In early 2026, reports began surfacing that Oracle, one of the world’s largest enterprise software and cloud infrastructure companies, had suffered a significant data breach. Oracle’s initial response was a flat denial. Then came the private admissions to customers. Then the federal warnings. Then the lawsuits.
What followed became one of the most closely watched cybersecurity stories of the year: a major cloud vendor caught between public denials and private acknowledgments, while millions of credentials, patient records, and enterprise data remained exposed across multiple compromised systems.
This page covers everything confirmed so far, which Oracle products were breached, which organizations were affected, what data was exposed, and what Oracle has officially said (and deliberately avoided saying). If your company runs Oracle Cloud, Oracle Health, or Oracle E-Business Suite, this is required reading.
Use DeXpose’s free Oracle Breach Check tool to see if your organization appears in the breach data instantly. Check Your Exposure Now →
What Is the Oracle Data Breach?
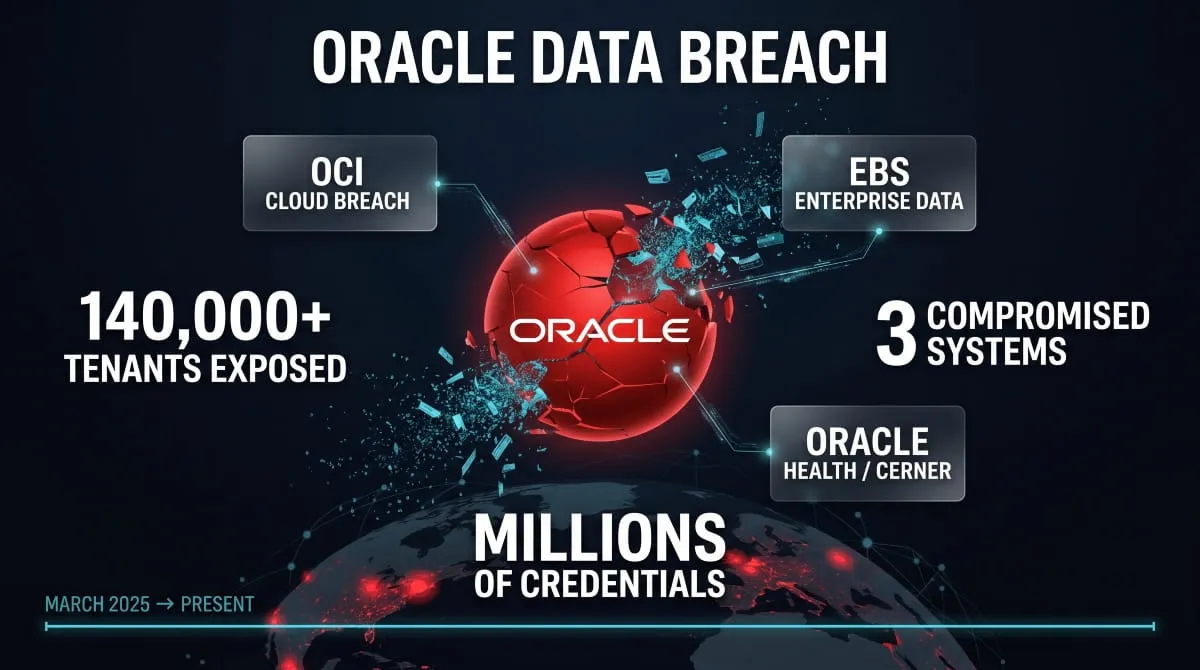
The Oracle data breach refers to a series of confirmed security incidents in 2025 in which unauthorized actors gained access to Oracle’s cloud infrastructure and several of its enterprise product lines. Unlike a single, contained intrusion, what emerged over the course of the year was a multi-system compromise, affecting Oracle’s cloud environments, its healthcare division, and its legacy enterprise software, each with its own scope, timeline, and set of victims.
At the center of the story is a fundamental conflict: Oracle publicly denied any breach had occurred while simultaneously notifying affected customers through private channels. That gap between what Oracle said publicly and what it told clients behind closed doors drew federal attention, legal action, and sustained media scrutiny throughout 2025.
Which Oracle Products Were Breached?
The 2026 Oracle breach was not confined to a single product. Three distinct systems were compromised, each affecting a different segment of Oracle’s customer base.
Oracle Cloud Infrastructure (OCI) was the first to surface publicly, with threat intelligence firm CloudSEK reporting that login credentials, SSO tokens, and encrypted passwords belonging to thousands of Oracle Cloud tenants had been exposed. Oracle’s Gen 1 legacy cloud environment was specifically implicated as the entry point.
Oracle E-Business Suite (EBS) emerged as a second, separate compromise, with breaches confirmed at multiple named organizations, including the Washington Post, Cox Enterprises, LKQ Corporation, and Dartmouth, among others. The EBS incidents were reported across November and December 2025, suggesting a sustained campaign rather than a one-time intrusion.
Oracle Health, formerly Cerner, was hit in a third incident that directly compromised patient data at U.S. hospitals. This breach carried the most serious real-world consequences, prompting Oracle to issue direct warnings to its healthcare customers and drawing immediate regulatory scrutiny given the sensitivity of the exposed records.
How Many Records and Companies Are Affected?
The full scale of the Oracle breach remains difficult to pin down precisely, in part because Oracle has been selective about what it discloses publicly. CloudSEK’s initial findings identified data belonging to over 140,000 Oracle Cloud tenants, with millions of credential records allegedly offered for sale on dark web forums. Confirmed EBS victims include several large enterprises across media, logistics, and technology sectors, though security researchers believe the published company list represents only a fraction of total exposure.
On the healthcare side, Oracle Health’s breach affected an unspecified number of U.S. hospital systems, with patient records, including data inherited from the Cerner acquisition, confirmed as compromised.
When Did the Breach First Come to Light?
The Oracle breach became public knowledge in early March 2025, when CloudSEK published its findings after discovering Oracle Cloud credentials being actively sold on a cybercriminal forum. The threat actor behind the listing claimed to have exfiltrated data from Oracle’s login infrastructure, including SSO endpoints and LDAP data.
