Every data breach has a story. And at the center of that story is a threat actor.
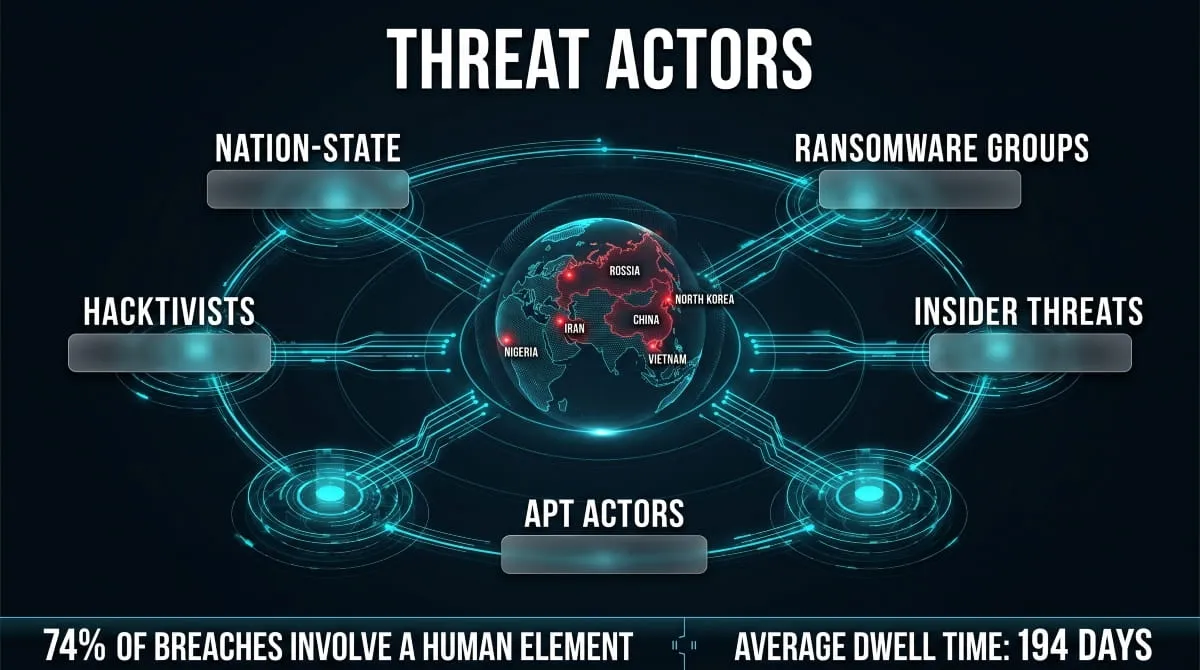
The term gets used constantly in cybersecurity briefings, incident reports, and news headlines, but what does it actually mean? A threat actor isn’t just a hoodie-wearing hacker. It’s a broad term that covers everyone capable of deliberately causing harm to your systems, data, or organization: nation-state operatives running long-term espionage campaigns, ransomware gangs extorting hospitals, insiders leaking sensitive files, and opportunistic criminals scanning the internet for easy targets.
Understanding who threat actors are, their types, motivations, tactics, and how they’re tracked, is no longer optional for security teams. It’s the foundation of every sound defense strategy.
This guide covers the full picture. From the definition of a threat actor and how they differ from a general hacker, to the most dangerous active groups operating today, the techniques they use to penetrate networks and evade detection, and the intelligence methods analysts use to profile and attribute attacks. Whether you’re building your first threat model or deepening your knowledge of advanced persistent threat actors, everything you need is here.
What Is a Threat Actor?
A threat actor is any individual, group, or organization that intentionally compromises the security of a system, network, or dataset. The word “actor” is deliberate; it implies agency, intent, and a role being played within a larger threat landscape. These aren’t accidents or system failures. Threat actors make choices, pursue objectives, and adapt their methods based on what works.
In cybersecurity, a threat actor can be a foreign government running a decade-long espionage operation, a ransomware crew extorting businesses for cryptocurrency, a disgruntled employee leaking internal documents, or a lone opportunist exploiting an unpatched vulnerability. What they share is intent, the deliberate decision to cause harm, steal data, disrupt operations, or gain unauthorized access.
Threat Actor vs. Hacker, What’s the Difference?
The two terms are often used interchangeably, but they mean different things. A hacker is defined by capability, someone with the technical skill to manipulate systems in unintended ways. A threat actor is defined by intent and role within a security context.

Not all hackers are threat actors. Ethical hackers and penetration testers use the same skills to find vulnerabilities before malicious actors do. A threat actor, by contrast, is always operating with a harmful or unauthorized objective. Think of it this way: every threat actor may possess hacker-level skills, but not every hacker is a threat actor.
Threat Actor vs. Threat Vector vs. Threat Agent, Key Distinctions
These three terms appear together frequently in threat intelligence and threat modeling, and the confusion between them is common.
A threat actor is the who, the human or group behind an attack. A threat vector is the method or pathway used to carry out the attack, such as a phishing email, a compromised credential, or an unpatched software vulnerability. A threat agent is a broader term sometimes used interchangeably with threat actor. Still, in formal frameworks, it can also include non-human sources of risk, such as malware or natural disasters.
For practical purposes, when analysts say “identify the threat actor,” they mean find out who did it. When they say “close the threat vector,” they mean block the method. Understanding this distinction keeps threat models clean and response efforts focused.
Why the Term “Threat Actor” Matters in Modern Cybersecurity
Language shapes how we respond to problems. When organizations frame attacks as generic “cyber incidents,” they tend to apply generic solutions: patch, scan, repeat. When they think in terms of threat actors, they ask better questions: Who is targeting us? What do they want? How do they typically operate? Have they hit organizations like ours before?
This shift from reactive to intelligence-led security is exactly why the threat actor framework has become central to modern cybersecurity. Frameworks like MITRE ATT&CK are built around it. Threat intelligence platforms are designed to track and profile specific actors. Incident response teams now routinely attempt attribution, not just to understand what happened, but to anticipate what comes next.
Knowing your threat actor changes everything about how you defend.
Types of Threat Actors in Cybersecurity
Not all threat actors operate the same way, pursue the same goals, or carry the same level of risk. Categorizing them by type is one of the first steps in building an accurate threat model, because the defenses that work against an opportunistic attacker look very different from those needed against a nation-state operation. Here are the primary categories security teams work with today.

Nation-State Threat Actors
Nation-state threat actors are government-backed groups that conduct cyber operations in the service of national interests. Their objectives typically include espionage, intellectual property theft, disruption of critical infrastructure, and political influence. What sets them apart is their resources: government funding, military-grade tooling, and near-unlimited patience.
Groups like Russia’s Sandworm, China’s Volt Typhoon, Iran’s OilRig, and North Korea’s Lazarus Group are well-documented examples. Their campaigns often run for months or years before detection, targeting defense contractors, energy grids, financial institutions, and government agencies. Nation-state threat actors represent the highest tier of adversarial sophistication in the current landscape.
Cybercriminal Organizations and Ransomware Groups
Cybercriminal threat actors are primarily motivated by financial gain. This category includes everything from loosely organized fraud networks to highly structured ransomware operations running affiliate programs, customer support portals, and leak sites.
