or financial credentials. What it contained was in many ways more permanently damaging, the kind of personal information that cannot be changed after the fact.
For the majority of affected users, the exposed data included full name, phone number, Facebook ID, date of birth, location, and biographical information. A subset of records also contained email addresses, relationship status, employer information, and account creation date. In some cases, enough overlapping data points existed within a single record to build a near-complete personal profile from a single entry.
Phone numbers were the most significant element. Unlike passwords, you cannot reset a phone number with a few clicks. For millions of users, that number is tied to two-factor authentication across banking apps, email accounts, and other social platforms, meaning the exposure created a vector for account takeover well beyond Facebook itself.
How to Check if Your Number Was in the Leak
Because phone numbers, not email addresses, were the primary identifier in this dataset, the usual breach-checking tools initially fell short. Services like Have I Been Pwned eventually added support for phone number lookups, but the process is less straightforward than a standard email search.
The most reliable way to check your exposure is to use a dedicated dark web monitoring tool that scans across breach databases, leaked credential dumps, and dark web sources simultaneously. DeXpose’s Email Data Breach Scan can determine whether your email address appears in known breach records associated with this and other major leaks. For a broader picture of your organization’s exposure, including phone numbers and account credentials surfacing on dark web markets, the Free Dark Web Report provides an instant snapshot across multiple data sources.
If you were active on Facebook before 2020 and have never checked your exposure status, the probability that your data appears somewhere in this dataset is significant. Over 533 million records from a platform with roughly 2.8 billion users at the time represent roughly one in five active accounts.
How the Data Ended Up on Dark Web Forums
This is where Facebook’s handling of the situation became most controversial.
The data was not collected in 2021. It was scraped between 2018 and 2019 using a vulnerability in Facebook’s contact import feature, the same flaw referenced in the 2013–2015 timeline. The feature was designed to help users find people they knew by uploading phone contacts. Attackers reverse-engineered it to do the opposite: submit phone numbers at scale and harvest the Facebook profiles associated with them.
Facebook patched the vulnerability in 2019. But by then, the data had already been collected. It passed through private channels for roughly two years before being posted publicly in April 2021, first offered for sale, then eventually released for free once its market value had been exhausted.
When Facebook responded, it confirmed the data was legitimate but emphasized that it was “old” and that the underlying vulnerability had already been fixed. The company stated it had no plans to notify the 533 million affected users. That decision drew sharp criticism from data protection regulators across Europe, with Ireland’s DPC and other authorities questioning whether Meta had met its GDPR obligation to assess and communicate the breach’s ongoing impact.
The data being “old” did not make it inert. Scraped datasets don’t expire. They get indexed, combined with other leaked records, and used in phishing campaigns, SIM-swapping attacks, and identity fraud, sometimes years after the original collection. For the people whose information was in that file, the breach became active the moment it was posted publicly, regardless of when the scraping occurred.
Was I Affected? How to Check If Your Facebook Data Was Breached
Given the scale of Facebook’s breach history, the more practical question isn’t whether a breach happened; it’s whether your personal data was part of one. With hundreds of millions of records exposed across multiple incidents, a significant portion of Facebook’s user base has had some form of personal information compromised without ever receiving direct notification.

Checking your exposure status is not complicated, but it does require using the right tools.
Free Tools to Search Your Email and Phone Number
The 2021 breach made phone number lookups essential, since most records in that dataset were indexed by phone rather than email. Standard breach checkers that only scan email addresses will miss it entirely.
For email-based exposure, DeXpose’s Email Data Breach Scan at dexpose.io/email-data-breach-scan checks whether your email address appears across known data breaches, dark web sources, and leaked credential databases, including records tied to major Facebook incidents. It takes seconds and requires no account to run.
For a broader snapshot that goes beyond a single identifier, the Free Dark Web Report at dexpose.io/free-darkweb-report scans across dark web markets, malware logs, and public breach repositories to show what information connected to you is currently circulating. If your phone number, email, or account credentials from a Facebook breach have made their way into active dark web ecosystems, that exposure becomes visible there.