Oracle responded with an immediate denial, stating that no breach of Oracle Cloud had occurred. That position became increasingly difficult to maintain as independent researchers verified samples of the leaked data, CISA issued a public advisory warning organizations to review their Oracle Cloud exposure, and reports emerged that Oracle had been quietly contacting affected customers, contradicting its own public statements.
The EBS and Oracle Health incidents followed later in the year, extending what had initially appeared to be a contained cloud security event into a much broader, multi-product security failure spanning most of 2025.
Oracle Denies, Then Admits: The Full Confirmation Timeline
The story of the Oracle data breach is, in many ways, a story about disclosure, or the deliberate avoidance of it. What unfolded over several months in 2025 was a slow, forced acknowledgment by one of the world’s most powerful enterprise software companies, driven not by internal transparency but by independent researchers, federal agencies, and mounting public evidence that its denials no longer held.
Initial Denial: “There Has Been No Breach of Oracle Cloud”
When CloudSEK’s findings first went public in March 2025, Oracle’s response was immediate and unequivocal. The company issued a statement asserting that no breach of Oracle Cloud had occurred and that the credentials being circulated online did not originate from its cloud infrastructure. Oracle pointed to the age of some data samples as evidence that the claims were either fabricated or irrelevant to its current environment.
For a brief window, that denial held in the press. Oracle is a $140 billion company with decades of enterprise credibility. When it says nothing happened, the default assumption in many boardrooms is to believe it.
That assumption didn’t last long.
CloudSEK’s Discovery and Public Disclosure
The breach first came to light through CloudSEK. This threat intelligence firm identified a threat actor on a prominent cybercriminal forum actively selling data purportedly extracted from Oracle Cloud’s login infrastructure. The listing included SSO tokens, encrypted credentials, LDAP data, and what appeared to be tenant-level records from Oracle’s Gen 1 cloud environment, with the seller claiming access to data belonging to over 140,000 Oracle tenants.
CloudSEK did not simply take the claim at face value. Researchers verified samples of the leaked data against known Oracle Cloud customers and found matches that were difficult to explain away as fabricated. When their findings went public, they effectively handed the security community and the press a documented basis to challenge Oracle’s denial directly.
It was the CloudSEK Oracle breach disclosure that turned a forum post into a global cybersecurity story.
Oracle Privately Confirms Breach to Customers
While Oracle was maintaining its public denial, a different conversation was happening behind closed doors. Reports later confirmed by multiple sources emerged that Oracle had been contacting affected customers privately, informing them that their data had been compromised and advising remediation steps.
This private confirmation, issued without any corresponding public statement, became the most damaging element of Oracle’s handling of the breach. It is clearly established that Oracle knew a breach had occurred, understood which customers were affected, and deliberately chose to manage that information out of public scrutiny. For affected organizations, many of whom learned of their own exposure through third-party researchers rather than directly from Oracle, the lack of proactive, transparent notification was a serious breach of trust on top of the security incident itself.
CISA Issues Oracle Cloud Warning
As the evidence mounted, the U.S. Cybersecurity and Infrastructure Security Agency stepped in. CISA issued a public advisory urging organizations that use Oracle Cloud to treat the situation as an active threat, reviewing access logs, rotating credentials, and monitoring for signs of unauthorized activity tied to the compromised SSO and login infrastructure.
The CISA Oracle breach warning was significant for two reasons. First, it validated what independent researchers had been saying for weeks, lending federal authority to findings that Oracle had dismissed. Second, it expanded the audience of concern well beyond the cybersecurity community, putting IT and security teams across thousands of enterprises on notice that Oracle’s denial was not a sufficient basis for inaction.
Oracle Finally Acknowledges the Breach Publicly
Oracle’s full public acknowledgment came gradually and without the kind of clear, consolidated statement that affected organizations had been waiting for. Rather than a single definitive admission, Oracle’s confirmation emerged from a combination of customer notifications, media coverage of those notifications, and updated guidance that implicitly acknowledged the breach.
By the time Oracle finally acknowledged the data breach in explicit terms, the damage to its credibility had largely already been done. The months-long gap between the CloudSEK disclosure, the private customer confirmations, and any formal public statement left a trail of corporate evasion that became central to the class action lawsuits filed in the breach’s aftermath.
What Oracle’s timeline ultimately illustrates is a pattern seen repeatedly in major corporate breaches: the cover-up, or in this case, the studied ambiguity, often compounds the harm more than the breach itself.
Affected Oracle Systems Breakdown
One of the most important things to understand about the 2025 Oracle breach is that it was not a single intrusion into a single system. What emerged over the course of the year was a pattern of compromise across multiple Oracle product lines, each affecting a different customer base, exposing different categories of data, and carrying different downstream consequences. Understanding which system was breached matters enormously if your organization runs any part of its operations on Oracle infrastructure.
Oracle Cloud Infrastructure (OCI) Breach
The OCI breach was the first to surface publicly and the one that triggered Oracle’s now-infamous denial. The compromise targeted Oracle’s cloud environment at the infrastructure level, specifically the authentication layer, exposing login credentials, encrypted passwords, and tenant-level access data belonging to organizations hosted on Oracle Cloud.
The scope was significant. CloudSEK’s research identified data associated with over 140,000 Oracle Cloud tenants, including persistent access credentials that, if left unrotated, give attackers long-term footholds inside enterprise environments. For organizations using Oracle Cloud to run core business workloads, the OCI security breach exposed systems beyond the initial intrusion; every system accessible with those compromised credentials became a potential secondary target.
Oracle E-Business Suite (EBS) Breach, November & December 2025
The Oracle E-Business Suite breach arrived later in the year and, in many ways, hit closer to home for large enterprises. EBS is Oracle’s flagship on-premise and hybrid enterprise application platform, used by major organizations for finance, HR, supply chain, and procurement. A breach here doesn’t just expose cloud credentials; it exposes the operational data sitting inside some of the most business-critical systems an organization runs.
