You have probably heard the Word darknet thrown around in news headlines, crime documentaries, or tech conversations. Some people imagine it as a shadowy digital underworld full of hackers and criminals. Others think it is simply another name for the dark web. The truth is more nuanced and far more interesting.
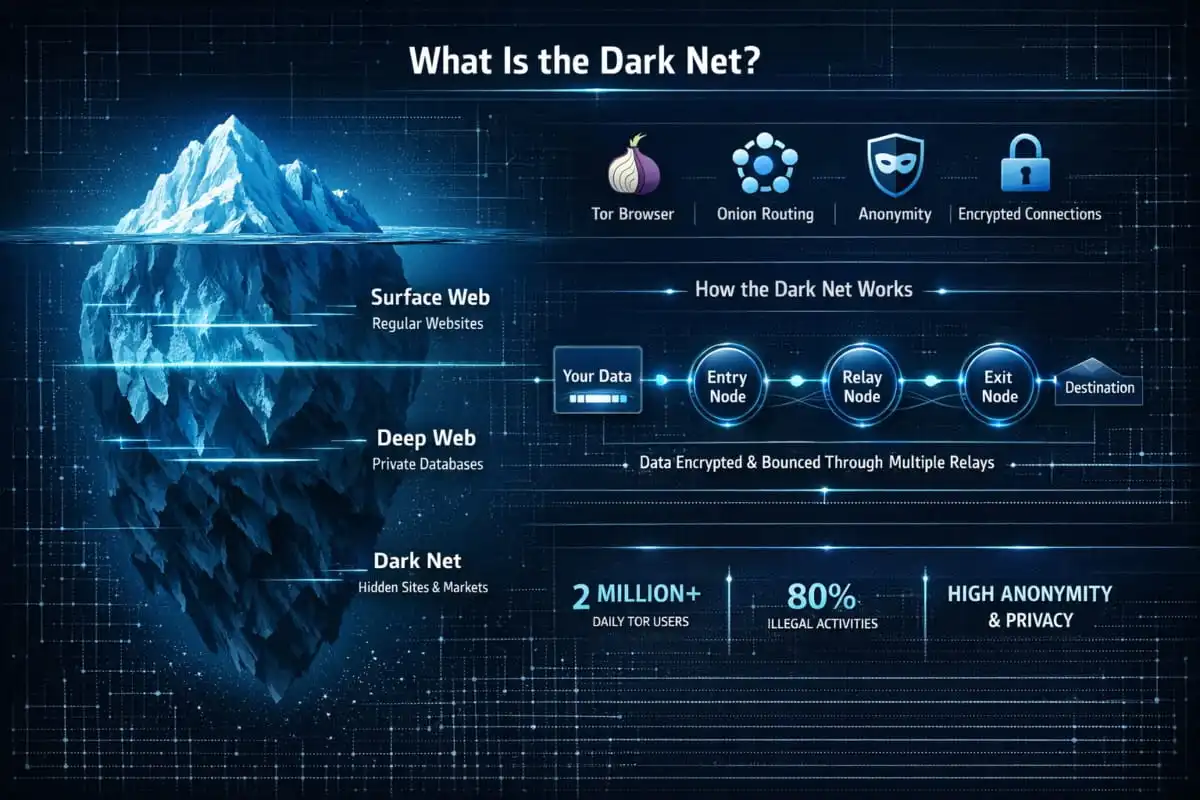
The darknet is a part of the internet that is not indexed by standard search engines like Google or Bing. You cannot reach it through a regular browser. It requires special software, specific configurations, and an understanding of how it works before you can access it. It exists in parallel to the internet you use every day, but it operates on an entirely different layer.
It was not built for crime. It was originally designed to enable private, anonymous communication and was used by military researchers, journalists, whistleblowers, and privacy advocates. Over time, it attracted a much wider range of users, both legitimate and otherwise.
In this guide, you will learn exactly what the darknet is, how it differs from the deep web and the dark web, how it works technically, what you will actually find on it, and whether accessing it is legal. Whether you are simply curious or you work in cybersecurity, this guide covers everything you need to know, clearly and without sensationalism.
What Is the Darknet?
The darknet is an encrypted, overlay network built on top of the existing internet infrastructure. Unlike the regular web, where websites are publicly listed, indexed by search engines, and accessible through any standard browser, darknet sites are intentionally hidden. They require specific software to access, the most common being the Tor browser, and they operate through anonymous routing systems that mask both the user’s identity and the server’s location.
In simple terms, the regular internet is a public space. The darknet is a private, hidden one.
It is important to understand that the darknet is not a separate physical network. It runs on the same cables and servers as the internet you use every day. What makes it different is the layer of encryption and anonymization sitting on top of it.
Who Created the Darknet?
Criminals did not invent the darknet. It was developed in the mid-1990s by researchers at the United States Naval Research Laboratory. Their goal was straightforward: to create a system that allowed intelligence agents and military personnel to communicate online without revealing their identities or locations.
The core technology behind it, called onion routing, was invented by mathematicians Paul Syverson, Michael Reed, and David Goldschlag. The idea was to wrap internet traffic in multiple layers of encryption, like the layers of an onion, so that no single point in the network could identify both who was sending a message and where it was going.
In 2002, this technology was released to the public as the Tor Project, a non-profit organisation that maintains it to this day. Making it open-source was a deliberate choice. A private anonymity network used only by the US government would actually be less secure; the more people using it, the harder it becomes to trace any individual user.

Darknet History Timeline
The darknet has evolved significantly since its origins in classified research labs.
In the 1990s, Onion routing was developed by the US Naval Research Laboratory as a tool for secure government communications.
In 2002, The Tor Project was publicly released, making anonymous browsing available to anyone worldwide.
2004–2010, Journalists, activists, and privacy advocates begin adopting Tor heavily, particularly in countries with strict internet censorship.
In 2011, Silk Road launched as the first major darknet marketplace, introducing the concept of anonymous online commerce using Bitcoin.
In 2013, the FBI shut down Silk Road and arrested its founder, Ross Ulbricht. The event brings worldwide media attention to the darknet for the first time.
From 2013 onwards, following the Snowden revelations about mass surveillance, mainstream interest in online privacy surged, and Tor usage climbed significantly.
In the 2020s, the darknet continued to evolve, with law enforcement agencies running increasingly sophisticated operations against illegal markets while legitimate privacy use remained strong.
Is the Darknet Real?
Yes, completely. The darknet is not a myth, an urban legend, or a Hollywood invention. It is a real, functioning network used by millions of people worldwide every single day.
What tends to be exaggerated, however, is its scale and content. Popular culture has painted it as an endless abyss of extreme illegal activity. The reality is that the majority of darknet traffic is driven by privacy-conscious individuals, people living under authoritarian governments, journalists protecting sources, and cybersecurity researchers, not the extreme criminal content that headlines tend to focus on.
The darknet exists. It is real. Understanding what it actually is, rather than what films and news stories make it out to be, is the first step toward forming an accurate picture of it.
Darknet vs Dark Web vs Deep Web: The Differences Explained
These three terms are used interchangeably in casual conversation, but they are not the same thing. Confusing them is one of the most common mistakes people make when trying to understand how the hidden internet works. Getting this distinction right matters, especially if you are researching this topic for cybersecurity, journalism, or simple curiosity.

Darknet vs Dark Web
This is where most of the confusion lives. The darknet and the dark web are closely related but not identical.