Ransomware groups like LockBit, ALPHV/BlackCat, Clop, and Akira have turned data extortion into an industry. They compromise networks, exfiltrate sensitive data, encrypt systems, and demand payment, often threatening to publish stolen files if the ransom is not paid. These groups are prolific and adaptive, and are increasingly operating under a Ransomware-as-a-Service (RaaS) model, in which core developers license their infrastructure to affiliates who carry out the actual attacks.
Beyond ransomware, financially motivated threat actors also run large-scale phishing operations, business email compromise (BEC) schemes, credential theft campaigns, and social media impersonation scams targeting consumers and enterprises alike.
Hacktivists
Hacktivist threat actors are driven by ideology rather than profit. Their attacks, typically website defacements, DDoS campaigns, or data leaks, are designed to make a public statement, embarrass a target, or advance a political or social cause.
Groups like Anonymous and KillNet fall into this category. While hacktivists are generally considered less technically sophisticated than nation-state actors or organized cybercriminals, they can cause significant reputational damage and service disruption, particularly for government agencies, media organizations, and corporations they view as ideological targets. During geopolitical conflicts, hacktivist activity tends to spike sharply.
Insider Threat Actors
Not every threat comes from outside the organization. Insider threat actors are individuals who already have legitimate access to systems and data, employees, contractors, vendors, or former staff, and who use that access in ways that cause harm, whether intentionally or through negligence.
Malicious insiders may steal intellectual property, sabotage systems, or sell credentials and access to external actors. Negligent insiders, meanwhile, can cause just as much damage through poor security hygiene, falling for phishing attacks, or misconfiguring systems. Internal threat actors are particularly dangerous because they bypass most perimeter defenses by design; they’re already inside.
Advanced Persistent Threat (APT) Actors
Advanced persistent threat actors, commonly referred to as APTs, represent a specific operational style more than a standalone category. APT groups are characterized by three things: advanced technical capability, a persistent presence inside compromised environments, and a clearly defined long-term objective.
Rather than smash-and-grab attacks, APT actors move slowly and quietly. They establish footholds, maintain access over extended periods, and collect intelligence or position themselves for future action without triggering alarms. Many nation-state groups operate as APTs, but the designation is about behavior and methodology, not origin. APT28 (Fancy Bear), APT29 (Cozy Bear), and APT41 are among the most extensively documented threat actors in the threat intelligence literature.
Script Kiddies and Opportunistic Attackers
At the lower end of the sophistication spectrum are script kiddies, attackers who rely on publicly available tools and exploits without a deep understanding of the underlying techniques. While they lack the skill of more advanced threat actors, they shouldn’t be dismissed entirely. They operate at scale, constantly scanning for unpatched systems, exposed credentials, and misconfigured services.
Opportunistic attackers, whether script kiddies or low-level cybercriminals, are responsible for a significant share of breaches affecting small and mid-sized businesses. They’re not targeting anyone specifically. They’re targeting whoever left a door open.
State-Sponsored vs. Independent Threat Actors
The line between state-sponsored and independent threat actors is increasingly blurred. Some groups operate with direct government backing and explicit tasking. Others enjoy a degree of unofficial tolerance from their host governments, allowed to operate freely as long as their targets are foreign and their activities occasionally serve state interests.
North Korea’s Lazarus Group, for example, conducts operations that serve both intelligence objectives and the regime’s revenue generation. Russian cybercriminal groups have historically operated with implicit government protection. Understanding whether a threat actor has state backing matters enormously for attribution, response strategy, and geopolitical context. Two organizations may face technically identical attacks, but for entirely different reasons, depending on the actor behind them.
Threat Actor Motivations, Why Do They Attack?
Understanding what drives a threat actor is just as important as knowing who they are. Motivation shapes everything: the targets they choose, the methods they use, how long they persist, and what they do with what they take. Two attacks that look identical on the surface can have completely different implications depending on whether the actor behind them wanted money, intelligence, or chaos. Here’s a breakdown of the primary motivations driving threat actor behavior today.

Financial Gain, The Most Common Threat Actor Motivation
If there’s one dominant force behind most cyberattacks, it’s money. Financial gain is the most common motivation for threat actors across sectors and geographies, and it drives an enormous range of criminal activity, including ransomware deployments, credential theft, business email compromise, payment card fraud, cryptocurrency theft, and social media scams.
Ransomware groups are the most visible example. Organizations like LockBit, Akira, and RansomHub treat cybercrime as a business, complete with revenue targets, negotiation teams, and affiliate programs. But financially motivated threat actors don’t stop at ransomware. Large-scale impersonation operations targeting airline customers, crypto investors, and financial service users, many originating from known threat actor regions including Nigeria, Vietnam, Kenya, and Ghana, are equally profit-driven, just operating at a different tier of sophistication.
The financial motive also explains why no sector is safe. Healthcare, education, manufacturing, logistics, if there’s money to extract or data to sell, it’s a viable target.
Espionage and Intelligence Collection
Nation-state threat actors are rarely after quick cash. Their primary motivation is intelligence, and the patience with which they pursue it is what makes them so dangerous.
Cyber espionage campaigns are designed to collect sensitive information over extended periods: government communications, military technology, diplomatic cables, proprietary research, and critical infrastructure blueprints. The goal isn’t disruption, it’s silent, sustained access. A well-placed APT actor inside a defense contractor’s network can exfiltrate valuable data for months before anyone notices.
China-nexus threat actors like Volt Typhoon and Salt Typhoon have been extensively documented conducting espionage against telecommunications infrastructure and government networks. Iranian groups like Charming Kitten target academic researchers and policy professionals. The intelligence-collection motivation is methodical by design; these actors are playing a long game.
Disruption, Sabotage, and Hacktivism
Not every threat actor wants to steal something. Some want to break things. Disruption-motivated attacks aim to take down services, destroy data, or demonstrate that a target is vulnerable, whether to make a political statement, damage a competitor, or destabilize critical infrastructure.
Sandworm, a Russian nation-state group, has carried out some of the most destructive cyberattacks on record, including attacks on Ukraine’s power grid and the NotPetya malware campaign that caused tens of billions of dollars in global damage. These weren’t espionage operations. They were acts of sabotage.
Hacktivists pursue disruption for ideological reasons, conduct DDoS attacks against government websites, leak data from organizations they oppose, and deface websites to embarrass them. The technical sophistication varies widely, but the intent is consistent: visibility and impact over stealth.
Ideological and Political Motivations
Closely linked to disruption, but distinct in character, ideological and political motivations drive a category of threat actors who see cyberattacks as a form of activism, warfare, or resistance. This includes state-sponsored groups acting on national ideology, hacktivist collectives rallying around social causes, and extremist actors targeting organizations that represent opposing values.
During geopolitical flashpoints, elections, conflicts, and sanctions, politically motivated threat actor activity reliably increases. KillNet, a pro-Russian hacktivist group, surged in activity following the Russian invasion of Ukraine, launching coordinated DDoS campaigns against NATO-aligned governments and media organizations. Understanding the ideological context behind an attack helps analysts assess likely targets, timing, and escalation risk.