Confirmed EBS victims emerged across November and December 2025, with named organizations including the Washington Post, Cox Enterprises, LKQ Corporation, and Dartmouth appearing in published breach reports. The pattern of incidents across two consecutive months suggested a coordinated campaign rather than an isolated intrusion by attackers who had identified a vulnerability in EBS deployments. It was systematically exploiting it across multiple targets.
The Oracle e-business suite breach drew particular attention because many of the affected organizations were large, well-resourced enterprises with mature security teams, a reminder that EBS vulnerabilities, when exploited at the infrastructure level, can bypass conventional perimeter defenses entirely.
Oracle Health / Cerner Breach, Patient Data at U.S. Hospitals
Of all the Oracle systems compromised in 2025, the Oracle Health breach carried the most serious real-world consequences. Oracle Health, built on the foundation of Cerner, the electronic health records giant Oracle acquired in 2022, provides clinical and administrative software to hospitals and health systems across the United States. The data it holds is among the most sensitive that exists: patient medical records, treatment histories, and personal health information protected under federal law.
The Oracle Health data breach confirmed that patient data at multiple U.S. hospital systems had been compromised. Oracle responded by issuing direct warnings to its healthcare customers, one of the few proactive disclosure steps the company took throughout the entire breach saga, acknowledging that records from the Cerner infrastructure had been accessed without authorization.
For hospital systems, the implications extend beyond regulatory exposure under HIPAA. Patients whose records were compromised face risks ranging from medical identity theft to the long-term misuse of sensitive health data on dark web markets. The Oracle Cerner breach stands as the human cost behind what might otherwise read as a story about enterprise software and cloud infrastructure.
Oracle Fusion & SSO Breach
Oracle Fusion, Oracle’s cloud-native ERP and HCM suite, and its associated Single Sign-On infrastructure were also implicated in the 2025 breach. The SSO compromise is particularly consequential because of what single sign-on actually does: it serves as the master key to an organization’s entire Oracle application ecosystem. A compromised SSO credential doesn’t just open one door; it opens all of them.
The Oracle Fusion data breach and SSO exposure meant that organizations using Oracle Fusion for enterprise resource planning, human capital management, or financial operations needed to treat every connected application as potentially accessible. Credential rotation alone was insufficient without a full audit of what those credentials had touched during the exposure window.
Oracle NetSuite Breach
Oracle NetSuite, the cloud ERP platform widely used by mid-market businesses for accounting, inventory, and e-commerce operations, also appeared in breach reporting throughout 2025. While the NetSuite incidents were less extensively documented than the OCI or EBS compromises, the Oracle Cloud Breach NetSuite reports raised serious concerns for the SMB and mid-market companies that rely on NetSuite as their primary business management platform.
For many of these organizations, NetSuite holds the entirety of their financial records, customer data, and vendor relationships, making any unauthorized access a significant operational and legal risk, even if the breach didn’t generate the same volume of headlines as the enterprise-facing incidents.
Oracle Gen 1 / Legacy System Breach
At the technical root of the OCI compromise sits Oracle’s Gen 1 cloud infrastructure, the legacy environment that predates Oracle’s current cloud architecture and that the company has been migrating customers away from for several years. The Oracle Gen 1 data breach is significant precisely because legacy systems are, by their nature, harder to patch, slower to monitor, and more likely to carry unresolved vulnerabilities that modern environments have long since addressed.
Security researchers identified Oracle’s Gen 1 environment as the likely initial access point for the broader cloud infrastructure breach. This finding underscores a risk pattern common across enterprise technology: organizations and vendors alike tend to underinvest in securing systems they consider transitional or end-of-life, even when those systems remain live and connected to production data. In Oracle’s case, that underinvestment appears to have been the opening that attackers needed.
Which Companies Were Affected? (Confirmed Breach Victims)
As the Oracle breach story developed throughout 2025, one of the most closely watched questions was simple: whose data was actually taken? Oracle’s reluctance to publish a comprehensive victim list meant that confirmed names emerged piecemeal, through security researchers, investigative reporting, and court filings rather than any organized disclosure from Oracle itself.

What follows are the organizations that have been publicly confirmed or credibly reported as affected by the Oracle E-Business Suite breach and related incidents. This list should not be read as exhaustive. Security researchers and legal filings suggest the actual number of compromised organizations is substantially larger than the publicly named figure.
University of Pennsylvania (Penn) Oracle Breach
The University of Pennsylvania was among the named institutions confirmed as an Oracle breach victim, with the compromise linked to its Oracle E-Business Suite deployment. Penn’s EBS environment supports a range of administrative and financial operations across one of the largest private university systems in the United States, making the exposure particularly significant given the volume of employee, vendor, and institutional financial data the platform typically holds.
The UPenn Oracle data breach drew attention both because of the institution’s size and because it illustrated that the EBS campaign was not limited to corporate targets. Higher education institutions running legacy Oracle deployments were equally exposed.
Dartmouth Oracle E-Business Suite Breach
Dartmouth College was separately confirmed as an Oracle EBS breach victim, with its compromise attributed to the same campaign targeting E-Business Suite deployments across late 2025. Like Penn, Dartmouth’s EBS environment underpins critical administrative infrastructure, and like Penn, its appearance on the confirmed victim list signaled that the attackers behind the EBS incidents were moving systematically across sectors, not targeting a single industry vertical.
LKQ Corporation Oracle EBS Breach
LKQ Corporation, one of North America’s largest distributors of automotive replacement parts with operations spanning the U.S., Europe, and beyond, was confirmed as a victim of an Oracle EBS breach. The LKQ Oracle EBS data breach is notable for the scale of operational data potentially exposed: a company of LKQ’s size running EBS for supply chain and distribution management holds an extensive record set covering suppliers, logistics partners, financial transactions, and customer accounts.
For a business operating at that scale across multiple geographies, the downstream risk of a compromised EBS environment extends well beyond the initial data loss.
Cox Enterprises Oracle E-Business Suite Breach
Cox Enterprises, the privately held media and automotive services conglomerate behind Cox Communications, Cox Automotive, and a portfolio of media properties, was confirmed as an Oracle EBS victim in the November 2025 reporting. The Cox Enterprises Oracle e-business suite data breach was one of the higher-profile corporate names to appear on the confirmed victim list, both because of Cox’s scale as a multi-billion-dollar private company and because its diverse business lines mean the compromised EBS data could span multiple industries and customer bases simultaneously.