The darknet refers to the network itself, the underlying infrastructure of encrypted, anonymous connections. Think of it as the road system.
The dark web refers to the websites and content that exist on top of that network. Think of it as the buildings on those roads.
So technically, the dark web is a part of the darknet. You access dark websites by connecting through the darknet. When someone says they “visited the dark web,” what they actually did was connect to the darknet using software like Tor, then navigate to websites hosted on it.
In everyday usage, most people use both terms to mean the same thing, and that is fine for general conversation. But if you are working in cybersecurity or digital forensics, the distinction is worth keeping sharp.
Darknet vs Deep Web
The deep web is far larger than most people realise, and far less dramatic than the darknet.
The deep web is simply any part of the internet that is not indexed by search engines. That includes your email inbox, your online banking portal, company intranets, academic databases, private cloud storage, and subscription-based content. None of those pages appear in Google search results, which technically makes them part of the deep web.
By that definition, the deep web makes up an estimated 90 to 95 percent of the entire internet. Most of it is completely ordinary and legal.
The darknet is a small, specific subset of the deep web. What separates it from the rest of the deep web is intentional anonymization. Deep web content is simply unindexed. Darknet content is deliberately hidden and requires special software to access.
In short, all darknet content is deep web content, but most deep web content has nothing to do with the darknet.
Clearnet vs Darknet
The clearnet, sometimes called the surface web, is the internet most people use every day. Every website you can reach through Chrome, Safari, or Firefox without any special tools is part of the clearnet. It is indexed by search engines, publicly accessible, and your activity on it can be tracked by your internet service provider, the websites you visit, and various third parties.
The darknet is the opposite in almost every way. It is not indexed, not publicly accessible via standard browsers, and built around the principle of anonymity. Your traffic is encrypted and routed through multiple servers before reaching its destination, making it extremely difficult to trace back to you.
The practical difference comes down to privacy and visibility. On the clearnet, you are largely visible. On the darknet, you are largely anonymous, though not completely untraceable, as many arrested darknet users have discovered.
The Three Layers of the Internet
A simple way to picture the structure of the internet is to think of it in three layers stacked on top of each other.
The surface web (clearnet) sits at the top. This is everything publicly accessible and searchable: news sites, social media, online shops, and YouTube. It represents a small fraction of the total internet.
The deep web lies in the middle and accounts for the vast majority of internet content. Emails, private databases, banking portals, internal corporate systems, anything not indexed by a search engine. It is enormous, mostly legal, and mostly boring.
The darknet sits at the bottom. It is a small, intentionally hidden layer accessible only through tools like Tor or I2P. It contains both legitimate privacy-focused communities and, in certain corners, illegal activity.
Understanding these three layers makes every subsequent conversation about the darknet significantly clearer.
| Feature | Surface Web (Clearnet) | Deep Web | Darknet / Dark Web |
|---|---|---|---|
| Indexed by Google? | Yes | No | No |
| Access Method | Normal Browser (Chrome, Safari) | Normal Browser + Login/URL | Special Software (Tor, I2P) |
| Anonymous by Design? | No | No (Identifiable via logins) | Yes (Layered Encryption) |
| Estimated Size | Small (~4-10% of Internet) | Huge (~90% of Internet) | Tiny (Less than 0.01%) |
| Common Examples | YouTube, Wikipedia, Blogs | Online Banking, Email, Databases | .onion markets, whistleblowing sites |
| ISP Visibility | Full (Activity is tracked) | Full (Activity is tracked) | Hidden (Only “Tor usage” is visible) |
| Primary Risk | Phishing, Public Tracking | Data Breaches, Identity Theft | Malware, Law Enforcement Stings |
| Legality | Legal | Legal (Used daily by everyone) | Legal to browse (mostly); Illegal activities are crimes |
How Does the Darknet Work? Technology, Infrastructure, and Networks
Understanding how to access the darknet starts with understanding how it actually functions. The darknet does not run on a separate physical internet; it runs on the same infrastructure as the regular web. What makes it different is a sophisticated layer of encryption and anonymous routing sitting on top of that infrastructure. Before you think about how to get onto the darknet, it helps to understand the technology that makes it possible.

Tor Network Explained
Tor, short for The Onion Router, is the most widely used network for accessing the darknet. It is free, open-source, and maintained by a non-profit organisation. When you connect to Tor, your internet traffic does not travel directly from your device to the website you are visiting. Instead, it is bounced through a series of volunteer-operated servers called nodes or relays, spread across the world.
Each relay knows only the addresses of the relay immediately before it and the one immediately after it. No single server in the chain ever knows both who you are and where you are going at the same time. By the time your request reaches its destination, it has passed through at least three different relays in different countries.
This is what makes Tor so effective for anonymous browsing. It does not just hide your activity; it structurally prevents any single point in the network from having enough information to identify you.
Websites on the Tor network use .onion addresses instead of standard domain extensions like .com or .org. These addresses are only resolvable inside the Tor network, which is why you cannot visit them through a regular browser.
I2P and Freenet
Tor is not the only darknet network, though it is the most well-known. Two significant alternatives are I2P and Freenet, each built on slightly different principles.
I2P (Invisible Internet Project) is designed primarily for communication within its own network rather than anonymous access to the regular web. It uses a system called garlic routing, which bundles multiple encrypted messages together to make traffic analysis even harder than Tor’s approach. I2P is favoured by users who want a self-contained, highly private network for messaging, file sharing, and hosting services within its own ecosystem.
Freenet takes a different approach entirely. It is a decentralised, censorship-resistant platform where users contribute a portion of their hard drive storage to host content collectively. Files are broken into encrypted fragments and distributed across thousands of nodes. No single person hosts a complete file, which makes it extremely difficult for anyone, including law enforcement, to locate or remove content once it is published there.
Both I2P and Freenet are smaller and more technically demanding than Tor, but they serve important roles in the broader darknet infrastructure.
Onion Routing
Onion routing is the foundational technology behind Tor and the concept that enables anonymous internet communication. The name comes directly from how it works.
When you send a request through Tor, your data is wrapped in multiple layers of encryption, one for each relay node it passes through. As the data travels through the network, each relay decrypts one layer at a time, like peeling back an onion, revealing only the address of the next relay. The innermost layer is only decrypted by the final destination.
The result is that the entry node knows your IP address but not your destination. The middle relay knows neither. The exit node knows the destination but not your original IP address. No one in the chain holds the full picture.
This architecture was specifically designed so that even if one or two nodes in the chain are compromised or monitored, the anonymity of the overall communication is preserved. It is an elegant solution to a genuinely difficult technical problem.
Darknet Architecture
The darknet’s architecture sets it apart from using a VPN or a private browser. A VPN hides your traffic from your internet service provider and routes it through a single server, but that server knows exactly who you are and where you are going. You are simply shifting your trust from your ISP to your VPN provider.
The darknet, particularly through Tor, distributes that trust across multiple independent nodes so that no single party has complete information. Combined with end-to-end encryption, .onion hidden services, and the fact that darknet servers can also hide their own location, the architecture creates a genuinely two-way anonymity system that protects both the user and the server from identification.
This is why the darknet is used not just for browsing but for hosting. Journalists set up secure drop boxes on .onion addresses. Organisations publish censorship-resistant information. The architecture ensures that both sides of the connection remain private.
P2P Darknets
Beyond Tor, I2P, and Freenet, there is a broader category known as peer-to-peer darknets. These are decentralised networks where users connect directly to each other, often by invitation only, rather than through a centralised relay infrastructure.