What Threat Actors Do With Stolen Data
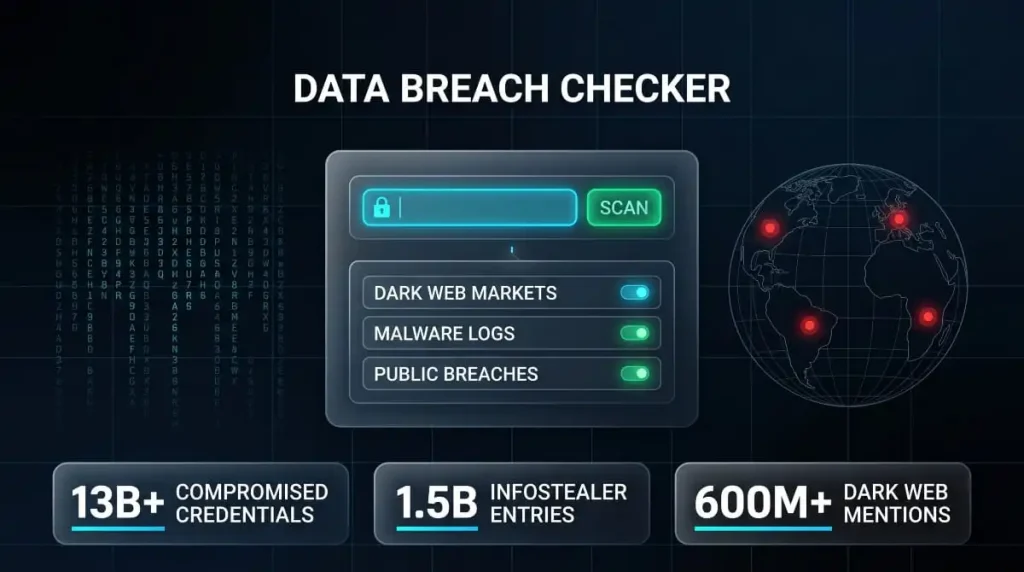
Once data is taken, what happens to it depends heavily on who took it and why. Financially motivated threat actors typically monetize stolen data in one of several ways: selling credentials and personal records on dark web marketplaces, using payment card data for fraud, leveraging corporate secrets for extortion, or offering network access to other criminal groups.
Ransomware actors have increasingly shifted to double extortion, encrypting systems and threatening to release sensitive files if the ransom isn’t paid publicly. This makes the stolen data a second lever of pressure beyond operational disruption alone.
Nation-state actors, by contrast, often don’t sell what they steal. Intelligence collected through espionage campaigns is retained, analyzed, and used to inform future operations, shape foreign policy decisions, or build targeting profiles for subsequent attacks.
Understanding what a threat actor wants to do with your data is a critical part of assessing the true impact of a breach, not just what was taken, but what it enables next.
Threat Actor Tactics, Techniques, and Procedures (TTPs)
Knowing who a threat actor is tells you the “who.” Their TTPs tell you the “how.” Tactics, techniques, and procedures describe the specific methods threat actors use to gain access, maintain presence, move through environments, and achieve their objectives. For security teams, understanding TTPs is what separates reactive incident response from proactive defense, because most threat actors reuse what works, and their patterns are traceable.

Frameworks like MITRE ATT&CK exist specifically to catalog these behaviors, giving analysts a shared language for describing and anticipating threat actor activity across the full attack lifecycle.
How Threat Actors Use Social Engineering and Pretexting
The majority of successful cyberattacks don’t begin with sophisticated zero-day exploits. They begin with a conversation, or something that looks like one. Social engineering remains one of the most effective techniques in any threat actor’s arsenal because it targets the one variable no technical control can fully patch: human judgment.
Pretexting is a form of social engineering in which a threat actor constructs a fabricated scenario to manipulate a target into taking an action or disclosing information. This might look like an attacker impersonating IT support to extract credentials, posing as a vendor to gain invoice payment authorization, or creating fake airline customer service accounts on Twitter to intercept complaints from real customers. That last pattern is particularly prevalent among threat actor groups operating out of known scam regions, Nigeria, Vietnam, Kenya, and Ghana, who have built highly organized impersonation operations targeting consumers across social media platforms.
Phishing, vishing, smishing, and business email compromise all fall under this umbrella. The common thread is deception at the human layer, bypassing technical defenses entirely.
How Threat Actors Move Laterally Through Networks
Getting initial access is only the beginning. Once inside an environment, threat actors work to expand their foothold, a phase known as lateral movement. The objective is to move from an initial entry point, often a low-privilege endpoint, toward higher-value systems: domain controllers, databases, backup infrastructure, and executive accounts.
Common lateral movement techniques include pass-the-hash and pass-the-ticket attacks that abuse stolen authentication credentials, exploitation of misconfigured internal services, and abuse of legitimate administrative tools like Windows Management Instrumentation (WMI) and PowerShell. APT actors are particularly disciplined in this phase, moving slowly, mimicking normal user behavior, and avoiding actions that might trigger anomaly detection.
Understanding how threat actors move laterally through a Windows environment is foundational to network segmentation strategy and detection engineering. The longer the lateral movement goes undetected, the deeper the compromise becomes.
Threat Actors Evading Security Tools (EDR, SEGs)
Modern enterprises deploy layered security, endpoint detection and response (EDR) platforms, secure email gateways (SEGs), SIEMs, and network monitoring tools. Sophisticated threat actors are acutely aware of this and design their operations specifically to evade them.
Techniques for bypassing EDR solutions include living-off-the-land (LotL) attacks that leverage legitimate system binaries to carry out malicious actions, process injection into trusted processes, and, where possible, the deliberate disabling or tampering with security agents. Several threat actors, including Scattered Spider and various ransomware affiliates, have been documented actively attempting to bypass SentinelOne and other EDR platforms before deploying payloads.
To evade SEGs, threat actors have shifted toward using legitimate file-sharing services, encrypted communications channels, and multi-stage phishing that doesn’t contain malicious links in the initial email, triggering only after the gateway has already scanned and passed the message.
Evasion isn’t an afterthought. For advanced threat actors, it’s a core part of operational planning.
RMM Tools, Nmap, and Other Utilities Abused by Threat Actors
One of the more insidious trends in threat actor behavior is the systematic abuse of legitimate software. Remote monitoring and management (RMM) tools, designed for IT teams to manage endpoints remotely, have become a favored persistence mechanism for ransomware groups and cybercriminal actors. Tools like AnyDesk, TeamViewer, Atera, and ScreenConnect appear regularly in incident reports, and attackers use them to maintain access, move laterally, and deploy payloads without triggering alerts tied to known malware signatures.
Nmap, the widely used network scanning utility, is routinely used by threat actors during reconnaissance to map internal networks, identify open ports, and locate vulnerable services. Because it’s a legitimate tool with a genuine security purpose, its use often blends into normal network activity.
This pattern, using trusted, signed, and expected tools to carry out malicious activity, is central to why modern detection strategies have shifted away from purely signature-based approaches toward behavioral analytics.
Threat Actors Using AI to Scale Attacks
Artificial intelligence has lowered the barrier to entry for threat actors at virtually every stage of the attack chain. The most immediate and widespread impact has been on social engineering. AI-generated phishing emails are now grammatically flawless, contextually relevant, and tailored to individual targets at a scale that previously required significant human effort. The grammatical errors that once served as a phishing red flag are largely gone.
Beyond phishing, threat actors are using AI to accelerate vulnerability research, generate malware variants that evade signature detection, and automate credential stuffing and fraud operations. Deepfake audio and video have begun appearing in targeted business email compromise attacks, with threat actors impersonating executives in voice calls to authorize fraudulent transfers.