What to Do If You’re in the Database
Finding your data in a breach record is alarming, but it’s also actionable. The steps depend on what was exposed.
If your email address or password appeared in a breach, change your Facebook password immediately and any other accounts where you reused the same credentials. Enable two-factor authentication if you haven’t already, and use an authenticator app rather than SMS where possible, since phone numbers exposed in the 2021 breach can be used in SIM-swapping attacks to intercept SMS codes.
If your phone number was in the dataset, be alert to unsolicited calls, texts, and phishing attempts that reference your name or personal details. Attackers use scraped data to make social engineering attempts feel credible. Knowing your number is out there means applying additional scrutiny to anything unexpected that lands on it.
If biographical data, date of birth, location, and employer were exposed alongside your name, monitor for signs of identity misuse. That combination of data points is enough to pass security questions on financial accounts and initiate fraudulent applications in your name.
Protect What’s Still at Risk, DeXpose Can Help
Checking whether you were affected is the first step. Staying protected after that requires ongoing visibility, because breached data doesn’t disappear after you find it. It circulates, combines with newer leaks, and continues to pose risk months or years after the original exposure.
DeXpose Email Data Breach Scan, Find out immediately whether your email appears in known breach records, including those tied to Facebook’s major incidents.
Free Dark Web Report: Get an instant exposure report covering dark web markets, malware logs, and public breach databases. No account required.
Brand Protection: If you’re a business owner or security professional, Facebook data breaches don’t just affect individuals. Exposed employee credentials, leaked customer data, and compromised brand assets create serious downstream risk. DeXpose’s Brand Protection service monitors for your organization’s exposure across dark web sources, impersonation attempts, and credential leaks, so threats are identified before they become incidents.
What Data Has Been Exposed in Facebook Breaches?
Over the past decade, Facebook breaches have exposed a remarkably wide range of personal data. Understanding exactly what has been compromised, and why each category matters, is what separates a vague awareness of risk from a clear picture of actual exposure.

Phone Numbers and Email Addresses
These two identifiers sit at the center of Facebook’s breach history, and the 2021 leak made phone numbers the most widely exposed data type. For 533 million users, their phone number, often the same one linked to banking apps, email recovery, and two-factor authentication on other platforms, was made publicly available on a hacker forum at no cost.
Email addresses appeared across multiple breach events, including Cambridge Analytica and various scraping incidents. On their own, an email address feels low-stakes. In combination with a name, date of birth, and phone number, all of which appeared together in the 2021 dataset, it becomes the foundation of a highly credible phishing attempt or account takeover operation.
The reason these two data types cause disproportionate downstream damage is that they don’t just expose Facebook; they also expose the broader ecosystem. They expose every other account, service, and platform where the same contact details were used to register.
Passwords and Login Credentials
Facebook’s 2019 plaintext password incident was a failure of a different kind entirely. This wasn’t data stolen by an outside attacker; it was data that Facebook itself had stored incorrectly, in readable format, accessible to thousands of employees for years.
Between 200 million and 600 million passwords were affected, spanning Facebook and Instagram accounts, with some records dating back to 2012. Properly handled passwords are stored as encrypted hashes, a format that makes them useless even if someone gains access to the storage system. Storing them in Plaintext removed that protection entirely.
For users who reused those passwords across other platforms, as research consistently shows is the case for the majority of people, the exposure extended far beyond Facebook. A leaked Facebook password can become a key to email inboxes, financial accounts, and any other services that use the same credentials.
Messenger and Private Communications
The Cambridge Analytica breach included private messages for a subset of affected users, a detail that received less attention than the headline figures but carries significant weight. Private messages carry an entirely different expectation of confidentiality than public profile data. Their exposure isn’t just a privacy violation in the abstract; it’s the kind of exposure that can have real consequences for relationships, employment, and personal safety.
Beyond Cambridge Analytica, Facebook Messenger has faced separate scrutiny over the years, from allegations of content scanning within the platform to questions about how message metadata is stored and who has access to it. While no single breach has exposed Messenger data at the scale of the 2021 phone number leak, the combination of message content and metadata that Facebook holds represents one of the most sensitive data categories on the platform.