Friend-to-friend networks are a well-known example. In these systems, you only connect to people you personally trust, creating a web of private, encrypted connections that is nearly impossible to map from the outside. Retroshare is one of the more established platforms built on this model.
P2P darknets tend to be smaller and slower than Tor, but they offer a different kind of security, one based on social trust rather than technical anonymity. They are particularly valuable in high-risk environments where even connecting to a known network like Tor could attract attention.
How to Access the Darknet Safely in 2026 (Step-by-Step Guide)
Accessing the darknet is not as technically complex as most people assume. The barrier is not skill; it is knowledge. The bigger challenge is doing it safely, because careless mistakes can expose your identity even on a network built for anonymity. This section walks you through every method, every platform, and the essential safety practices you need before you connect.
One important note before starting: accessing the darknet itself is legal in most countries. What you do once inside determines the legal boundary. Browsing privacy forums, reading uncensored news, or researching cybersecurity is entirely lawful. Engaging in illegal transactions is not. Keep that distinction clear.

Tor Browser Setup
The Tor Browser is the standard, most reliable way to access the darknet on a desktop or laptop. It is a modified version of Firefox, preconfigured to route all traffic through the Tor network automatically.
Step 1: Go to the official Tor Project website at torproject.org and download the Tor Browser for your operating system. Always download from the official source. Third-party downloads carry a real risk of containing malware.
Step 2: Install it as you would any other application. No special configuration is required for basic use.
Step 3: Open the browser and click Connect. Tor will establish a circuit through three relay nodes before your connection is live. This takes between 5 and 30 seconds, depending on your internet speed.
Step 4: Once connected, you can navigate to .onion addresses directly in the address bar. You can also use the regular web through Tor for added privacy, though browsing speed will be noticeably slower than usual.
Step 5: Never resize the Tor Browser window, do not install additional plugins or extensions, and never log in to personal accounts like Google or social media while using it. Each of these actions can create a unique fingerprint that undermines your anonymity.
How to Access on Android
Accessing the darknet on Android is straightforward thanks to the official Tor Project app.
Download the Tor Browser for Android directly from the Google Play Store or from the official Tor Project website as an APK file. Once installed, it functions almost identically to the desktop version. Tap Connect, wait for the circuit to establish, and you are browsing anonymously through the Tor network.
For users who want all their Android traffic routed through Tor, not just browser traffic, Orbot is the tool to use. Orbot is a proxy application from the Tor Project that tunnels your entire device’s internet connection through the Tor network. It can be used alongside other apps for system-wide anonymity.
Avoid using unofficial Tor apps found on third-party app stores. Several fake versions exist that claim to offer darknet access but are designed to harvest your data instead.
How to Access on iPhone
Accessing the darknet on an iPhone is possible, but it comes with more limitations than on Android due to Apple’s restrictions on how apps can handle network traffic.
The recommended option for iOS is Onion Browser, an open-source app endorsed by the Tor Project and available on the App Store. It routes your browsing through the Tor network and supports .onion addresses. It is not as fully featured as the desktop Tor Browser, and some .onion sites may not render perfectly, but it provides genuine Tor-based anonymity for mobile browsing.
A key limitation of the iPhone is that, unlike Android with Orbot, there is currently no reliable way to route all your device’s traffic through Tor on iOS. Onion Browser covers only in-browser activity. Keep that scope in mind when assessing your privacy needs.
Best VPNs for Darknet
Using a VPN alongside Tor adds an extra layer of privacy, though it is worth understanding exactly what that layer protects and what it does not.
When you connect to Tor without a VPN, your internet service provider can see that you are using Tor, even though they cannot see what you are doing on it. In most countries, this is not a problem. But in countries where Tor use is monitored or restricted, this visibility matters.
Adding a VPN before connecting to Tor, known as the VPN-over-Tor or Tor-over-VPN configuration, means your ISP sees only that you are connected to a VPN, not that you are using Tor. The VPN server sees your real IP but not your Tor traffic. Tor sees the VPN’s IP but not yours.
When choosing a VPN for darknet use, the most important criteria are a strict no-logs policy, jurisdiction outside of surveillance alliances, and a reliable kill switch. Mullvad, ProtonVPN, and IVPN are consistently regarded as the strongest options for privacy-focused users because they accept anonymous payment, keep no usage logs, and have been independently audited.
Avoid free VPNs entirely. Their business model almost always involves monetising your data, the opposite of what you need here.
OPSEC Basics
OPSEC (operational security) refers to the practices that protect your identity beyond just using Tor. Technical tools only go so far. Human behaviour is consistently the weakest point in any anonymity setup, and it is the reason most darknet users who have been identified were caught.
The most important OPSEC principles for darknet use are straightforward.
Never use your real name, personal email address, or any account linked to your real identity on the darknet. Create entirely separate identities for darknet activity and never cross-reference them with your normal online presence.
Do not brag or discuss your darknet activity on clearnet platforms. An extraordinary number of arrests have come from people discussing their darknet activities on Reddit, Twitter, or in Discord servers that were later monitored.
Be careful with files downloaded from the darknet. PDFs, images, and documents can contain tracking beacons or malware that phone home to a server with your real IP address the moment you open them outside of Tor. Always open downloaded files in an isolated environment, preferably while completely offline.
Disable JavaScript in the Tor Browser when visiting unknown .onion sites. JavaScript has been used in the past to de-anonymise Tor users by exploiting browser vulnerabilities.
Using Tails OS
Tails is a privacy-focused operating system designed to leave no trace of your activity on the computer you use it on. It is widely regarded as the gold standard for high-security darknet access and is the setup of choice for journalists, activists, and security researchers working in sensitive environments.
Tails runs entirely from a USB drive. You boot your computer from the USB, and Tails loads into your device’s RAM, never touching the hard drive. When you shut it down, every trace of your session is wiped automatically. Nothing is stored locally.
Tails comes with the Tor Browser pre-installed, along with a suite of privacy and encryption tools. Because it operates independently of your computer’s regular operating system, even if your main OS is compromised with malware, that malware cannot see or interfere with your Tails session.
Setting up Tails requires downloading the official image from tails.boum.org, verifying its cryptographic signature to confirm it has not been tampered with, and flashing it onto a USB drive of at least 8GB. The Tails website provides clear, step-by-step installation guides for Windows, Mac, and Linux.
For anyone who takes darknet privacy seriously or who accesses sensitive information in a high-risk professional context, Tails is not optional. It is the right foundation for everything else.
What Is on the Darknet? A Realistic Overview of Content and Services
The darknet has a reputation problem. Years of sensationalised news coverage and Hollywood dramatisation have created an image of an endless digital hellscape where every click leads to something horrifying or criminal. The reality is considerably more layered than that. Yes, illegal content and services exist on the darknet. But they represent one corner of a much broader ecosystem, and understanding the full picture is essential for anyone trying to form an accurate view of what the darknet actually is.

Legitimate Uses
The single most important thing to understand about darknet content is that a large portion of it serves entirely legitimate purposes. The anonymity that makes the darknet attractive to bad actors makes it equally valuable to people with genuinely good reasons to stay private.
People living under authoritarian governments use the darknet to access news, social media, and communication tools that are blocked or censored in their countries. Citizens of nations with heavy internet surveillance use it simply to speak freely. Privacy advocates and technologists use it to research and develop tools that protect civil liberties online.