Staying ahead of threat actors in the age of AI requires security teams to evolve their detection capabilities at the same pace, which increasingly means deploying AI-driven defenses capable of identifying behavioral anomalies that rule-based systems miss entirely.
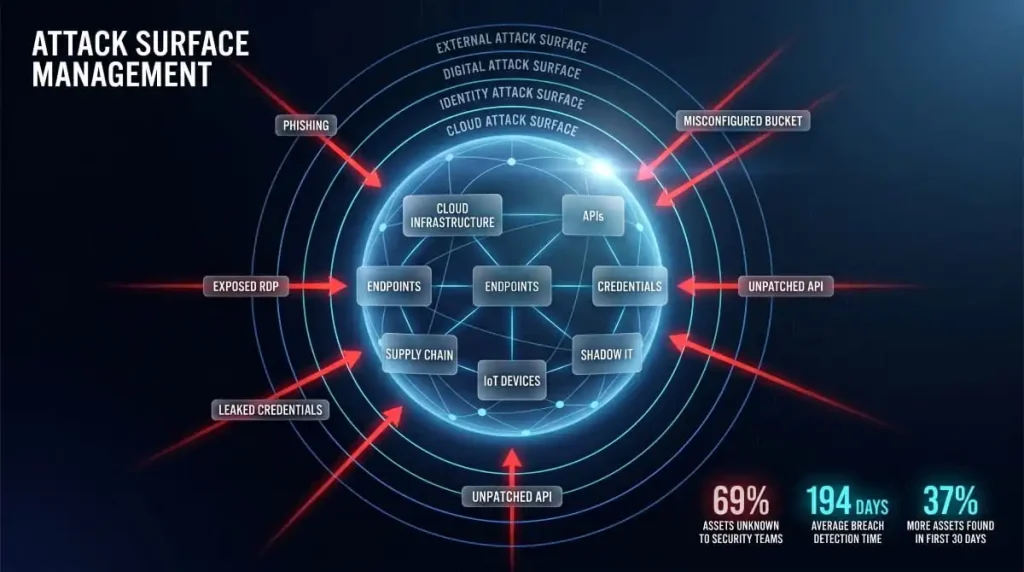
Exploiting Cloud Infrastructure, Current Techniques
As organizations have migrated critical workloads to cloud environments, threat actors have followed. Cloud infrastructure introduces a distinct attack surface and a different set of misconfigurations and vulnerabilities that many security teams are still learning to manage.
Current techniques used by threat actors to exploit cloud environments include targeting exposed API keys and access tokens, abusing overly permissive IAM roles to escalate privileges, exploiting misconfigured storage buckets to access or exfiltrate data, and hijacking cloud compute resources for cryptomining. The UNC5537 campaign against Snowflake-hosted environments in 2024, which affected dozens of major organizations, is one of the most prominent recent examples of how credential-based cloud attacks can produce catastrophic data exposure at scale.
For organizations running hybrid or multi-cloud environments, understanding how threat actors exploit cloud infrastructure isn’t optional. The attack surface is large, the misconfigurations are common, and the consequences of a successful breach in a cloud environment can propagate far faster than in a traditional on-premises network.
The World’s Most Active Threat Actor Groups (2025–2026)
Threat intelligence is only as useful as it is specific. Generic warnings about “cybercriminals” and “hackers” don’t help security teams make decisions. Named threat actor groups do, because they come with documented histories, known TTPs, identified targets, and measurable patterns of behavior. What follows is a reference-level overview of the most significant and active threat actor groups operating in 2025 and into 2026, organized by category.

Nation-State Groups, Russia, China, Iran, North Korea
Nation-state threat actors represent the most sophisticated and well-resourced adversaries in the current landscape. Their operations are patient, deliberate, and often run in parallel, collecting intelligence while pre-positioning for potential disruption.
Russia fields several of the most extensively documented APT groups. Midnight Blizzard (formerly Nobelium, also known as APT29 or Cozy Bear) is a Russian Foreign Intelligence Service (SVR) operation responsible for the SolarWinds supply chain attack and repeated intrusions into government and diplomatic networks across NATO-aligned nations. Fancy Bear (APT28), linked to Russian military intelligence (GRU), has a long record of targeting political organizations, media outlets, and defense infrastructure. Sandworm, also GRU-affiliated, is in a category of its own when it comes to destructive capability, responsible for attacks on Ukrainian power infrastructure and the NotPetya campaign, which remains one of the costliest cyberattacks in history.
China-nexus threat actors have shifted focus in recent years toward telecommunications and critical infrastructure. Volt Typhoon drew significant attention from U.S. intelligence agencies for pre-positioning inside American critical infrastructure networks, not to steal data, but to establish persistent access for potential future disruption. Salt Typhoon emerged as one of the most consequential threat actors of 2024–2025, breaching multiple major U.S. telecommunications providers and accessing systems used for lawful intercept, a deeply sensitive target with significant national security implications.
Iran operates several capable APT groups with a focus on espionage, influence operations, and targeted harassment. Charming Kitten (APT35) is among the most active, running persistent phishing and social-engineering campaigns targeting journalists, academics, human rights activists, and policy researchers. OilRig (APT34) targets government and critical infrastructure across the Middle East, using custom malware and DNS tunneling techniques refined over years of operational use.
North Korea’s cyber program is uniquely dual-purpose, combining intelligence collection with revenue generation for the regime under international sanctions. The Lazarus Group is the most recognized North Korean threat actor, responsible for the 2016 Bangladesh Bank heist, the WannaCry ransomware outbreak, and ongoing cryptocurrency theft operations. Kimsuky and Andariel operate alongside Lazarus, conducting espionage against South Korean government targets, defense contractors, and think tanks focused on Korean Peninsula policy.
Ransomware Threat Actor Groups
The ransomware ecosystem has evolved dramatically. What began as relatively crude encryption-and-ransom schemes has matured into a sophisticated criminal industry with affiliates, negotiators, infrastructure teams, and public-facing leak sites. These are the groups that have defined the ransomware threat landscape over the past few years.
LockBit was, until its partial disruption by law enforcement in early 2024, the most prolific ransomware operation in the world by the number of victims. Despite the takedown, affiliates remained active, and LockBit operators attempted to rebuild their infrastructure, a testament to the RaaS model’s resilience.
ALPHV/BlackCat operated one of the most technically advanced ransomware platforms, written in Rust for cross-platform compatibility. The group was responsible for the devastating attack on Change Healthcare in early 2024 that disrupted prescription processing across the United States. ALPHV subsequently conducted an exit scam against its own affiliates before infrastructure was seized.
Clop is known less for volume than for impact, repeatedly exploiting zero-day vulnerabilities in widely used file transfer software, including MOVEit Transfer and GoAnywhere MFT, to compromise hundreds of organizations simultaneously in single, coordinated campaigns.
Akira has risen sharply in prominence since 2023, targeting mid-market enterprises across manufacturing, education, and professional services with a dual extortion approach. RansomHub, which emerged in 2024 and absorbed many former ALPHV affiliates, has quickly become one of the most active ransomware operations currently tracked by threat intelligence teams.