Facebook Marketplace and Financial Data
Facebook Marketplace introduced a new exposure surface that earlier breaches didn’t involve. As the platform grew into a significant peer-to-peer commerce tool, it brought with it transaction records, shipping addresses, payment-related conversations, and in some cases, partial financial details shared directly between buyers and sellers through Messenger.
Scraped and leaked Marketplace data has appeared in breach datasets, giving attackers not just static profile information but transactional context, who bought what, from whom, and where it was shipped. That level of detail enables highly targeted fraud, including purchase scams, address harvesting for physical mail fraud, and social engineering attacks built around real transaction histories that feel legitimate.
Facebook Data Breaches and the Law, Fines, Lawsuits & GDPR
Facebook’s data breach history didn’t just produce headlines; it also led to some of the most significant regulatory and legal consequences in the history of the technology industry. Across multiple jurisdictions, regulators and courts have found that Facebook failed in its obligations to protect user data, and the financial penalties that followed reflect the scale of those failures.

Facebook GDPR Breach, The Irish DPC Investigation
Because Meta’s European headquarters are in Dublin, Ireland, the Data Protection Commission serves as the lead GDPR supervisory authority for Facebook across the European Union. That position has placed the Irish DPC at the center of nearly every major post-2018 investigation into Facebook’s data handling practices.
The 2021 scraping breach triggered one of the most closely watched investigations. After extended scrutiny of how the data was collected, how long Facebook had known about the vulnerability, and whether the company had met its GDPR obligation to assess and communicate the breach, the Irish DPC issued a €265 million fine against Meta in November 2022. The ruling found that Facebook had failed to implement adequate technical and organizational measures to prevent the systematic scraping of user data.
This was not an isolated ruling. The Irish DPC has issued a series of findings against Meta in recent years, covering everything from data transfer practices to children’s privacy violations, with cumulative fines running into the billions of euros. For European users in particular, GDPR created enforceable rights around data protection, and Facebook’s breach history has become one of the most prominent test cases for how seriously those rights are enforced.
How Much Was Facebook Fined for Data Breaches?
The total financial penalties imposed on Facebook and its parent company, Meta, across all jurisdictions run to several billion dollars. The single largest came from the U.S. Federal Trade Commission, a $5 billion fine issued in 2019, directly tied to the Cambridge Analytica scandal and Facebook’s broader violations of a 2012 consent decree that had required the company to protect user privacy.
The €265 million Irish DPC fine followed in 2022 for the scraping breach. The UK’s Information Commissioner’s Office issued a £500,000 penalty, the maximum available under pre-GDPR law, for the Cambridge Analytica incident. Additional fines and regulatory actions have been issued across Italy, South Korea, and several other jurisdictions.
Despite the scale of these figures, critics have consistently argued that the penalties fall short of genuine deterrence for a company generating annual revenues in excess of $100 billion. The $5 billion FTC fine, while record-breaking at the time, accounted for less than one month of Facebook’s revenue that year.
Facebook Class Action Lawsuits and Settlements
Parallel to regulatory action, Facebook has faced a sustained wave of civil litigation from affected users. Class action lawsuits related to Cambridge Analytica alone resulted in a $725 million settlement reached in late 2022, the largest privacy settlement in U.S. history at the time. Eligible claimants were U.S. Facebook users active between 2007 and 2022.
Separate class actions tied to the 2021 data breach, the plaintext password storage incident, and various other privacy violations have proceeded through courts in the United States and Europe. Not all have resulted in settlements of comparable scale, but the cumulative litigation landscape has imposed both financial costs and reputational consequences that regulatory fines alone did not.
Can You Sue Facebook for a Data Breach?
In most jurisdictions, yes, though the practical path depends on where you are located and what the breach exposed.