Corporations and security teams use it for threat intelligence, monitoring darknet forums and marketplaces for leaked credentials, stolen data, or chatter about planned attacks against their organisations. Law enforcement agencies worldwide maintain a significant presence on the darknet for investigative purposes.
The darknet also hosts mirrors of mainstream websites specifically for users in censored regions. Facebook, for example, operates an official .onion address. The BBC and other news organisations publish darknet versions of their sites to reach audiences where their content is blocked.
Whistleblowing and Journalism
One of the most important and well-documented legitimate uses of the darknet is secure communication between journalists and their sources. SecureDrop, an open-source whistleblowing platform developed with support from the Freedom of the Press Foundation, runs exclusively as a .onion service. It is used by major news organisations including The New York Times, The Washington Post, The Guardian, and dozens of others.
The reason is simple. A whistleblower contacting a journalist via email, phone, or an encrypted messaging app leaves metadata that can eventually be traced. A SecureDrop submission through Tor leaves none. The source’s identity is structurally protected, not just promised.
This use case alone illustrates why the darknet exists and why it matters. Without it, many of the most significant investigative journalism stories of the past decade, stories that exposed genuine wrongdoing at the highest levels of government and industry, would never have made it to a reporter’s desk.
Forums and Communities
A significant portion of darknet traffic is simply people talking. The darknet hosts a wide range of forums and communities covering topics from cybersecurity research and privacy technology to politics, philosophy, and harm reduction.
Dread is the most prominent darknet forum, often described as the Reddit of the darknet. It hosts discussions on security, privacy, darknet market reviews, and general topics. It operates as a community hub where users share information, debate ideas, and ask questions in a safe environment free from surveillance.
Beyond Dread, there are forums dedicated to specific technical disciplines, political movements, and communities that feel marginalised or monitored on the clearnet. Some of these communities engage in legal activity that is simply sensitive, political dissent, discussions of drug harm reduction, or conversations about subjects that are taboo in certain countries but entirely legal in others.
Not all of it is admirable content. But the existence of these communities reflects a genuine human need for spaces where speech is not monitored or filtered.
Darknet Markets Overview
Darknet markets are online marketplaces that operate within the Tor network, typically facilitating the sale of goods, most commonly drugs, using cryptocurrency as payment. They function similarly to mainstream e-commerce platforms, complete with product listings, seller ratings, buyer reviews, and escrow systems to manage transactions.
The concept was introduced in 2011 with Silk Road, the first major darknet marketplace. Founded by Ross Ulbricht, Silk Road operated for two years and processed hundreds of millions of dollars in transactions before the FBI shut it down in 2013 and arrested Ulbricht. His arrest and subsequent life sentence sent a clear message, but it did not end darknet markets. It multiplied them.
AlphaBay emerged as the largest darknet market of its era before being taken down in 2017 in a coordinated international law enforcement operation. It was later relaunched by one of its original administrators. The cycle of markets rising, being shut down, and being replaced by new ones has continued ever since.
According to Chainalysis darknet market reports, these markets collectively process hundreds of millions of dollars in cryptocurrency transactions annually, even as authorities regularly dismantle individual platforms. The 2025 and 2026 reports show that while major takedowns temporarily reduce activity, the overall market ecosystem has proven remarkably resilient.
Darknet markets in 2026 continue to operate, though the landscape shifts constantly. Active markets come and go, and the question of which markets are currently operational changes week to week. What has remained consistent is the ecosystem itself; demand drives supply, and supply finds a way to operate.
It is also worth understanding exit scams, one of the most common risks in darknet market activity. An exit scam occurs when a market’s administrators, who hold funds in escrow on behalf of buyers and sellers, simply disappear with all the cryptocurrency in the system. Several of the biggest darknet markets have ended this way rather than through law enforcement action, leaving users with no recourse.
Horror Stories and Myths
No discussion of darknet content is complete without addressing the myths, because they are persistent, widely believed, and almost entirely false.
The most enduring myth is the red room, a live-streamed torture or murder broadcast that viewers pay to watch in cryptocurrency. Despite decades of claims, no verified evidence of a functioning red room has ever been produced. The concept is almost certainly an internet urban legend that has been recycled and embellished over time.
Hitman services are another common darknet myth. Numerous sites claiming to offer contract-killing services are scams: they accept Bitcoin payments but deliver nothing because the service does not actually exist. Several documented cases show that people who attempted to use these services were either scammed or, in some cases, identified and arrested for attempted murder.
The idea that the darknet contains an infinite catalogue of extreme illegal content in every imaginable category is also significantly overstated. Illegal content exists, which is not in dispute. But the darknet is not the bottomless pit of horror that popular media portrays. Much of what circulates online as darknet “screenshots” or stories is fabricated, exaggerated, or wildly taken out of context.
Understanding the darknet accurately means resisting both the urge to dismiss it as entirely harmless and the urge to mythologise it as uniquely monstrous. It is a technology, one that reflects the full range of human behaviour, both constructive and destructive.
Is the Darknet Illegal? Laws, Risks, and What Can Get You Arrested
This is one of the most searched questions about the darknet, and the answer is not as simple as yes or no. The legality of the darknet depends entirely on where you are in the world and, more importantly, what you are doing on it. Conflating the network itself with the illegal activity that sometimes occurs on it is a mistake that leads to unnecessary fear and genuine misunderstanding.

Is Accessing the Darknet Illegal?
In most countries, accessing the darknet is completely legal. Downloading the Tor Browser, connecting to the Tor network, and browsing .onion websites are no different, legally, from using a VPN or a private browser. The act of connection carries no criminal liability on its own.
The United States, the United Kingdom, most of Europe, Canada, and Australia all permit access to the darknet without restriction. Journalists, security researchers, academics, and privacy advocates use it openly and professionally every day.
There are exceptions. In countries like China, Russia, Iran, and North Korea, Tor usage is either heavily restricted or outright banned as part of broader internet censorship regimes. In those jurisdictions, simply connecting to the Tor network can attract government attention, regardless of what you do once connected.
For the vast majority of users in democratic countries, the answer is clear: accessing the darknet is not illegal. What you do there is what determines your legal exposure.
What Activities Are Illegal
The darknet does not create a legal exception for criminal behaviour. Every law that applies in the physical world and on the regular internet applies equally to activity conducted on the darknet. Anonymity is a technical feature of the network; it is not a legal shield.
The activities that carry serious criminal liability on the darknet fall into well-defined categories.
Purchasing or selling controlled substances through darknet markets is a criminal offence in virtually every jurisdiction, regardless of whether the transaction is conducted anonymously. Buying, selling, or possessing child sexual abuse material carries severe criminal penalties and is subject to active international law enforcement cooperation. Commissioning or facilitating violence, even through services that turn out to be scams, can constitute attempted murder or conspiracy charges. Trafficking in stolen financial data, hacked credentials, counterfeit documents, or illegally obtained personal information constitutes fraud and identity theft. Conducting or facilitating cyberattacks, deploying ransomware, or selling hacking tools and exploit kits carries significant criminal exposure under computer fraud laws in most countries.
The common thread across all of these is simple: the crime is the activity, not the network. Using Tor does not make illegal things legal. It makes them harder to trace, but as years of successful prosecutions have demonstrated, not impossible.
Darknet Arrests and Major Busts
The history of law enforcement on the darknet is a consistent reminder that anonymity there is powerful but not absolute. Some of the most significant criminal prosecutions of the past decade have involved darknet activity.