Other groups worth monitoring include Play, Qilin, Medusa, Dark Angels, Cactus, Fog, Interlock, and Everest, each of which maintains active operations and leak site infrastructure as of 2025–2026. Earlier groups like Conti, REvil, Hive, and DarkSide have formally disbanded or rebranded, but their personnel and techniques have largely migrated into successor operations.
Data Extortion and Breach Actors
A distinct category has emerged alongside traditional ransomware, threat actors who focus primarily on data theft and public exposure rather than encryption. These groups operate by infiltrating environments, exfiltrating large volumes of sensitive data, and then leveraging that data for extortion or selling it directly on criminal marketplaces.
ShinyHunters is one of the most prolific data breach actors on record, responsible for breaches affecting Ticketmaster, Santander, and dozens of other major organizations through the 2024 Snowflake credential campaign. The group has a long history of targeting cloud-hosted databases and selling stolen records at scale.
IntelBroker has established a reputation in dark web communities as a reliable source of high-value corporate data, repeatedly claiming breaches of major technology companies, government contractors, and financial institutions. The actor operates with a level of persistence and targeting discipline that sets them apart from opportunistic data thieves.
888 is a prolific threat actor known for aggregating and leaking large datasets, frequently appearing on breach forums with claimed records from financial institutions and consumer platforms.
Scattered Spider (also tracked as UNC3944 and Octo Tempest) became one of the most discussed threat actors of 2023–2024 after executing social-engineering-heavy intrusions against MGM Resorts and Caesars Entertainment, causing hundreds of millions of dollars in damage. The group is notable for its sophisticated vishing and SIM-swapping techniques and for being composed largely of English-speaking members, challenging the assumption that advanced threat actors are primarily non-Western.
LAPSUS$ made headlines in 2022 with high-profile breaches of Microsoft, Nvidia, Samsung, and Okta, using insider recruitment and social engineering rather than technical exploits as primary access vectors. Several members were subsequently arrested, but the group’s methods have influenced a generation of extortion-focused actors.
UNC5537, the threat actor behind the Snowflake campaign, demonstrated how credential-based attacks against cloud infrastructure can scale into some of the largest breach events in recent history, affecting Ticketmaster, AT&T, and numerous other Snowflake customers through stolen credentials rather than any vulnerability in Snowflake’s own platform.
Financially Motivated Cybercrime Groups
Beyond ransomware, a layer of sophisticated, financially motivated threat actors operates across fraud, malware distribution, initial access brokering, and long-term financial crime. These groups often serve as the infrastructure layer that enables other attacks, selling access, deploying loaders, and establishing the footholds that ransomware affiliates later exploit.
FIN7 is one of the longest-running and most adaptable financially motivated threat actor groups, with a track record spanning nearly a decade. Originally focused on point-of-sale malware targeting the restaurant and hospitality sector, FIN7 has evolved into a broad cybercrime operation involved in ransomware deployment, spear-phishing campaigns, and front-company operations to recruit unwitting security professionals.
FIN8 specializes in targeting retail and hospitality environments to steal payment card data, using custom malware and living-off-the-land techniques to maintain stealth over long dwell times. FIN6 and FIN11 round out the FIN-designated group series, each with documented histories of large-scale financial fraud and malware distribution.
TA505 is a prolific threat actor responsible for some of the largest malspam campaigns ever recorded, historically distributing Dridex, FlawedAmmyy, and Clop ransomware. TA571 and TA866 are active malware distribution actors observed running large-scale email campaigns delivering infostealers and remote access trojans.
Emotet, though significantly disrupted by a 2021 law enforcement operation, has re-emerged in various forms, with its infrastructure and distribution model rebuilt by the threat actors behind it. SocGholish remains an active initial access operation, using fake browser update lures to deliver malware that is subsequently sold as access to ransomware affiliates.
Emerging and Notable Threat Actors to Watch in 2026
The threat landscape doesn’t stand still. Several actors and clusters that gained prominence in late 2024 and 2025 warrant close attention as they mature their operations heading into 2026.
Storm-designated groups from Microsoft’s tracking taxonomy, including Storm-1575, Storm-1747, Storm-2460, and Storm-1849, represent clusters of activity that haven’t yet been fully attributed to known actors but show consistent TTPs and targeting patterns. Storm-2460 drew particular attention for exploiting a Windows vulnerability (CVE-2025-29824) in targeted attacks against organizations across multiple sectors.
DragonForce has evolved from a hacktivist operation into a ransomware operation with a growing affiliate base, claiming responsibility for attacks against high-profile targets in retail and critical infrastructure.
Dark Storm Team has been active in DDoS campaigns against Western targets with politically motivated framing. Hellcat emerged targeting educational institutions and government entities, focusing on data theft and public exposure.
The broader trend to watch in 2026 is the continued convergence of nation-state and cybercriminal tactics, state-sponsored groups adopting financially motivated cover, and criminal actors whose infrastructure and access are increasingly leveraged for intelligence purposes. The line between espionage and crime is becoming harder to draw, and threat actor attribution is becoming correspondingly more complex.
Threat Actor Naming Conventions, How Microsoft, CrowdStrike, and MITRE Name Groups
If you’ve spent any time reading threat intelligence reports, you’ve noticed that the same group can appear under completely different names depending on who’s writing about them. Midnight Blizzard, Cozy Bear, and APT29 are all the same Russian intelligence operation, just named by different organizations using different systems. This isn’t an accident or a branding quirk. Each major threat intelligence vendor maintains its own naming taxonomy, built around their internal tracking methodology and designed to be internally consistent as new groups emerge and old ones evolve.

Understanding how these naming systems work makes threat intelligence reporting significantly easier to navigate.
Microsoft’s Naming System (Blizzard, Typhoon, Tempest, Storm)
Microsoft overhauled its threat actor naming convention in 2023, moving away from chemical element names toward a weather-themed taxonomy that encodes the actor’s suspected origin or type directly into the name. The system works as follows: the noun appended to the actor’s name indicates their category.
Blizzard designates Russian-origin threat actors. Midnight Blizzard (the SVR-linked group previously called Nobelium) and Seashell Blizzard (formerly Iridium, linked to Sandworm) carry this suffix. Typhoon designates Chinese-origin actors; Volt Typhoon, Salt Typhoon, and Silk Typhoon all fall under it. Sandstorm is used for Iranian actors, Sleet for North Korean groups, and Hail for Vietnamese-origin activity.
Tempest designates financially motivated cybercriminal actors; Lace Tempest and Octo Tempest (Scattered Spider) carry this suffix. Storm is a temporary designation assigned to clusters of emerging or unattributed activity that Microsoft is actively tracking but hasn’t yet fully attributed. Storm designations, like Storm-1575, Storm-1747, or Storm-2460, are placeholders that may eventually be upgraded to a permanent name once attribution matures.
This system allows anyone reading a Microsoft threat report to immediately understand the suspected origin and nature of an actor from the name alone.
CrowdStrike’s Animal-Based Naming Convention
CrowdStrike’s naming convention is arguably the most widely recognized in the industry, partly because it predates the others and has been in use long enough that many of its names have become the default shorthand in security conversations. The system assigns animal names to threat actor groups, with the animal species encoding the suspected nation-state origin.