In the United States, individuals can file lawsuits against Facebook for damages arising from data breaches. Still, they are rarely pursued independently, given the cost and complexity of litigation against a well-resourced defendant. The more common route is participation in class action lawsuits, where affected users are grouped and represented collectively. If a settlement is reached, eligible class members typically receive notice and an opportunity to file a claim.
In the European Union and the United Kingdom, GDPR provides a more direct mechanism. Individuals have the right to seek compensation from a data controller, including Meta, for material or non-material damage resulting from a breach of the regulation. This includes financial losses, distress, and the loss of control over personal data. Several law firms across Europe have actively pursued group litigation on behalf of affected Facebook users under this framework.
How to File a Facebook Data Breach Claim
The process varies by jurisdiction, but the general steps apply broadly.
First, establish that you were affected. Document your Facebook account activity during the relevant breach periods and, where possible, confirm your data appears in known breach records. Tools like DeXpose’s Email Data Breach Scan can help verify whether your information surfaces in breach databases connected to Facebook incidents.
In the United States, monitor for class action notices related to active Facebook litigation. Settlement administrators typically publish claim-filing portals with eligibility criteria and deadlines. Missing a filing window forfeits your right to participate in that settlement.
In the EU and UK, you can file a complaint directly with your national data protection authority, the Irish DPC, the UK ICO, or your local equivalent, which carries no cost and can trigger an investigation on your behalf. Alternatively, several law firms specializing in GDPR litigation offer no-win no-fee arrangements for Facebook data breach compensation claims, particularly in the UK, Ireland, Germany, and the Netherlands.
In all cases, the foundation of any claim is documentation: when you used Facebook, what data you provided, and evidence that it was exposed through a breach the company was responsible for preventing.
How Did Facebook Respond to Its Data Breaches?
When a company the size of Facebook faces a data breach, its response becomes almost as consequential as the breach itself. How quickly it acts, what it discloses, who it notifies, and what it actually changes determines whether the incident becomes a turning point or simply the next entry in a growing list. Across multiple incidents, Facebook’s responses have followed a recognizable pattern, one that regulators, researchers, and affected users have repeatedly found wanting.

Official Statements and Crisis Communications
Facebook’s communications around its major breaches have been consistently characterized by delayed disclosure, carefully managed language, and a tendency to minimize rather than clarify.
When Cambridge Analytica came under public scrutiny in March 2018, Facebook had known about the unauthorized data transfer for three years. Mark Zuckerberg’s initial public response came days after the story broke, acknowledging that “a breach of trust” had occurred while stopping short of accepting full responsibility for the systemic API policies that made the harvest possible in the first place. His subsequent congressional testimony was notable more for what it revealed about senators’ limited understanding of the platform than for any substantive commitments Facebook made in response.
The 2021 breach produced perhaps the most criticized communications of all. Facebook’s official position, that the data was “old,” the vulnerability already patched, and direct user notification unnecessary, was technically accurate in a narrow sense and practically indefensible in a broader one. Telling half a billion people that their permanently exposed phone numbers were not worth a direct notification because the scraping happened two years earlier was a position that satisfied almost no one outside of Facebook’s own communications team.
Across both incidents and others in between, the pattern held: acknowledge minimally, attribute to past events where possible, and avoid creating the expectation that affected users would be proactively informed.
Security Changes Facebook Implemented
To be fair, Facebook did implement meaningful technical changes in the aftermath of its major breaches, though in several cases those changes came years after the vulnerabilities were first identified.
Following the Cambridge Analytica scandal, Facebook significantly overhauled its developer API. The friend data permissions that had allowed Kogan’s app to harvest 87 million records from 270,000 direct participants were removed. Third-party app access to user data was restricted, and Facebook introduced a more rigorous app review process intended to prevent similar harvesting operations in the future.
After the 2018 security breach, the “View As” feature that allowed the access token theft was temporarily taken offline and later substantially redesigned. Facebook also expanded its bug bounty program and increased investment in its internal security infrastructure.
The plaintext password issue prompted a full audit of how credentials were stored across Facebook’s systems, with the company stating that the storage practices had been corrected and no evidence of external access had been found.