GlobalLogic Oracle Data Breach
GlobalLogic, the digital engineering services firm owned by Hitachi, also appeared in Oracle data breach reporting as a confirmed or credibly attributed victim. GlobalLogic’s business model, which provides software engineering and product development services to enterprise clients across technology, healthcare, and financial services, means that a compromise of its internal systems could pose a third-party risk. Client project data, proprietary code, and engagement records may all reside in environments at risk.
Washington Post Oracle EBS Breach
The Washington Post’s confirmation that it was an Oracle E-Business Suite breach victim added a significant media dimension to the story. The Washington Post Oracle breach was reported as part of the broader EBS campaign, with the publication’s internal Oracle environment compromised during the same period as other confirmed victims. For a news organization that regularly covers data privacy and corporate security failures, the irony was not lost on observers, and the breach served as a pointed reminder that no sector, including the media, is immune to enterprise software vulnerabilities.
Full Company & Domain List, What’s Been Published
Beyond the named organizations above, security researchers published broader lists of domains and company identifiers appearing in the Oracle breach data, suggesting that the confirmed named victims represent only the visible surface of a much larger compromise. Threat intelligence platforms and dark web monitoring services identified hundreds of organizational domains in the leaked credential sets, spanning industries including finance, healthcare, logistics, higher education, and government contracting.
Oracle has not released its own comprehensive list of affected organizations. The breach notification process, where it occurred at all, happened through private outreach rather than public disclosure, leaving many potentially affected companies unaware that their Oracle environments were implicated until researchers or journalists brought the data to light.
If your organization runs Oracle Cloud, Oracle EBS, or Oracle Health infrastructure and has not yet verified its exposure status, the most reliable first step is an active check against known breach data rather than waiting for Oracle to make contact.
Check whether your organization appears in the Oracle breach data now. Run a Free Oracle Breach Check →
What Data Was Exposed in the Oracle Breach?
Understanding what was actually taken matters as much as knowing which systems were hit. The category of exposed data determines the severity of downstream risk for the organizations breached, their customers, and, in the case of Oracle Health, for individual patients who had no direct relationship with Oracle at all. Across the three primary breach vectors, the data exposed spans three distinct and serious categories.
Credentials, SSO Tokens, and Password Hashes
The Oracle Cloud Infrastructure breach exposed what security professionals consider among the most dangerous categories of stolen data: authentication credentials. The compromised records included usernames, encrypted password hashes, SSO tokens, and LDAP authentication data belonging to Oracle Cloud tenants.
What makes this category particularly damaging is persistence. Unlike a stolen credit card number, which becomes useless once the card is cancelled, compromised SSO tokens and credential sets can provide attackers with sustained, legitimate-looking access to enterprise environments for weeks or months before detection. In the Oracle breach, the SSO compromise was especially consequential because Oracle’s single sign-on infrastructure serves as the gateway to an organization’s entire Oracle application stack. One set of valid credentials doesn’t open one door; it opens every door those credentials were authorized to reach.
For organizations that had not rotated credentials or audited access logs in the weeks following the initial CloudSEK disclosure, Oracle’s delayed public acknowledgment significantly extended the window of potential unauthorized access. Attackers operating with valid SSO tokens during that period would have appeared indistinguishable from legitimate users in standard access logs.
The Oracle data breach credentials that surfaced on dark web forums were offered in bulk, structured datasets organized by tenant domain, making it straightforward for buyers to target specific organizations rather than sifting through undifferentiated data. That level of organization suggests the exfiltration was deliberate and systematic, not opportunistic.
Patient Data Compromised in Oracle Health / Cerner Breach
The data exposed in the Oracle Health breach falls into a completely different category of severity. Electronic health records contain some of the most sensitive personal information, including medical histories, diagnoses, treatment records, prescription data, insurance information, and demographic details that tie it all to a specific individual. Unlike financial data, medical information cannot be changed. A patient whose health records are compromised carries that exposure for life.
Oracle Health’s infrastructure, built on the Cerner electronic health records platform acquired in 2022, held patient records from multiple U.S. hospital systems. The Oracle health breach confirmed that this data had been accessed without authorization, prompting Oracle to issue direct warnings to its healthcare customers, a notable departure from the evasive posture it maintained throughout the cloud infrastructure breach.
The regulatory consequences of HIPAA violations involving patient data are significant. Healthcare organizations that relied on Oracle Health’s infrastructure and whose patient records were compromised face mandatory breach notification obligations, potential federal investigation, and civil liability, regardless of whether the vulnerability originated in their own systems or in Oracle’s. The Oracle Cerner data breach effectively shifted a compliance and legal burden onto hospital systems that had no direct role in creating the vulnerability that was exploited.
Beyond the regulatory dimension, the patient data exposed in the Oracle Health breach has real human consequences. Medical identity theft, where stolen health records are used to obtain prescriptions, insurance reimbursements, or medical procedures fraudulently, is one of the fastest-growing forms of identity fraud, and health records sourced from a breach of this scale represent significant raw material for such abuse.
Enterprise EBS Records and Business Data
The Oracle E-Business Suite breach exposed a different but equally consequential category of data: the operational backbone of large enterprises. EBS environments hold the financial ledgers, procurement records, vendor contracts, payroll data, HR records, and supply chain information that organizations use to run their day-to-day operations. For the confirmed EBS victims, Cox Enterprises, LKQ Corporation, the Washington Post, Dartmouth, Penn, and others, the compromised data represents a detailed operational map of their business.
The practical risks here are several. Exposed vendor and supplier records can be weaponized in business email compromise (BEC) attacks, in which attackers impersonate known vendors to redirect payments or extract sensitive information. Payroll and HR data pose a direct risk of identity theft to employees. Financial records provide intelligence that competitors or adversarial actors could exploit. And procurement data, particularly for organizations operating in sensitive sectors, can reveal strategic relationships and operational dependencies that were never intended to be public.