Bear designates Russian actors Fancy Bear (APT28) and Cozy Bear (APT29) as the most prominent examples. Panda designates Chinese actors, Kitten Iranian actors, Chollima North Korean actors, and Spider cybercriminal groups without a dominant nation-state affiliation. Jackal is used for hacktivist actors, and Lynx for Eastern European cybercriminals.
This is why Scattered Spider carries the Spider suffix; CrowdStrike classifies it as a financially motivated criminal actor rather than a nation-state group. The animal naming convention has proven durable and intuitive, and many organizations default to CrowdStrike’s naming even when using intelligence from other vendors.
MITRE ATT&CK Threat Actor Framework
MITRE takes a different approach. Rather than creating proprietary names, MITRE ATT&CK catalogues threat actor groups under the designation Groups, assigning each a G-prefixed identifier (for example, G0007 for APT28) and mapping them to the specific tactics, techniques, and procedures they’ve been observed using. MITRE also aggregates aliases, documenting all the names different vendors use for the same group under a single entry, which makes it an invaluable cross-reference tool.
The power of the MITRE framework isn’t in the naming itself but in the behavioral mapping. Each group entry links directly to the ATT&CK techniques that group has been observed using, the software and tools associated with them, and references to public threat intelligence reporting. For security teams building detections or running threat-informed defense exercises, MITRE’s group profiles are often the most operationally useful reference available.
Why Naming Conventions Matter for Threat Intelligence
The practical consequence of multiple competing naming systems is that following threat intelligence across vendors requires constant translation. A Microsoft report on Midnight Blizzard, a CrowdStrike advisory on Cozy Bear, and an MITRE ATT&CK entry for APT29 all describe the same adversary, but a security analyst who doesn’t know that could easily treat them as separate threats, duplicating effort and missing the full picture.
This is why alias awareness is considered a core skill in threat intelligence analysis. Most mature threat intelligence platforms, including DeXpose, maintain actor alias mappings that connect names across vendor taxonomies, giving teams a unified view of a threat actor regardless of which vendor’s reporting they’re working from.
Beyond operational convenience, naming conventions also carry implicit analytical claims. When Microsoft assigns a Typhoon suffix, they’re making a public attribution statement about Chinese origin. When CrowdStrike names a group Fancy Bear, they’re asserting Russian GRU affiliation. These attributions are based on technical evidence, behavioral analysis, and often classified intelligence, which is why the names themselves carry weight in geopolitical and legal contexts, not just security ones.
Insider Threat Actors, The Danger From Within
Most cybersecurity conversations focus outward, on nation-state groups, ransomware gangs, and external attackers probing perimeter defenses. But some of the most damaging breaches in history have originated from inside the organization itself. Insider threat actors are uniquely dangerous precisely because the defenses designed to stop external attackers don’t apply to them. They already have access. They already know where the valuable data lives. And in many cases, their activity is nearly indistinguishable from normal work.
Who Qualifies as an Internal Threat Actor?
An internal threat actor is anyone who has legitimate, authorized access to an organization’s systems, networks, or data and uses that access to cause harm, whether deliberately or negligently. This definition is broader than most people assume.
The obvious case is the malicious insider: an employee who steals intellectual property before resigning, a system administrator who sabotages infrastructure after being passed over for promotion, or a contractor who exfiltrates client data to sell on criminal forums. These actors are intentional, motivated, and often difficult to detect precisely because their access patterns don’t raise immediate flags; they’re doing things they’re technically permitted to do, just for the wrong reasons.
But internal threat actors also include current and former employees acting under external pressure. Recruitment by outside criminal or nation-state actors is a documented and growing tactic. A financially stressed employee who is approached by a threat actor offering payment for credential access becomes an insider threat, even if they never intended to initiate the access themselves. Former employees whose access credentials were never properly revoked represent a different category, one that’s less about intent and more about access control failure with real-world consequences.
Vendors, third-party contractors, and managed service providers with privileged access to internal systems round out the picture. Supply chain security incidents frequently involve a trusted external party whose access was exploited, either by that party directly or by a threat actor who compromised them first.
Shadow IT and Accidental Insider Threats
Not every insider threat involves malicious intent. A significant and often underestimated category is the accidental insider, an employee who causes a breach through poor judgment, inadequate security awareness, or unauthorized use of unsanctioned tools and services.
Shadow IT, the use of applications, cloud storage, messaging platforms, and software that haven’t been approved or provisioned by the IT department, is one of the most common sources of accidental insider risk. When an employee uploads a sensitive client database to a personal Google Drive to work from home, or uses a consumer file-sharing service to send a contract because the approved method is too cumbersome, they’ve created an exposure that the organization has no visibility into and no control over.
The same applies to employees who fall victim to phishing campaigns, inadvertently hand over credentials to social engineering attacks, or misconfigure shared cloud resources in ways that expose internal data publicly. These individuals aren’t threat actors in the adversarial sense, but their actions produce outcomes that are functionally identical to an intentional breach from the organization’s perspective.
The distinction matters for response but not for risk. Accidental insider incidents are arguably more common than malicious ones, and the data loss they cause is no less real.
How Organizations Detect and Respond to Insider Threats
Detecting insider threat activity is fundamentally different from detecting external attacks. The behavioral baseline is harder to establish, the actions are often technically authorized, and the investigation carries legal and HR sensitivities that an external breach response doesn’t. That said, established approaches significantly improve detection capability.
User and Entity Behavior Analytics (UEBA) is the technical foundation of most modern insider threat programs. By establishing baseline behavioral patterns for each user, what systems they typically access, when, from where, and at what volume, UEBA platforms can surface anomalies that would be invisible to rule-based systems. A finance employee suddenly accessing engineering repositories at 2 am, or a departing employee downloading three years of client records in their final week, are the kinds of signals UEBA is designed to catch.
Data loss prevention (DLP) controls add a second layer of protection by monitoring and restricting the movement of sensitive data across endpoints, email, and cloud services. Privileged access management (PAM) limits what even authorized users can do with their access, enforcing least privilege principles that reduce the blast radius of both malicious and accidental insider incidents.
From a monitoring perspective, dark web intelligence is increasingly important. When employee credentials, internal documents, or proprietary data appear on dark web forums or leak sites, it often provides the first indication that an insider incident has occurred, or that an insider is actively cooperating with an external threat actor. Continuous dark web monitoring gives organizations early warning that would otherwise arrive only after significant damage has occurred.
Response to insider threats requires coordination across security, legal, HR, and executive leadership from the outset. Evidence preservation, access revocation sequencing, and legal obligations around employee data must be managed in parallel, making insider threat response one of the most operationally complex scenarios a security team can face.
Geographic Threat Actor Hotspots, Where Do Attacks Originate?
Cyber attacks aren’t geographically random. Threat intelligence consistently shows that certain regions produce disproportionate volumes of specific attack types, shaped by local economic conditions, enforcement gaps, technical infrastructure, and in some cases, tacit tolerance from local authorities. Understanding where attacks originate doesn’t mean attributing every incident from a given country to a coordinated group. Still, it does help analysts prioritize detections, contextualize IP-based signals, and build more accurate threat models for the specific attack types their organizations face.

Known Threat Actor Regions, Nigeria, Vietnam, Kenya, Ghana (NG, VN, KE, GH)
Four countries appear with notable consistency across threat intelligence reporting on social engineering, impersonation scams, and fraud operations: Nigeria (NG), Vietnam (VN), Kenya (KE), and Ghana (GH). These aren’t coincidental clusters; they represent regions where organized cybercriminal ecosystems have developed over time, often built around specific fraud methodologies that have proven consistently profitable.