Scraping, the mechanism behind the 2021 breach, proved harder to address structurally, given that the contact import features involved served a legitimate user purpose. Facebook implemented rate limiting and detection systems to make bulk scraping more difficult, but the data already collected before those controls existed could not be recalled.
Was Facebook’s Response Enough?
By most independent assessments, regulatory, academic, and journalistic, the answer is no.
The core problem is not that Facebook failed to act after each breach. It’s that the responses were consistently reactive rather than proactive, and consistently calibrated to legal minimums rather than user interests. The company patched vulnerabilities after they were exploited, disclosed breaches after they became public, and notified users only when required by law.
GDPR was designed in part to change that calculus by imposing mandatory breach notification timelines and financial penalties large enough to make inaction costly. The €265 million fine for the 2021 scraping breach was a direct consequence of regulators finding that Facebook had failed to meet those obligations. But even with that regulatory framework in place, the Irish DPC investigation took more than a year to conclude, meaning affected users went without official confirmation of their exposure status for the duration.
The broader question Facebook’s response history raises is structural. A company whose business model depends on collecting and monetizing user data at scale has an inherent tension with the kind of aggressive, user-first breach response that genuine accountability would require. That tension has never been resolved. It has only been managed, and managed repeatedly, in ways that prioritized the platform over the people on it.
What Should You Do After a Facebook Data Breach?
Knowing your data was exposed is only useful if it leads to action. The window between a breach becoming public and attackers actively exploiting the data is often shorter than people expect. In the case of Facebook’s 2021 breach, millions of records had already been circulating privately for two years before most users had any idea they were at risk. The steps below apply whether you’ve just learned about a breach or you’re acting on exposure that happened years ago.

Immediate Steps to Secure Your Account
Start with your Facebook account itself. Change your password immediately, and make it unique, not a variation of something you use elsewhere. If your previous password was reused across other platforms, change it on those accounts too. Credential stuffing attacks work precisely because people reuse passwords, and a leaked Facebook password becomes a skeleton key for every other account that uses the same combination.
Enable two-factor authentication if it isn’t already active. Use an authenticator app rather than SMS verification where possible; phone numbers exposed in the 2021 breach can be targeted in SIM-swapping attacks, which redirect your SMS codes to an attacker’s device before they reach you. An authenticator app removes that vulnerability entirely.
Review the apps and third-party services connected to your Facebook account. Years of casual “Login with Facebook” approvals can leave a long tail of active permissions you’ve forgotten about. Each one represents a potential access point. Revoke anything you don’t actively use.
Finally, check your active sessions. Facebook allows you to see every device and location currently logged into your account. Anything unfamiliar should be terminated immediately.
Monitor for Credential Misuse on the Dark Web
Securing your account addresses the immediate risk. The longer-term problem is that breached data doesn’t disappear; it moves. Phone numbers, email addresses, and biographical details from Facebook breaches get absorbed into dark web marketplaces, combined with data from other leaks, and used in fraud operations that can surface months or years after the original exposure.
Passive monitoring is the only reliable way to stay ahead of this. Rather than checking periodically and hoping nothing new has appeared, continuous dark web monitoring flags your exposed data in real time, enabling you to respond before an attacker has time to act on it.
DeXpose’s Free Dark Web Report gives you an immediate snapshot of what information connected to you is currently circulating across dark web markets, malware logs, and public breach repositories. It takes seconds to run and requires no account. If your data from a Facebook breach has made it into active dark web ecosystems, this is where that becomes visible.
How to Reduce Your Attack Surface Going Forward
Beyond the immediate response, the goal is to make future exposure less damaging, because no platform, including Facebook, can be assumed to be permanently secure.
Treat your phone number as a sensitive credential, not a casual contact detail. Given how central phone numbers were to the 2021 breach and how they serve as recovery and authentication keys across dozens of other platforms, limiting where you share them reduces the damage any single future breach can cause.
Use unique email addresses for different platforms where possible. Some email providers support alias addresses that forward to your main inbox, allowing you to isolate exposure by source. If a specific alias starts receiving phishing attempts, you know exactly where the data came from.