Ross Ulbricht, the founder of Silk Road, was arrested in 2013 in a San Francisco public library. Despite operating one of the most sophisticated anonymous marketplaces ever built, he was identified through a combination of early operational security mistakes, including using his real email address in early forum posts, and traditional investigative work. He was sentenced to life in prison without the possibility of parole.
AlphaBay’s administrator, Alexandre Cazes, was arrested in Thailand in 2017 following a joint operation between the FBI, DEA, and Europol. His arrest came not from a Tor vulnerability. Still, due to a configuration error, his server’s welcome email was accidentally sent from his personal ProtonMail address, which was registered under his real name.
Welcome to Video, a darknet platform hosting child sexual abuse material, which was dismantled in 2018 through blockchain analysis. Investigators traced Bitcoin transactions to real-world identities, resulting in arrests in 38 countries. The case demonstrated that cryptocurrency is far less anonymous than many darknet users assume.
These cases share a consistent pattern. In almost every major darknet arrest, the technical anonymity of Tor remained intact. What failed was human behaviour, poor operational security, careless mistakes, and the assumption that anonymous online activity could never be linked back to a physical identity.
FBI and Law Enforcement Operations
Law enforcement engagement with the darknet has grown substantially more sophisticated over the past decade. Early operations relied heavily on informants and traditional investigative methods. Modern operations combine those approaches with advanced blockchain analytics, undercover infiltration, international cooperation, and increasingly, the use of legal processes to compel information from infrastructure providers.
The FBI, Europol, the DEA, and equivalent agencies in dozens of countries now have dedicated units focused exclusively on darknet investigations. Operations like Operation Onymous in 2014, which took down over 400 darknet services simultaneously, and Operation DisrupTor in 2020, which resulted in 179 arrests across six countries, illustrate the scale and coordination that modern darknet enforcement operations can achieve.
Importantly, law enforcement agencies do not always shut down darknet infrastructure immediately upon gaining access to it. In several documented cases, agencies have quietly taken control of darknet markets or servers and continued operating them for weeks or months, harvesting user data, mapping vendor networks, and building cases before making arrests. Users who believed they were transacting on a legitimate darknet market were, in some instances, transacting directly with federal agents.
The takeaway is not that the darknet is a trap. It is that law enforcement has developed genuinely effective methods for darknet investigation, and the assumption that anonymity guarantees safety has cost many people their freedom.
Legal Darknet Uses
It is worth stating clearly and finally: the darknet has substantial, well-documented, legitimate uses, and using it for those purposes carries no legal risk whatsoever in most countries.
Journalists and their sources use it to communicate securely through platforms like SecureDrop. Activists and political dissidents in authoritarian countries use it to organise, communicate, and access uncensored information. Cybersecurity professionals use it to conduct threat research, monitor for leaked organisational data, and study attack methodologies in a controlled way. Privacy-conscious individuals use it simply because they prefer not to be tracked, profiled, or monitored by corporations or governments.
Academic researchers study darknet ecosystems to understand cybercrime, drug markets, and underground economies. The data produced by that research informs policy, law enforcement strategy, and public health initiatives around the world.
The darknet is a tool. Like any tool, its legal and ethical character is determined entirely by how it is used. Understanding that distinction is the foundation of any honest conversation about it.
Darknet Monitoring and Cybersecurity: Protecting Your Organization
For most individuals, the darknet is something to understand, if not avoid. For cybersecurity professionals, it is something to watch closely and continuously. The darknet is where stolen data gets sold, where cyberattack infrastructure gets built, and where early warning signs of threats against organisations first appear. Knowing how to monitor it effectively has become a core competency for modern security teams.

What Is Darknet Monitoring?
Darknet monitoring is the practice of systematically scanning darknet forums, marketplaces, paste sites, and hidden services to identify information or activity that poses a risk to an organisation or individual. It is a form of proactive cybersecurity, finding threats before they materialise rather than responding after damage has been done.
At its most basic level, darknet monitoring involves checking whether your organisation’s data has appeared where it shouldn’t. Leaked employee credentials, stolen customer records, exposed internal documents, and compromised payment card data all routinely surface on darknet marketplaces and forums shortly after a breach, often before the affected organisation even knows the breach occurred.
At a more advanced level, darknet monitoring extends to tracking threat actor behaviour, monitoring chatter about planned attacks, identifying new malware or exploit kits being sold or distributed, and mapping the infrastructure of cybercriminal networks operating against specific industries or targets.
The value of darknet monitoring is fundamentally about timing. A breach detected through darknet exposure monitoring within hours of data appearing for sale allows an organisation to respond, reset credentials, notify affected parties, and close vulnerabilities before the leaked data is widely used. A breach discovered weeks or months later, after credentials have been sold and exploited repeatedly, is dramatically more damaging.
Best Darknet Monitoring Tools
The darknet monitoring tool market has grown significantly as enterprise demand for threat intelligence has increased. Tools range from fully automated platforms that continuously scan and alert to more research-oriented services that provide curated intelligence reports.
DeXpose
When it comes to darknet monitoring, DeXpose stands out as one of the most capable and practically accessible platforms available today. Built by a team with an average of 10 years of hands-on offensive security experience, it was designed by people who understand how cybercriminals actually operate, not just how to observe them from a distance.
At its core, DeXpose is a unified digital risk protection platform. It gives enterprises and government organisations real-time visibility into how their data, credentials, and brand are being exposed and exploited across dark web markets, malware logs, data breaches, and deep web sources, all from a single dashboard.
What makes DeXpose particularly practical is where it starts: with a free exposure report. Any organisation can enter their domain and receive an immediate breakdown of their darknet exposure, covering dark web market mentions, compromised credentials from malware logs, and known breach appearances, before committing to anything. It is one of the few enterprise-grade darknet monitoring tools that makes the first step genuinely frictionless.
Beyond the free report, DeXpose offers five core capabilities that cover the full spectrum of organisational darknet risk.
Dark web monitoring provides 24/7 continuous visibility into your organisation’s exposure across dark web sources, tracking compromised accounts, leaked credentials, and mentions of your assets in criminal communities before that information is weaponised against you.
For organisations that want enterprise-grade darknet intelligence without the complexity and cost of the largest players in the market, DeXpose offers a compelling combination of technical depth, practical accessibility, and a genuinely useful free starting point at dexpose.io.
Recorded Future is one of the most established darknet intelligence platforms, aggregating data from across the darknet, deep web, and open web to produce structured threat intelligence. Enterprise security teams and government agencies widely use it.
Flare specialises in exposure monitoring, automatically detecting when an organisation’s data, credentials, or mentions appear across darknet forums and markets. It is designed to reduce the manual effort required to maintain darknet visibility.
DarkOwl operates one of the largest commercially available darknet data archives, providing access to indexed darknet content for investigators, security researchers, and intelligence teams through an API and analyst platform.
Kela focuses specifically on cybercriminal intelligence, monitoring the communities and marketplaces where threat actors coordinate, trade tools, and discuss targets. It is particularly strong for understanding the human networks behind cyber threats rather than just the data they produce.
SpyCloud focuses on recaptured breach data, credentials, and personal information recovered from criminal sources and delivers it in a format that enables organisations to take immediate remediation action.
Choosing the right tool depends on the organisation’s size, threat profile, and internal security capability. Smaller organisations may find managed darknet monitoring services more practical than enterprise platforms built for dedicated analyst teams.