What distinguishes the EBS data exposure from the credential breach is that credentials can be rotated. The business records extracted from compromised EBS environments cannot be unexposed. Once operational data is in circulation on dark web markets, the risk it creates is permanent, which is why ongoing dark web monitoring, rather than a one-time credential reset, is the appropriate long-term response for any organization confirmed or suspected to be among the Oracle breach victims.
Oracle’s Official Response and Breach Notifications
How a company responds to a data breach often matters as much as the breach itself. Affected organizations need timely, accurate information to contain damage, notify their own users, and meet legal disclosure obligations. What Oracle delivered instead was a communications strategy defined by deflection, selective disclosure, and a months-long gap between what the company knew and what it was willing to say publicly.

Oracle’s Public Statements vs. Private Customer Notifications
Oracle’s official public position, maintained through the early weeks of the breach story, was that no breach of Oracle Cloud had occurred. The company’s statement was categorical, not hedged, not under investigation, not a “we are looking into it.” A flat denial.
Behind that denial, a different reality was taking shape. Multiple reporting outlets and affected customers confirmed that Oracle had been reaching out privately, through direct customer notifications and account team communications, to inform specific organizations that their data had been compromised and to recommend remediation steps, including credential rotation and access log review.
The contradiction between Oracle’s public statements and its private breach notifications ultimately unraveled the company’s position. Organizations that received private outreach from Oracle while the company simultaneously denied any breach in the press were left in an untenable position: act on the private warning while publicly being told nothing happened, or wait for a public acknowledgment that Oracle showed no urgency to provide.
This divergence, oracle admits breach privately while maintaining public denial, became the central narrative thread that journalists, regulators, and plaintiff attorneys followed throughout 2025. It also raised a question that remains relevant for any organization evaluating its Oracle relationship: if Oracle’s first instinct in a breach of this scale was to minimize public disclosure, how confident can customers be that they received complete information even through the private channel?
Oracle Health Warning to Healthcare Customers
The one area where Oracle’s disclosure posture showed meaningful urgency was its healthcare division. Oracle Health issued direct warnings to hospital systems and healthcare customers confirming that patient data had been compromised in the Cerner infrastructure breach, a notably more proactive step than the company took in response to the cloud infrastructure and EBS incidents.
The reason for that difference is almost certainly regulatory. Healthcare data breaches trigger mandatory notification obligations under HIPAA, with defined timelines, federal oversight, and significant penalties for non-compliance. Oracle Health’s warning to healthcare customers was less a demonstration of transparency than a recognition that the legal cost of silence in a healthcare breach context is substantially higher than in an enterprise software context.
Oracle’s warning to health customers about a patient data breach was one of the few unambiguous, proactive disclosure moments in the entire Oracle breach saga. It also set an uncomfortable contrast: Oracle found the urgency to warn hospital systems about compromised patient records while simultaneously telling the broader market that no breach had occurred in its cloud infrastructure. The inconsistency did not go unnoticed by regulators or the legal teams that subsequently filed class action suits.
For healthcare organizations on the receiving end of Oracle’s notification, the warning itself created an immediate compliance burden. HIPAA breach notification requirements impose obligations on covered entities, the hospitals and health systems, not just on the technology vendor. Oracle’s warning effectively started a clock for those organizations, regardless of whether Oracle itself was meeting its own disclosure timelines.
What Oracle Has (and Hasn’t) Disclosed About the Investigation
As of the time of this writing, Oracle’s public disclosure of the breach investigation remains incomplete by any standard. Oracle has not published a comprehensive incident report. It has not released a full list of affected organizations or customers. It has not provided a detailed technical account of how the intrusion occurred, which vulnerabilities were exploited, or what evidence supports its initial claim that the breach was limited to legacy Gen 1 infrastructure.
What Oracle’s statement on the data breach has amounted to, in practical terms, is a series of private notifications, a gradual and implicit acknowledgment forced by external evidence, and a posture of managed ambiguity that kept the company from ever having to make a single, clear, accountable public statement.
What Oracle has not disclosed is arguably more significant. The full scope of the OCI breach, how many tenants were actually affected, how long unauthorized access persisted, and whether any of the compromised SSO credentials were used to move laterally into customer environments, remains publicly unresolved. The EBS breach timeline, including how the initial vulnerability was identified and whether Oracle had prior warning signs it failed to act on, has not been addressed in any public Oracle breach statement. And the forensic details of the Oracle Health compromise, including which hospital systems were affected and how many patients’ records were exposed, have not been disclosed in any consolidated form.
For organizations making decisions about their Oracle infrastructure today, that absence of disclosure is itself a data point. A vendor that responds to one of the most significant enterprise cloud breaches of 2025 with sustained ambiguity is a vendor whose future incident response posture deserves serious scrutiny.
Legal Fallout, Lawsuits, and Regulatory Action
When a breach of this scale is handled with the level of opacity Oracle demonstrated throughout 2025, legal consequences are not a possibility; they are a certainty. The combination of a massive credential exposure, a confirmed patient data compromise, a months-long public denial, and selective private notifications created precisely the conditions that plaintiff attorneys, federal agencies, and state regulators are structured to respond to. The legal fallout from the Oracle data breach is still developing, but its early shape is already significant.
Oracle Data Breach Class Action Lawsuit
Multiple class action lawsuits stemming from the breach were filed in the aftermath, targeting both the security failures that enabled the intrusion and Oracle’s conduct in the months that followed. The legal claims center on several distinct but related arguments: that Oracle failed to implement adequate security measures to protect customer and patient data, that Oracle’s initial denial constituted a deliberate misrepresentation to affected parties, and that Oracle’s delay in issuing transparent public notifications prevented organizations and individuals from taking timely protective action.
The Oracle data breach lawsuit filings draw particular attention to the gap between Oracle’s public denials and its private customer notifications, a documented contradiction that gives plaintiff attorneys a concrete basis to argue that Oracle knew the breach was real, knew who was affected, and made an active choice to manage that information away from public view. In class action litigation, that kind of documented discrepancy between internal knowledge and public statements is often more damaging than the underlying security failure itself.