Be deliberate about what biographical information is public on your Facebook profile. Date of birth, hometown, employer, and relationship status are individually innocuous. Combined with a name and phone number in a breach dataset, they become a toolkit for identity fraud. Restricting profile visibility doesn’t eliminate breach risk, but it limits what an attacker can do with the data if a breach occurs.
The underlying principle is straightforward: the less data that is both accurate and publicly associated with your identity, the less useful any single breach becomes. Facebook’s history makes clear that another incident is a question of when, not if. Building habits that prevent damage in advance is the most practical form of protection available.
Facebook vs. Other Major Platform Breaches
Facebook is not the only major platform to have suffered significant data breaches. Google, Apple, and others have all faced incidents involving user data. But when you place them side by side, meaningful differences emerge, in scale, in frequency, like what was exposed, and in how each company chose to respond.

Facebook vs. Google, Breach Comparison
Google’s most significant publicly known breach involved Google+, its now-defunct social network. In 2018, Google disclosed that a software bug had exposed the private profile data of up to 500,000 users, and that the company had known about it for months before disclosing it. A second vulnerability discovered later that year affected 52 million users. Google shut down Google+ in 2019, partly as a consequence of the fallout.
Compared to Facebook’s breach history, Google’s direct platform breaches have been smaller in scale and fewer in number. But the comparison requires an important qualification: Google’s data exposure risk is not primarily through breaches in the conventional sense. It operates through scope. Google holds more comprehensive behavioral data on more people than almost any other entity on the planet: search history, location data, email content, browsing behavior, app usage, and purchase history. The consequences of a large-scale Google breach would likely exceed anything Facebook has experienced, precisely because the data is much more intimate.
Where Facebook’s breaches have predominantly exposed contact information and social graph data, a serious Google breach would implicate the kind of data people rarely think of as stored anywhere at all, the questions they searched at 2 am, the routes they drove, the emails they never expected anyone to read.
Facebook vs. Apple: How Each Handles User Data
Apple occupies a genuinely different position in this comparison, and the difference is architectural rather than just reputational.
Apple’s business model is built on hardware and services, not advertising. That fundamental distinction shapes how the company approaches data collection. Where Facebook’s revenue depends on building detailed profiles of user behavior to sell targeted advertising, Apple has a financial incentive to collect less and to market privacy as a feature. The App Tracking Transparency framework introduced in iOS 14, which requires apps to explicitly request permission before tracking users across platforms, was a direct competitive move against Facebook’s advertising infrastructure, and Facebook publicly said so, estimating it would cost the company billions in annual revenue.
No major breach involving Apple user data at Facebook’s scale has been publicly confirmed. Apple has faced security incidents, including iCloud credential attacks and the 2014 celebrity photo leak, which was the most prominent. Still, these have generally involved targeted account compromises rather than systemic platform-level data exposure.
The honest caveat is that Apple’s cleaner breach record partly reflects what it doesn’t collect rather than superior security alone. A company that holds less sensitive behavioral data has less to expose. That said, Apple’s security architecture, end-to-end encryption defaults on iMessage and FaceTime, and on-device processing for sensitive operations do represent genuine structural privacy advantages over platforms built around centralized data aggregation.
Which Platform Has Had the Most Data Breaches?
By volume and scale of exposed records, Facebook has the most documented breach history among the major consumer platforms. The combination of the Cambridge Analytica incident, the 2018 security breach, the plaintext password exposure, the 2021 scraping leak affecting 533 million users, and the 858 million data broker dataset places Facebook in a category of its own among social platforms in terms of cumulative user data exposure.
That said, the question of which platform has had the “most” breaches depends on how you count. Yahoo, now part of Verizon, holds the record for the single largest breach in internet history, with three billion accounts compromised in a 2013 attack that wasn’t fully disclosed until 2017. LinkedIn has experienced multiple significant breaches. Twitter, Snapchat, and TikTok have all faced data exposure incidents of varying scale.