Darknet Threat Intelligence
Darknet threat intelligence goes beyond simply checking whether your data has leaked. It involves understanding the threat landscape your organisation operates in, who is targeting your industry, what tools and techniques are being discussed or sold, and where the next wave of attacks is likely to come from.
Threat intelligence analysts working the darknet monitor a specific set of environments. Criminal forums like Exploit and XSS, Russian-language platforms where sophisticated threat actors trade tools, services, and stolen data, provide early visibility into emerging attack techniques. Darknet marketplaces reveal what types of access and data are being commoditised. Telegram channels, which sit at the intersection of the clearnet and darknet ecosystems, have become increasingly important as coordination hubs for cybercriminal groups.
The output of this intelligence work feeds directly into defensive security operations. When an analyst identifies that initial access brokers are selling VPN credentials for companies in a specific sector, that information can trigger immediate credential audits and multi-factor authentication enforcement across affected organisations, before a single attack has been launched.
Darknet threat intelligence is also essential for understanding ransomware groups. Most major ransomware operators maintain darknet sites where they publish victims’ names, post stolen data as leverage, and negotiate publicly. Monitoring these sites gives security teams and incident responders real-time visibility into active ransomware campaigns.
Brand Protection on the Darknet
Brand protection on the darknet is a specific and increasingly important discipline for organisations whose reputation, intellectual property, or customer trust can be damaged by darknet activity.
The most common brand-related darknet threats include the sale of counterfeit products using a brand’s identity, the distribution of phishing kits designed to impersonate a brand’s login pages, the sale of compromised customer accounts from a brand’s platform, and the leaking or sale of proprietary business documents, source code, or trade secrets.
Darknet brand protection monitoring involves continuously scanning for mentions of an organisation’s name, domain, product names, and executive identities across darknet forums and markets. When a threat is identified, a phishing kit is being sold, counterfeit goods are being advertised, or customer data is being auctioned, the organisation can take action to mitigate damage, notify affected customers, and in some cases, work with law enforcement to pursue the responsible parties.
For financial institutions, healthcare organisations, and large consumer brands, darknet brand protection monitoring is no longer optional. The volume and speed at which brand-related threats emerge and circulate on the darknet make manual monitoring impractical; automated darknet scanning with human analyst oversight is the standard approach for organisations taking this seriously.
OSINT and Darknet Investigation
Open-source intelligence, OSINT, and darknet investigation are closely related disciplines that overlap significantly in professional practice. OSINT refers to the collection and analysis of information from publicly available sources. Darknet investigation extends that practice into the hidden corners of the internet that require specialised access and tools.
For cybersecurity investigators, journalists, and law enforcement analysts, combining OSINT techniques with darknet research yields a more complete picture of threat actors, criminal networks, and illicit operations than either approach alone.
A typical darknet investigation might begin with a leaked credential appearing on a paste site, a clearnet OSINT source. Tracing that credential leads to a darknet forum where it was first sold. Analysing the seller’s posting history on that forum reveals patterns, other products sold, communication styles, and operational details that can be cross-referenced with clearnet OSINT sources to build a profile of the actor behind the account.
Tools commonly used in darknet OSINT investigations include Maltego for relationship mapping, blockchain analytics platforms such as Chainalysis and TRM Labs for tracing cryptocurrency flows, and specialised darknet search and indexing services that enable investigators to query archived darknet content without manually visiting every relevant site.
The discipline requires patience, technical knowledge, and a clear understanding of legal boundaries, particularly around evidence handling if the investigation is intended to support legal proceedings.
Darknet Data Feeds
For organisations that want to integrate darknet intelligence directly into their security operations infrastructure, darknet data feeds provide a structured, continuous stream of threat data that SIEM platforms, threat intelligence tools, and automated alerting systems can ingest.
Darknet data feeds typically deliver information in standardised formats, JSON, STIX/TAXII, or CSV, covering categories like newly discovered leaked credentials, fresh paste site content, newly listed stolen data on darknet markets, newly registered .onion domains, and indicators of compromise associated with known threat actors.
The advantage of data feeds over platform-based monitoring tools is automation and integration. Rather than logging into a separate portal to check for alerts, security teams receive darknet intelligence directly inside the tools they already use, correlating darknet signals with internal telemetry to identify threats that affect their specific environment.
Providers such as DarkOwl, Flashpoint, and Recorded Future offer API-based darknet data feeds at the enterprise level. For organisations with mature security operations centres, integrating darknet data feeds into the broader threat intelligence pipeline represents a meaningful upgrade to their early warning capability, turning the darknet from an unknown blind spot into a monitored and manageable part of the threat landscape.
Darknet Markets, What They Are, How They Work, and Their History
Darknet markets are among the most discussed and least understood aspects of the darknet. They are simultaneously a subject of serious academic research, ongoing law enforcement focus, and endless media fascination. Understanding what they actually are, how they function, and how they have evolved gives a far more accurate picture than the sensationalised version that typically circulates in news coverage and documentaries.

Silk Road, The First Darknet Market
To understand darknet markets, you have to start with Silk Road, because everything that came after it was built in its image.
Silk Road launched in February 2011 and was created by Ross Ulbricht, who operated under the pseudonym Dread Pirate Roberts. It was a straightforward concept: an anonymous online marketplace hosted on the Tor network, using Bitcoin as its currency, where sellers could list products and buyers could purchase them without either party revealing their real identity. The primary inventory was drugs, cannabis, MDMA, cocaine, and prescription medications, though the platform also hosted other goods and services.
What made Silk Road genuinely remarkable was not just its anonymity but its community standards. Ulbricht enforced strict rules against the sale of weapons, child abuse material, and anything designed to harm a third party. The market had a functioning review system, dispute-resolution processes, and a seller-rating infrastructure that closely mirrored those of legitimate e-commerce platforms. At its peak, it was processing millions of dollars in transactions monthly.
The FBI shut down Silk Road in October 2013 and arrested Ulbricht at a San Francisco public library, not through a Tor vulnerability but through old-fashioned investigative work that traced his early forum posts to a personal email address. He was convicted in 2015 and sentenced to life in prison without the possibility of parole, a sentence that remains deeply controversial in privacy and drug policy circles.
Silk Road’s closure did not end darknet markets. It proved their commercial viability and triggered an explosion of successor platforms. Within weeks of its shutdown, Silk Road 2.0 had launched. The template Ulbricht created has been replicated, refined, and rebuilt dozens of times in the decade since.
How Darknet Markets Work
The operational structure of a darknet market is more sophisticated than most people assume, mirroring mainstream e-commerce in many of its fundamental mechanics.
A darknet market operates as a .onion website accessible only through the Tor network. Vendors apply to sell on the platform, typically paying a bond or deposit to establish credibility and deter scammers. Buyers browse listings, read reviews, and place orders, a process that feels familiar to anyone who has used eBay or Amazon, with the obvious difference that the products are frequently illegal.
Payments are made exclusively in cryptocurrency, historically Bitcoin. However, privacy-focused coins like Monero have become increasingly common as buyers and sellers seek transaction anonymity that Bitcoin alone does not fully provide. When a buyer places an order, funds are typically held in escrow by the market rather than sent directly to the vendor, protecting the buyer against vendors who take payment and disappear.
Communication between buyers and vendors happens through the platform’s internal messaging system, often encrypted with PGP keys to ensure that even if the market is compromised, individual message content cannot be read. Vendors provide shipping instructions, tracking information, and stealth packaging details through these encrypted channels.