For patients whose data was exposed through the Oracle Health and Cerner breach, a separate legal track exists under HIPAA’s private right of action framework, with healthcare-specific claims that carry their own evidentiary standards and damage calculations. The Oracle health data breach lawsuits represent a distinct category of litigation with potentially significant per-plaintiff exposure given the sensitivity of the records involved.
CISA’s Role and Federal Response
The federal response to the Oracle breach was anchored by CISA, the Cybersecurity and Infrastructure Security Agency, which issued a public advisory urging organizations using Oracle Cloud to treat the situation as an active threat requiring immediate action. The CISA Oracle breach advisory directed organizations to review authentication logs, rotate credentials tied to Oracle Cloud environments, and monitor for indicators of compromise consistent with the reported intrusion methods.
The significance of CISA’s intervention was twofold. At the practical level, it gave security teams across thousands of enterprises the federal validation they needed to escalate remediation efforts internally; a CISA advisory carries organizational weight that a threat intelligence firm’s blog post, however well-documented, does not always command. At the political level, the Oracle Cloud potential breach warning from CISA represented an implicit rebuke of Oracle’s public denial, signaling that federal cybersecurity authorities assessed the threat as credible and serious regardless of what Oracle was saying publicly.
CISA’s involvement also opened the door to broader federal scrutiny. Agencies with oversight responsibilities across healthcare, finance, and critical infrastructure began examining their own exposure to Oracle systems, and the breach entered the policy conversation around vendor security accountability and enterprise cloud risk that has been building in Washington throughout the mid-2020s.
Oracle Data Breach Settlement: What to Expect
As of now, the Oracle data breach settlement process is in its early stages, with class-action litigation still working its way through the courts. Based on the scale of the breach, documented handling failures, and the categories of data involved, the legal and financial resolution is likely to follow a pattern established by comparable enterprise breach cases. However, several factors suggest the eventual settlement or judgment could be substantial.
The credential breach affecting over 140,000 Oracle Cloud tenants establishes a large potential plaintiff class. The patient data exposure through Oracle Health adds a healthcare liability dimension with its own multiplier effect on damages. And Oracle’s documented public denial, followed by a private acknowledgment, provides plaintiffs with an aggravating-conduct argument that goes beyond simple negligence. Courts and juries in comparable cases have consistently treated the deliberate withholding of breach information as a factor that increases damages beyond what a straightforward security failure would warrant.
The Oracle data breach settlement payout date remains uncertain, as class action litigation of this complexity rarely resolves quickly. Affected individuals and organizations should expect the legal process to extend over multiple years, with preliminary settlements or court-ordered discovery potentially producing new disclosures about the breach’s true scope before any final resolution is reached.
For organizations and individuals waiting on legal outcomes, that timeline is a reason to act independently rather than wait. Whatever settlement eventually emerges will not undo the exposure that already occurred, and the dark web data circulating from this breach will remain in play long after any courtroom resolution.
How to Check If Your Organization Was Exposed
Oracle’s failure to publish a comprehensive victim list means that thousands of organizations potentially affected by the breach have had no official notification to act on. Waiting for Oracle to make contact is not a viable security strategy. The credential data, domain records, and organizational identifiers from the breach have been circulating on dark web forums since early 2025, which means the exposure clock started long before most affected companies were aware there was anything to check.

The good news is that you do not need to wait for Oracle or a class action court filing to find out where your organization stands.
Using DeXpose’s Free Oracle Breach Check Tool
DeXpose built a dedicated Oracle breach-check tool specifically in response to the 2025 incidents, designed to give security teams, IT administrators, and business owners a fast, reliable way to determine whether their organization’s data appears in breach records identified and indexed from the Oracle compromise.
The tool checks your domain or organizational identifier against DeXpose’s dark web intelligence database, which includes data sourced from the Oracle Cloud credential exposure, the EBS breach records, and related dark web forum activity tied to the 2025 incidents. It takes seconds to run and returns actionable results, not a generic risk score, but a direct answer to the question every affected organization needs answered first: is our data in there?
There is no cost to run the check. No sales process. Just a direct lookup against the breach data that matters right now.
Run Your Free Oracle Breach Check →
What to Do If Your Credentials Appear in the Oracle Breach
If your organization’s data appears in the Oracle breach results, the response needs to move quickly and in the right order. The instinct to immediately reset all passwords is correct. Still, credential rotation alone is insufficient if you do not first understand what those credentials had access to during the exposure window.
Start with an access log audit. Pull authentication logs for your Oracle Cloud and EBS environments going back to at least January 2025, the period before the breach became public, and look for login activity that falls outside normal usage patterns. Unusual access times, unfamiliar IP addresses, or access to systems that specific credentials would not typically touch are the indicators that matter most. If you find anomalies, treat them as confirmed intrusion activity until proven otherwise.
Once you have a clear picture of the exposure window, rotate all affected credentials, SSO tokens, LDAP passwords, API keys, and any service account credentials that touch Oracle infrastructure. Do not limit the rotation to the specific credentials that appeared in breach data; rotate anything that shares authentication infrastructure with the compromised accounts, because lateral credential reuse is one of the most common techniques attackers employ after an initial access event.
Notify your legal and compliance teams immediately. Depending on your industry and jurisdiction, a confirmed appearance in the Oracle breach data may trigger mandatory notification obligations to regulators, customers, or both. The timeline for those obligations is often shorter than organizations expect, particularly in healthcare and finance, and the penalty for missing a notification deadline is compounded when regulators can see that the underlying breach was publicly known months before the notification was filed.
Finally, do not treat this as a closed incident once credentials are rotated. The data from the Oracle breach is in circulation and will remain so. The risk does not end when your internal remediation does.
Monitoring for Ongoing Dark Web Exposure After the Breach
A one-time breach check determines whether your data was affected by the Oracle incident. It does not answer the question of what happens next, and in the context of a breach this large, that is the more important question for long-term security posture.
Credential sets and organizational data from major breaches do not disappear from dark web markets after the initial sale. They get repackaged, resold, and recirculated through criminal forums for months and years after the original incident. An organization that checks its Oracle breach exposure today and finds nothing may still find its data surfacing three months from now as the breach records are redistributed through secondary markets.