Nigeria has the longest documented history in this context. What began with advance-fee fraud, the so-called “419 scams” named after a section of Nigerian criminal law, has evolved into sophisticated multi-vector operations involving business email compromise, romance fraud, impersonation of corporate entities, and social media scams targeting consumers at scale. Nigerian threat actors have demonstrated a particular sophistication in social engineering, building convincing personas and sustaining long-term deceptive relationships with targets.
Vietnam has emerged as a significant source of infostealer malware distribution and large-scale social media fraud. Vietnamese-linked threat actors have been documented running Facebook ad account hijacking operations, credential phishing campaigns, and organized impersonation networks targeting users across Southeast Asia and beyond.
Kenya and Ghana appear frequently in IP geolocation data associated with Twitter impersonation operations, customer support fraud, and cryptocurrency scams, often as either origin points or infrastructure relay locations for broader fraud networks. The presence of these country codes in threat actor IP data is now a recognized signal in fraud detection workflows across multiple industries.
Twitter/Social Media Impersonation Scams, Common Origin Countries
Social media impersonation has become one of the most scalable and low-barrier threat actor operations in the current landscape. The attack model is straightforward: create accounts that convincingly mimic legitimate brands, public figures, or customer service channels, then intercept users who are seeking genuine assistance or engagement.
On Twitter/X, this pattern is particularly well-documented in the airline and financial services sectors. Threat actors monitor brand mentions and complaint hashtags in real time, responding to frustrated customers with fake support accounts before the legitimate brand can engage. The goal is to redirect the customer to a phishing site, extract payment card details under the guise of resolving a complaint, or harvest account credentials.
IP geolocation and infrastructure analysis consistently tie a significant portion of these operations to Nigerian (NG), Kenyan (KE), Ghanaian (GH), and Vietnamese (VN) IP ranges. However, sophisticated actors routinely use VPNs, proxies, and cloud infrastructure to obscure their true origin. The country code correlation is therefore most useful as a probabilistic signal in fraud detection rather than a definitive attribution.
Airline and Customer Support Impersonation, Threat Actor IP Regions
The airline sector is a particularly active hunting ground for impersonation threat actors targeting customer support. Flight disruptions, delays, lost baggage, and refund requests generate high volumes of distressed customers publicly posting on social media, creating a constant stream of targets for fake support accounts to exploit.
Threat actors operating in this space build out convincing account profiles, often with plausible handles, profile pictures, and pinned posts mimicking legitimate airline support pages, and engage customers at the exact moment of peak frustration. The social engineering success rate in these scenarios is high because the target is already primed to engage with anyone offering a resolution.
Infrastructure analysis of these campaigns shows recurring IP location patterns tied to NG, VN, KE, and GH ranges, with some operations also routing through the UK (GB) and Canadian (CA) infrastructure, either through legitimate cloud services, residential proxies, or compromised systems in those countries. The use of Western IP addresses in these operations is deliberate, as it reduces the friction of platform-level geo-based fraud detection.
UK (GB), Canada (CA), and Other IP Location Patterns
The appearance of UK (GB) and Canadian (CA) IP addresses in threat actor infrastructure data is a recurring point of confusion for analysts. These aren’t necessarily indicators of UK or Canadian-based threat actors; they more commonly reflect the abuse of legitimate cloud hosting, residential proxy services, and VPN exit nodes in those countries by actors whose true origin lies elsewhere.
GB country code IP addresses appear frequently in threat intelligence associated with impersonation scams, phishing infrastructure, and fraud relay networks, particularly when threat actors attempt to appear geographically credible to targets in Europe. Canada similarly appears as a proxy layer in operations targeting North American consumers and financial institutions.
This pattern underscores an important principle in IP-based threat actor attribution: geolocation of an IP address tells you where infrastructure is hosted, not necessarily where the threat actor is operating from. Effective threat intelligence uses IP location as one data point among many, correlated with behavioral patterns, registration data, payment infrastructure, and historical campaign overlap, rather than as a standalone attribution signal.
Crypto Scam Threat Actor Regions
Cryptocurrency scams represent one of the fastest-growing segments of financially motivated threat actor activity, and their geographic distribution closely mirrors the broader fraud ecosystem. Nigeria, Vietnam, Kenya, and Ghana again feature prominently in crypto-related threat actor IP data, particularly for pig butchering scams, fake investment platforms, and social media-based crypto giveaway fraud.
The crypto sector is an attractive target for threat actors across these regions for several reasons: transactions are irreversible, recovery mechanisms are limited, and the relatively new and complex nature of cryptocurrency makes it easier to deceive targets who lack deep familiarity with how legitimate platforms operate.
Beyond these four countries, Southeast Asia has emerged as a major hub for industrialized crypto fraud operations, particularly from Myanmar, Cambodia, and Laos, where large-scale scam compounds have been documented operating with thousands of workers, many of whom are themselves victims of human trafficking. These operations represent a convergence of organized crime, fraud, and human rights abuse that sits at the end of the threat actor geography picture.
For organizations in financial services, fintech, and crypto platforms specifically, geographic threat actor data isn’t just a threat intelligence artifact; it’s an active input into fraud detection models, transaction monitoring systems, and account verification workflows.
Threat Actor Profiling and Attribution
Responding to a cyberattack without knowing who’s behind it is like treating symptoms without diagnosing the disease. You might manage the immediate damage, but you’re not equipped to anticipate what comes next, predict future targets, or build defenses calibrated to the actual adversary. Threat actor profiling and attribution are intelligence disciplines that turn raw attack data into actionable knowledge about the humans and organizations behind threats.

What Is Threat Actor Profiling?
Threat actor profiling is the process of building a structured, evidence-based picture of an adversary, who they are, what they want, how they operate, and what they’re likely to do next. A threat actor profile isn’t a single data point. It’s an aggregated intelligence product that draws on technical indicators, behavioral patterns, historical campaign data, dark web activity, and open source intelligence to construct a coherent picture of a specific actor or group.
Profiling serves multiple functions. For security teams, knowing a group’s preferred techniques informs detection engineering: you can build detections tuned to their specific behavior rather than generic attack patterns. For incident responders, it shapes containment strategy, understanding whether you’re dealing with a financially motivated ransomware affiliate or a nation-state APT actor changes every decision about how aggressively to act and how carefully to preserve evidence. For executive leadership, it translates technical threat data into a business risk context that informs investment decisions and regulatory disclosures.
Building a Threat Actor Profile, Key Attributes
A well-constructed threat actor profile covers several core dimensions. Origin and suspected affiliation, whether the group is nation-state sponsored, financially motivated, hacktivist, or independent, establishes the foundational context for everything else. Known aliases and cross-vendor naming help analysts correlate intelligence from multiple sources without treating the same group as separate threats.
Targeting patterns are among the most practically useful profile attributes. Which sectors does this actor consistently hit? What company sizes and geographies appear in their victim lists? Understanding targeting preferences helps organizations assess their relevance as potential targets; not every group is indiscriminate, and many APT actors have well-documented industry focus areas.