The review system is central to how trust functions on darknet markets. In an environment where neither party can take legal recourse if a transaction goes wrong, reputation is everything. Vendors build their standing through consistent, accurate product descriptions, reliable shipping, and responsive communication. Buyers read these reviews the same way they would check seller feedback before purchasing on any mainstream platform.
Are Darknet Markets Still Active in 2026?
Yes, darknet markets remain active in 2026, though the landscape looks different from earlier years. Law enforcement pressure has become more sophisticated and more international in its coordination, and no single market has achieved the dominance that platforms like AlphaBay or Hydra once held. The ecosystem has instead become more fragmented, with multiple mid-sized markets operating simultaneously rather than one dominant platform.
The pattern that has defined darknet markets since Silk Road’s closure is one of continuous disruption and renewal. A major market is taken down by law enforcement or collapses through an exit scam. Its user base, vendors, and buyers alike, migrate to established alternatives or newly launched platforms. The cycle repeats. Each iteration tends to incorporate lessons from previous market failures, introducing new security features, decentralised structures, and more sophisticated operational security.
What has changed most significantly in recent years is the increasing shift toward direct vendor shops, individual vendors operating their own .onion storefronts rather than listing through centralised markets. This decentralisation reduces the single point of failure that has made large markets attractive targets for both law enforcement and exit-scamming administrators.
The short answer for anyone researching current darknet market activity: the ecosystem is alive, active, and continuously evolving. Specific platforms come and go, but the underlying infrastructure and demand that sustains them have proven consistently resilient.
Escrow, PGP, and Crypto Payments
Three technical mechanisms underpin how trust and security function within darknet markets, and understanding them explains a great deal about how these platforms have managed to operate at scale despite operating entirely outside legal frameworks.
Escrow is a system that protects buyers from vendors who take payment but fail to deliver goods. When a buyer places an order, their cryptocurrency payment is held by the market in a neutral account until the buyer confirms receipt of their order. Only then are funds released to the vendor. This mirrors the escrow systems used in legitimate real estate and high-value commerce transactions. Some markets offer a finalise early option, allowing buyers to release funds before confirming delivery, but experienced users treat this with caution, as it removes the buyer’s primary protection.
PGP (Pretty Good Privacy) is an encryption standard used to secure communications among buyers, vendors, and market administrators. Each party generates a PGP key pair: a public key they share openly and a private key they keep secret. Messages encrypted with someone’s public key can only be decrypted by their private key. On darknet markets, PGP encryption ensures that order details, shipping addresses, and sensitive communications cannot be read even if the market’s servers are seized by law enforcement. Vendors who do not support PGP are generally viewed with suspicion by experienced buyers.
Cryptocurrency payments provide the financial anonymity that enables darknet commerce. Bitcoin was the original standard, but its transaction history is publicly visible on the blockchain, allowing flows to be traced with sufficient analysis. Monero has emerged as the preferred currency for privacy-focused darknet transactions because its blockchain obscures sender, recipient, and transaction amounts by default, making tracing significantly harder.
Exit Scams Explained
Exit scams are one of the defining risks of darknet market participation and one of the most instructive examples of how trust functions, and fails, in anonymous commercial environments.
An exit scam occurs when a market’s administrators, who hold cryptocurrency in escrow to support thousands of ongoing transactions, abruptly disappear and take all that money with them. Because darknet markets operate anonymously and outside any legal framework, there is no recourse for the vendors and buyers who lose funds. The administrators are simply gone.
Exit scams have led to the closure of several major darknet markets. Evolution, one of the largest markets of its era, exit-scammed in 2015, taking an estimated $12 million in Bitcoin from its users. Dream Market, which operated for several years as one of the most trusted platforms in the ecosystem, closed in 2019 amid circumstances many users believed constituted at least a partial exit scam.
The warning signs of an impending exit scam have become well understood within darknet communities. Extended withdrawal delays, where vendors find themselves unable to withdraw their earnings, are typically the first indicator. This is followed by increasingly implausible technical explanations from administrators, growing complaints on forums like Dread, and eventually silence. By the time most users recognise what is happening, the funds are already gone.
The response from the market ecosystem has been a gradual shift toward shorter escrow periods, multi-signature cryptocurrency transactions that require both vendor and buyer agreement to release funds, and decentralised market architectures that remove the administrator’s ability to access escrow funds entirely.
Chainalysis Annual Reports
Chainalysis, a blockchain analytics firm that works with law enforcement, financial institutions, and government agencies, publishes annual reports on cryptocurrency crime that include some of the most rigorously sourced data available on darknet market activity. For researchers, journalists, security professionals, and policymakers, these reports have become essential reading.
The Chainalysis darknet market reports track transaction volumes flowing through darknet markets year over year, map user migration between markets following shutdowns, analyse cryptocurrency flows associated with major law enforcement operations, and identify emerging trends in how darknet markets structure their financial operations.
Key findings from recent Chainalysis reports illustrate the scale and resilience of the darknet market ecosystem. Despite multiple high-profile takedowns, total darknet market revenue has remained substantial, measured in hundreds of millions of dollars annually. The reports have also documented the growing adoption of Monero and other privacy coins, the increasing sophistication of money laundering techniques used to convert darknet proceeds into usable currency, and the rising importance of cryptocurrency exchanges in the overall flow of darknet funds.
For anyone conducting serious research into darknet markets, whether for academic, journalistic, or professional purposes, the Chainalysis annual crypto crime report provides the most reliable publicly available statistical picture of how this ecosystem operates and evolves.
Darknet, Cryptocurrency, and Financial Crime
The relationship between the darknet and cryptocurrency is not accidental. It is structural. The anonymity that makes the darknet attractive as a network is only useful for commerce if the payment system matches it. Traditional financial systems, bank transfers, credit cards, and PayPal leave clear identity trails that completely undermine any anonymity the Tor network provides. Cryptocurrency filled that gap, and the two technologies have been deeply intertwined ever since.
Understanding how darknet financial flows work matters beyond the darknet itself. It sits at the centre of modern financial crime, regulatory policy, and the ongoing debate about how much privacy cryptocurrency users should have.

Why Darknet Uses Crypto
The core requirement for darknet commerce is a payment method that does not require either party to reveal their real identity and cannot be reversed or frozen by a third party. No traditional financial instrument meets both criteria simultaneously.
Credit cards require identity verification and can be charged back or traced through the issuing bank. Wire transfers are logged by financial institutions and subject to anti-money laundering reporting requirements. Even cash, the most anonymous traditional payment method, becomes impractical for online transactions and international commerce.
Cryptocurrency solves both problems at once. A cryptocurrency wallet can be created without identity verification. Transactions are processed by a decentralised network rather than a bank or payment processor, meaning no single institution can freeze funds or reverse a transaction. And while the transaction history is recorded on a public blockchain, the wallet addresses involved are strings of characters rather than names, providing a layer of pseudonymity that, combined with the Tor network, creates a reasonably effective system for financial privacy.
Bitcoin was the natural first choice when Silk Road launched in 2011, simply because it was the only viable cryptocurrency at the time. Its adoption on darknet markets drove significant early awareness of Bitcoin in the broader public, one of the more ironic footnotes in cryptocurrency history.
Bitcoin Mixers and Tumblers
Bitcoin’s pseudonymity has a fundamental limitation that darknet users quickly discovered: the blockchain is entirely public. Every transaction ever made in Bitcoin is permanently recorded and publicly visible. While wallet addresses are not inherently linked to real identities, the transparent transaction graph means that with enough analysis, Bitcoin flows can be traced, and real identities can sometimes be inferred at points where cryptocurrency intersects with the real world, such as exchange deposits and withdrawals.