What distinguishes Facebook is not just the numbers but the pattern. Most platforms have experienced breaches as discrete external incidents. Facebook’s history involves a recurring combination of external attacks, internal negligence, policy failures, and deliberate data-sharing decisions that caused harm. This pattern reflects something more systemic than bad luck. That is ultimately what separates Facebook’s breach record from its peers and why it continues to define the conversation around platform accountability and user data protection.
Conclusion
Facebook’s data breach history is not a story of isolated incidents; it’s a decade-long pattern of systemic failures that has left hundreds of millions of people’s personal information permanently in circulation.
The data exposed across these breaches doesn’t expire. Phone numbers, email addresses, and personal records from incidents dating back to 2013 are still being traded, combined, and exploited today.
Awareness is the starting point, but it isn’t enough. If you haven’t checked your exposure status, now is the time.
Run a free scan with DeXpose’s Email Data Breach Scan to see if your information appears in known breach records, or get a full picture of your dark web exposure with the Free Dark Web Report. Your data is already out there; the question is whether you know about it.
Frequently Asked Questions (FAQ’s)
Has Facebook had a data breach?
Yes, multiple times. Facebook has experienced several major data breaches since 2013, including the Cambridge Analytica scandal affecting 87 million users, a 2018 security breach exposing 50 million accounts, and a 2021 leak that made 533 million users’ personal records publicly available on hacker forums.
When did the Facebook data breach happen?
There is no single date; Facebook has suffered repeated breaches across more than a decade. The most significant incidents occurred in 2018 (Cambridge Analytica and the access token breach), 2019 (plaintext password exposure), and April 2021 (the public release of 533 million records).
How many people were affected by the Facebook data breach?
Across all known incidents combined, well over one billion individual records have been exposed. The 2021 breach alone affected 533 million users across 106 countries, while the Cambridge Analytica scandal compromised data belonging to approximately 87 million people.
What information was stolen in the 2021 Facebook breach?
The 2021 breach exposed full names, phone numbers, Facebook IDs, email addresses, dates of birth, locations, and biographical details. Phone numbers were the most widely affected data type, appearing in the majority of the 533 million records that were posted freely on a hacker forum.
What was Facebook fined for in the data breach?
Yes. Facebook received a $5 billion FTC fine in 2019 for privacy violations tied to Cambridge Analytica, a €265 million fine from Ireland’s Data Protection Commission in 2022 for the 2021 scraping breach, and a £500,000 penalty from the UK’s ICO, among other regulatory actions across multiple jurisdictions.
How do I check if my Facebook data was breached?
Use a dark web monitoring tool that scans breach databases and dark web sources. DeXpose’s Email Data Breach Scan checks whether your email appears in known breach records. At the same time, the Free Dark Web Report provides a broader snapshot of your personal data exposure across dark web markets and leaked databases.
What should I do if my Facebook data was leaked?
Change your Facebook password immediately and update it on any other platforms that use the same credentials. Enable two-factor authentication via an authenticator app, review third-party app permissions on your account, and run a dark web scan to understand the full scope of what was exposed.
Is my Facebook password safe after the 2019 breach?
Not necessarily. Facebook confirmed that between 200 million and 600 million passwords were stored in Plaintext and accessible to thousands of employees for years. If you have not changed your Facebook password since 2019, you should do so immediately and update any other accounts that use that password.
Did Facebook settle the data breach lawsuit?
Yes. The most significant settlement was a $725 million agreement reached in late 2022 to resolve class action litigation related to the Cambridge Analytica data breach, the largest privacy settlement in U.S. history at the time. Eligible claimants were U.S.-based Facebook users active between 2007 and 2022.
What is the Cambridge Analytica Facebook data breach?
Cambridge Analytica was a political consulting firm that obtained personal data from approximately 87 million Facebook users without their consent through a third-party quiz app. The data was allegedly used to build psychographic voter profiles for political campaigns, including the 2016 U.S. presidential election. Facebook had known about the unauthorized data transfer since 2015 but did not disclose it publicly until 2018.