This is why ongoing dark web monitoring is the appropriate long-term response to the Oracle breach, not a one-time check, but continuous visibility into whether your organization’s credentials, domains, or data are appearing in new dark web sources as the breach data continues to circulate.
DeXpose’s dark web monitoring platform provides exactly that: persistent surveillance across dark web markets, criminal forums, paste sites, and breach databases, with real-time alerts when your organization’s data surfaces anywhere in the ecosystem. For organizations confirmed or suspected to be in the Oracle breach, it closes the gap that a single credential rotation cannot, and ongoing awareness of a threat landscape that does not stop moving just because your internal remediation did.
Start Monitoring Your Dark Web Exposure →
Oracle Breach vs. Past Oracle Security Incidents
Oracle is not a company without a security history. Long before 2025, the company had faced documented breaches, vulnerability disclosures, and criticism over its approach to transparency when things went wrong. Understanding that history matters, not to pile on, but because it provides essential context for evaluating whether the 2025 incidents represent an isolated failure or a pattern with deeper roots.

Oracle Data Breach History (2016–2024)
The most significant pre-2025 Oracle security breach on record was the 2016 compromise of Oracle’s MICROS point-of-sale division, at the time, one of the largest POS system providers in the world, serving hundreds of thousands of hospitality, retail, and food service locations globally. The Oracle Micros breach was attributed to a Russian cybercriminal group. It resulted in malware being planted on MICROS support systems, potentially exposing payment and credential data across a vast network of hospitality businesses. Oracle’s response at the time drew criticism for being slow and limited in scope, a preview, in retrospect, of the communication posture it would adopt nine years later.
In the years that followed, Oracle faced a steady stream of reported vulnerabilities across its product portfolio, including critical patches for Oracle Database, Oracle WebLogic Server, and Oracle E-Business Suite issued through its quarterly Critical Patch Update program. Several of these vulnerabilities, when left unpatched by customers or disclosed with insufficient urgency by Oracle, were exploited in the real world. The Oracle-documented Oracle security breaches between 2016 and 2024 were largely product-level vulnerabilities rather than infrastructure-level compromises, serious but contained to specific systems and customer environments rather than Oracle’s own cloud backbone.
The Oracle data breach in 2024 prompted renewed scrutiny of Oracle’s cloud security posture as enterprise cloud adoption accelerated and threat actors increasingly targeted cloud infrastructure providers as high-value single points of failure. By the time 2025 arrived, Oracle’s Gen 1 cloud environment, already considered legacy by Oracle’s own roadmap, had been carrying unresolved risk that the company had not adequately communicated to the customers still operating on it.
What Makes the 2025 Cloud Breach Different
Every major breach has distinguishing characteristics. What separates the 2025 Oracle cloud breach from every prior Oracle security incident is not just its scale; it is the combination of factors that converged simultaneously and the way Oracle chose to respond to them.
Previous Oracle security incidents were largely contained to specific product vulnerabilities that affected customers who had failed to apply available patches. The 2025 breach was different in origin: it began inside Oracle’s own infrastructure, in a legacy cloud environment that Oracle controlled and was responsible for securing. Customers did not fail to patch; they were exposed because Oracle’s own systems were compromised. That shifts the accountability calculus entirely.
The multi-system scope is also without precedent in Oracle’s breach history. Prior incidents touched one product line. The 2025 incidents compromised Oracle Cloud Infrastructure, Oracle E-Business Suite, Oracle Health, Oracle Fusion, and Oracle’s SSO layer, essentially a cross-section of Oracle’s entire enterprise product portfolio, hitting cloud customers, on-premise EBS users, and healthcare organizations in parallel. No prior Oracle data breach came close to that breadth of impact.
Then there is the disclosure conduct. Oracle has faced criticism for slow patching and limited transparency before. Still, it had never previously issued a categorical public denial of a breach while simultaneously sending private notifications to affected customers confirming that breach. That specific contradiction, documented and reported across multiple outlets, represents a new category of reputational and legal exposure for Oracle. It transformed what might have been a serious but manageable security incident into a story about corporate conduct. That shift drew class-action attorneys, CISA, and sustained media attention in ways prior Oracle security incidents never did.
The 2025 Oracle Cloud breach is, in the end, a different kind of event than anything in Oracle’s prior security history. Not because Oracle had never been breached before, but because never before had the breach been this broad, this deep inside Oracle’s own infrastructure, and handled with this degree of public evasion. That combination is what makes it the defining Oracle security event of the decade.
What Should Organizations Do Right Now?
Knowing your organization may have been caught in the Oracle breach is not the same as knowing what to do about it. The gap between awareness and action is where the real damage compounds, where unrotated credentials get exploited, where notification deadlines get missed, and where data that could have been contained continues to circulate. If your organization runs any Oracle infrastructure implicated in the 2025 incidents, the time to act was months ago. The second-best time is now.
Immediate Steps: Credential Reset and Access Audit
The priority is not a password reset. It is an audit. Rotating credentials before understanding what those credentials accessed during the exposure window is like changing the locks without first checking whether someone is still inside.
Pull authentication and access logs for all Oracle environments, Cloud, EBS, Health, Fusion, going back to at least January 2025. Look specifically for login activity from unfamiliar IP addresses, access to systems outside the normal usage pattern for specific accounts, and any service account activity that does not correspond to scheduled or documented processes. If your logging infrastructure does not go back that far, document that gap; it will matter in any subsequent regulatory review.
Once the audit establishes your exposure window, execute a full credential rotation. This means SSO tokens, LDAP passwords, API keys, and any service account credentials that authenticate against Oracle infrastructure, not just the accounts that appeared in breach data. Assume that any credential-sharing authentication infrastructure with a compromised account is itself at risk until proven otherwise. Enforce multi-factor authentication across all Oracle-connected accounts if it is not already in place, and review third-party integrations that use Oracle credentials for automated processes; these are frequently overlooked and represent a persistent re-entry point if left unaddressed.