Bitcoin mixers, also called tumblers, were developed specifically to address this problem. A mixer works by pooling Bitcoin from multiple users, breaking the transaction chain, and returning equivalent amounts to each user from a different set of inputs. The goal is to sever the traceable link between the source of funds and their destination.
The process typically works as follows: a user sends Bitcoin to the mixer service along with a destination address. The mixer combines those funds with Bitcoin from other users in the pool, applies randomised delay times and variable transaction amounts to obscure patterns, and sends back equivalent funds from a different wallet, ensuring that the output cannot be directly linked to the input on the blockchain.
Mixing services have faced increasing legal scrutiny. In 2022, the US Treasury Department sanctioned Tornado Cash, a cryptocurrency mixer operating on the Ethereum network, marking the first time a piece of open-source software was sanctioned. Several Bitcoin mixer operators have faced criminal prosecution for facilitating money laundering. The legal environment around mixing services has become significantly more hostile as regulators and law enforcement have developed a clearer framework for treating mixing as an enabler of financial crime.
Money Laundering on the Darknet
Money laundering, the process of making criminally obtained funds appear to have a legitimate origin, is a central challenge for anyone profiting from darknet criminal activity. Cryptocurrency earned through darknet drug sales, fraud, or cybercrime is recorded on a blockchain, where its criminal origin can potentially be traced. Converting it into spendable real-world currency without triggering financial crime detection is the problem that darknet money laundering attempts to solve.
The layering process typically involves multiple steps. Funds earned on darknet markets are first moved through mixing services or exchanged for privacy coins like Monero to break the transaction trail. They are then moved through a series of intermediate wallets, sometimes dozens, to obscure the origin further. Eventually, the funds reach a cryptocurrency exchange where they can be converted into fiat currency, ideally through exchanges operating in jurisdictions with less rigorous know-your-customer requirements or through peer-to-peer trading platforms.
The scale of darknet money laundering is substantial. Chainalysis data consistently shows that a significant portion of cryptocurrency flowing out of darknet markets moves through exchanges, including, in some cases, major regulated exchanges where automated compliance systems failed to flag the funds as high risk.
How do cybercriminals use darknet markets in the broader financial crime ecosystem? Beyond direct drug sales, darknet markets facilitate the sale of stolen financial credentials, compromised bank account access, and money mule recruitment, creating interconnected financial crime networks where the darknet serves as both a marketplace and a coordination infrastructure for laundering operations that extend well into the legitimate financial system.
Blockchain Analytics (Chainalysis, TRM Labs)
The development of blockchain analytics as a discipline has fundamentally changed the risk calculation for darknet financial activity. What was once assumed to be essentially untraceable has proven, in case after case, to be significantly more transparent than its users believed.
Blockchain analytics firms work by mapping the flow of cryptocurrency transactions across public blockchains. These clustering wallet addresses appear to be controlled by the same entity, and identifying points where anonymous cryptocurrency intersects with known entities, exchanges, services, and previously identified criminal wallets. Over time, these firms have built extraordinarily detailed maps of how cryptocurrency moves through the global financial system, including through darknet markets.
Chainalysis is the dominant player in the space, working extensively with law enforcement agencies, including the FBI, DEA, IRS Criminal Investigation, and Europol. Its tools have been used as evidence in major darknet prosecutions, and its annual crypto crime reports set the standard for public data on illicit cryptocurrency flows. The firm’s reactor tool allows investigators to trace cryptocurrency transactions across complex multi-hop laundering chains visually.
TRM Labs operates in the same space, with a strong focus on financial institution compliance and law enforcement support. Its blockchain intelligence platform covers a broader range of blockchains than many competitors, reflecting the diversification of cryptocurrency use across the darknet ecosystem beyond Bitcoin.
Elliptic provides similar capabilities with particular strength in exchange compliance, helping regulated cryptocurrency businesses identify and reject deposits originating from darknet markets or other high-risk sources.
The implications of darknet financial crime are significant and well-documented. The Welcome to Video case, in which darknet child abuse material distribution was disrupted through Bitcoin transaction tracing, and the Colonial Pipeline ransomware recovery, in which the FBI recovered the majority of a Bitcoin ransom payment through blockchain analysis, demonstrated that cryptocurrency’s apparent anonymity is far more conditional than the darknet community once assumed.
The arms race between privacy-enhancing technologies and blockchain analytics continues. The adoption of Monero, zero-knowledge proofs, and cross-chain bridges reflects the darknet community’s ongoing efforts to stay ahead of forensic tracing capabilities. Whether those techniques remain effective against the next generation of analytics tools is a question that will define the Future of darknet financial crime and the policies designed to combat it.
Final Thoughts
The darknet is one of the most misunderstood corners of the internet. It is not the endless criminal underworld that headlines suggest, nor is it an innocent privacy tool free from serious risks. The truth sits firmly in between.
It was built for anonymity, adopted for both noble and destructive purposes, and it continues to evolve in response to technology, law enforcement, and human behaviour. Journalists rely on it to protect sources. Activists use it to speak freely. Criminals exploit it for profit. Security professionals monitor it to defend organisations.
What matters most is understanding it accurately, because accurate understanding leads to informed decisions, whether you are a curious individual, a cybersecurity professional, or a policymaker shaping the rules around digital privacy.
The darknet exists. It is real, complex, and here to stay. Now you know what it actually is.
Frequently Asked Questions (FAQ’s)
Can you access the darknet on a phone?
Yes. On Android, the official Tor Browser and the Orbot app both provide reliable access to the darknet. On iPhone, Onion Browser, endorsed by the Tor Project, is the recommended option.
Is Tor the same as the darknet?
Not exactly. Tor is the software and network used to access the darknet. Think of Tor as the road and the darknet as the destination; one enables access to the other, but they are not the same thing.
Is the darknet the same as the dark web?
They are closely related but technically different. The darknet is the underlying anonymous network infrastructure. The dark web refers to websites and content hosted on it. In everyday conversation, the terms are used interchangeably, but the distinction matters in technical and security contexts.
Who created the darknet?
The core technology behind the darknet, onion routing, was developed in the mid-1990s by researchers at the United States Naval Research Laboratory. It was released to the public as the Tor Project in 2002 and has been maintained as an open-source non-profit ever since.
What is Dread on the darknet?
Dread is the darknet’s most prominent discussion forum, often described as the Reddit of the darknet. It hosts communities focused on darknet market reviews, cybersecurity, privacy, and general discussion in an environment designed for anonymous, uncensored conversation.
Are darknet markets still active in 2026?
Yes. Darknet markets remain active in 2026, though the landscape is more fragmented than in previous years. No single platform dominates the way Silk Road or AlphaBay once did, but multiple markets continue to operate, and the overall ecosystem shows no signs of disappearing.
What is PGP, and why does the darknet use it?
PGP (Pretty Good Privacy) is an encryption standard that scrambles messages so only the intended recipient can read them. The darknet uses it to secure communications between buyers and vendors, ensuring that sensitive information like shipping addresses cannot be read even if a market’s servers are seized.
What is escrow on the darknet?
Escrow is a system where a buyer’s payment is held by the market rather than sent directly to the vendor until the order is confirmed as received. It protects buyers from vendors who take payment without delivering, and it is the primary trust mechanism that enables darknet commerce to function at scale.