Notify Affected Users and Review Breach Notification Obligations
Once your internal picture of the exposure is clear, the obligation to look outward begins. Depending on your industry, jurisdiction, and the category of data held in your Oracle environments, a confirmed appearance in the Oracle breach may trigger mandatory notification requirements with defined timelines that are already running.
Healthcare organizations operating on Oracle Health or Cerner infrastructure face HIPAA breach notification obligations requiring notice to affected patients within 60 days of discovering a breach, and regulators will consider the public CloudSEK disclosure and CISA advisory as markers of when discovery could reasonably have occurred, not just when Oracle formally notified you. Financial services organizations face parallel obligations under state and federal financial privacy regulations. Any organization holding personal data belonging to EU residents must assess its exposure against the GDPR’s 72-hour regulatory notification window.
Beyond regulatory obligations, there is a practical and reputational case for proactive user notification. Organizations that communicate clearly and early about what happened, what data was involved, and what they are doing in response consistently fare better, legally and in terms of customer trust, than those whose affected users learn about the breach from a news article. Oracle’s own handling of this situation provides an instructive negative example: the companies that suffered the most reputational damage in the Oracle breach story were not those that were breached, but those perceived as slow or evasive in responding.
Work with legal counsel to map your specific notification obligations before communicating externally. The content, timing, and recipient list for breach notifications carry legal weight, and getting them wrong, either by over-disclosing prematurely or under-disclosing in a way that omits required information, creates liability independent of the breach itself.
Long-Term: Dark Web Monitoring for Post-Breach Exposure
Internal remediation addresses issues within your environment. It does not address what is happening outside it, and in the case of the Oracle breach, what is happening outside is the more persistent long-term threat.
The credential sets, domain records, and organizational data extracted in the Oracle breach are in active circulation on dark web markets and criminal forums. They will be repackaged, resold, and deployed in follow-on attacks, credential-stuffing campaigns, targeted phishing operations, and business email compromise attempts for months and years beyond the initial incident. An organization that completes its internal remediation and considers the matter closed is operating with a blind spot that attackers will eventually exploit.
Ongoing dark web monitoring closes that blind spot. Rather than a one-time check against known breach data, continuous monitoring provides real-time visibility into whether your organization’s credentials, domains, or internal data surface in new dark web sources as the Oracle breach records continue to circulate through secondary markets. It is the difference between knowing what was exposed in March 2025 and what is actively being traded about your organization today.
DeXpose monitors dark web markets, criminal forums, ransomware leak sites, and breach databases around the clock, alerting your team the moment your organization’s data appears anywhere in the ecosystem, not just in the sources that are already indexed. For organizations caught in the Oracle breach, it provides the persistent post-breach visibility that credential rotation alone cannot deliver.
Start Monitoring Your Dark Web Exposure →
Conclusion
The 2026 Oracle data breach was not a single event; it was a months-long unraveling of one of enterprise technology’s most trusted names, across multiple systems, affecting organizations that had every reason to expect better. What made it worse was not just the scale of the compromise but the deliberate ambiguity Oracle maintained while affected organizations waited for answers they deserved immediately.
The breach data is still circulating. The lawsuits are still developing. And the organizations that act now, auditing their exposure, rotating credentials, and putting continuous dark web monitoring in place, are the ones best positioned to limit what comes next.
Don’t wait for Oracle’s next statement. Find out where your organization stands today.
Frequently Asked Questions (FAQ’s)
Was Oracle really breached in 2026?
Yes. Oracle initially denied that a breach had occurred, but subsequently confirmed the incident through private customer notifications, while independent researchers at CloudSEK verified samples of the leaked data. CISA issued a public advisory urging organizations to treat the threat as real and take immediate protective action.
Which Oracle products were affected?
The 2026 Oracle breach impacted multiple product lines, including Oracle Cloud Infrastructure (OCI), Oracle E-Business Suite (EBS), Oracle Health (formerly Cerner), Oracle Fusion, Oracle NetSuite, and Oracle’s SSO authentication layer. Each incident affected a different customer base and exposed different categories of data.
Was patient data exposed in the Oracle Health / Cerner breach?
Yes. Oracle confirmed that patient data held within its Oracle Health and Cerner infrastructure was compromised, prompting direct warnings to affected U.S. hospital systems. The exposed records included sensitive personal health information protected under HIPAA, creating mandatory breach notification obligations for the healthcare organizations involved.
How do I know if my company’s data is in the Oracle breach?
Oracle has not published a comprehensive list of affected organizations, so waiting for direct notification is not a reliable strategy. DeXpose offers a free Oracle Breach Check tool at dexpose.io/oracle-breach-scan/ that checks your organization’s domain against indexed breach data from the 2026 Oracle incidents and returns results in seconds.
Is there an Oracle breach settlement or payout coming?
Multiple class action lawsuits have been filed against Oracle in connection with the 2026 breach, targeting both the security failures and Oracle’s conduct in denying and delaying disclosure. A formal settlement is likely, given the scale of the breach and the documented contradiction between Oracle’s public statements and private customer notifications. However, final resolution is expected to take several years.
What is Oracle’s official statement on the breach?
Oracle’s public response evolved from an outright denial, stating that no breach of Oracle Cloud had occurred, to a gradual, implicit acknowledgment driven by external evidence, CISA’s advisory, and media reporting on private customer notifications. Oracle has never issued a single, consolidated public statement confirming the full scope of the breach or detailing the results of its internal investigation.
Did CISA confirm the Oracle breach?
Yes. The U.S. Cybersecurity and Infrastructure Security Agency issued a public advisory in response to the Oracle Cloud breach, directing organizations to review access logs, rotate credentials, and monitor for indicators of compromise. CISA’s intervention effectively validated Oracle’s publicly dismissed findings and signaled that federal authorities assessed the threat as credible and serious.
Is the Oracle EBS breach different from the OCI breach?
Yes, they are distinct incidents. The Oracle Cloud Infrastructure (OCI) breach targeted Oracle’s cloud authentication layer, exposing SSO tokens and tenant credentials. The Oracle E-Business Suite (EBS) breach was a separate campaign targeting Oracle’s enterprise application platform. It compromised operational business data at named organizations, including Cox Enterprises, LKQ Corporation, and the Washington Post.