TTPs form the technical core of any profile, the specific tactics, techniques, and procedures the actor has been observed using, ideally mapped to the MITRE ATT&CK framework. Infrastructure indicators, including known IP ranges, domain registration patterns, malware families, and C2 communication methods, provide the detection layer. Motivation and objectives, recent activity timeline, and known operational security habits round out a profile that’s genuinely useful rather than merely descriptive.
Threat Actor Attribution, How Analysts Identify Who’s Behind an Attack
Attribution is one of the hardest problems in cybersecurity and one of the most consequential. Correctly identifying the threat actor behind an attack enables targeted response, informs legal and diplomatic action, and helps the broader community defend against future campaigns from the same group. Incorrect attribution, or premature attribution, can misdirect response efforts and cause significant geopolitical harm.
Analysts approach attribution by simultaneously correlating multiple evidence streams. Technical attribution relies on malware code similarities, reuse of infrastructure, distinctive TTPs, and overlaps with previously documented campaigns. Operational attribution examines the timing, targeting logic, and objectives of an attack; nation-state operations tend to show a consistent strategic focus that financially motivated groups don’t. Strategic attribution considers the geopolitical context: who benefits from this attack, and does that align with a known actor’s documented interests?
No single indicator is sufficient for confident attribution. A threat actor reusing a known malware family might be the original group, a copycat, or a false flag operation designed to implicate someone else. Sophisticated nation-state actors have been documented deliberately using tools and TTPs associated with other groups to complicate attribution. This is why serious threat intelligence firms express attribution with confidence levels rather than certainties, and why public attribution statements from government agencies carry the weight they do; they represent the convergence of classified and open-source evidence that private analysts don’t have full access to.
OSINT-Based Threat Actor Investigation
Open source intelligence, OSINT, is the practice of collecting and analyzing information from publicly available sources to develop intelligence products. In the context of threat actor investigation, OSINT encompasses a wide range of sources: dark web forums and marketplaces, paste sites, social media platforms, domain registration records, certificate transparency logs, code repositories, breach databases, and public malware sandboxes.
OSINT-based threat actor profiling begins with a known indicator, a malware hash, a C2 domain, a dark web forum handle, or a cryptocurrency address. It expands outward through a process of pivot analysis. Each data point potentially connects to others: a domain leads to a registrant email, which appears in a forum registration, which links to a Bitcoin wallet, which connects to an exchange withdrawal. The discipline is in knowing which pivots are meaningful and which are noise.
OSINT is particularly powerful for investigating financially motivated threat actors and fraud networks, who tend to leave more visible traces across public-facing criminal infrastructure than nation-state groups operating under strict operational security protocols. Dark web monitoring, in particular, provides continuous visibility into threat actor activity that would otherwise be entirely invisible, including the sale of stolen credentials, the advertisement of network access, and direct communications between actors about targeting decisions.
How Open Source Intelligence Identifies Threat Actors (2025–2026 Methods)
The OSINT toolkit for threat actor investigation has expanded significantly in recent years, driven by both the growth of open criminal infrastructure and advances in the tools available to analysts. In 2025 and into 2026, several methods have become particularly central to threat actor identification work.
Leak site and extortion blog monitoring has become a primary early warning mechanism. Ransomware and data extortion groups maintain public-facing infrastructure to pressure victims, and that infrastructure is a continuous source of intelligence about active campaigns, targeted organizations, and actor behavior patterns. Automated monitoring of these sites, correlated with dark web forum activity, gives analysts near-real-time visibility into the threat actor landscape.
Telegram has emerged as a major operational platform for threat actors across fraud, ransomware, and hacktivism, with groups using channels and groups to communicate, recruit, advertise stolen data, and coordinate attacks. OSINT collection from Telegram, while technically and legally nuanced, has become an important source of threat actor intelligence that didn’t exist at scale five years ago.
AI-assisted OSINT analysis is increasingly being deployed to process the volume of data that human analysts alone cannot cover, correlate indicators across disparate sources, surface connections between forum handles and infrastructure, and flag behavioral anomalies in actor activity that might indicate an imminent campaign or a shift in targeting.
Identifying Threat Actor Cryptocurrency Addresses
Cryptocurrency has become the financial backbone of the cybercriminal economy, used for ransomware payments, dark web marketplace transactions, money laundering, and payments to criminal affiliates. And unlike cash, cryptocurrency leaves a permanent, publicly auditable trail on the blockchain.
Blockchain analytics has become a mature discipline within threat actor investigation. By tracing the flow of funds from known ransom payments or fraud proceeds through the blockchain, analysts can identify clusters of addresses controlled by the same actor, track fund movements toward exchange withdrawal points, and, in some cases, link on-chain activity to real-world identities when funds interact with regulated exchanges that maintain KYC records.
Law enforcement agencies and private threat intelligence firms now routinely identify threat actor cryptocurrency addresses as part of both investigation and sanctions processes. The U.S. Treasury’s OFAC has sanctioned specific cryptocurrency addresses associated with groups like Lazarus and Evil Corp, making those addresses radioactive within the regulated financial system and significantly complicating threat actors’ ability to convert proceeds to fiat currency.
For organizations that have paid ransoms or been targeted by crypto fraud, blockchain tracing of threat actor addresses offers a recovery path that didn’t exist in the era of untraceable wire transfers. However, recovery rates remain low, and the process is complex.
Linking Fraud Activity to Specific Threat Actors
Attribution of fraud activity, impersonation scams, business email compromise, and social media fraud to specific threat actors follows a similar logic to technical attack attribution. Still, it draws more heavily on behavioral and infrastructure analysis than on malware forensics.
Analysts look for consistency across campaigns: recurring phone numbers, email templates, domain registration patterns, social media account creation behaviors, and payment collection methods that tie separate fraud incidents to the same underlying operation. When the same Bitcoin wallet appears across multiple unrelated fraud complaints, or when a cluster of fake airline support accounts all registered within the same 24-hour window and follow identical engagement scripts, those patterns point toward a coordinated actor rather than isolated individuals.
Dark web intelligence adds critical depth to fraud attribution. Threat actors advertising fraud services, selling impersonation toolkits, or recruiting money mules on criminal forums leave traces that connect their online criminal identity to specific campaign activity. Cross-referencing fraud incident data with dark web monitoring output to identify overlaps in infrastructure, methods, and claimed victims is one of the most effective ways to move from “a fraud occurred” to “this specific actor or group is responsible.”
This kind of linked intelligence is exactly what separates reactive fraud reporting from proactive threat actor tracking, and it’s the difference between organizations that get hit repeatedly by the same actor and those that see the pattern early enough to shut it down.
How to Detect and Monitor Threat Actor Activity
Detection is where threat intelligence becomes operational. Building detailed profiles of threat actor groups and understanding their TTPs is only valuable if that knowledge translates into the ability to spot their activity early, ideally before significant damage has occurred. The organizations that consistently outperform their peers in breach outcomes aren’t necessarily the ones with the biggest security budgets. They’re the ones with the best visibility. Here’s what that visibility looks like in practice.

Best Practices for Detecting an Active Threat Actor
The first principle of threat actor detection is accepting that perimeter defense alone is insufficient. Sophisticated threat actors, and increasingly even less sophisticated ones, are capable of bypassing boundary controls. The detection posture that matters is what happens after initial access: can you identify that someone is inside your environment, moving through it, and working toward an objective before they reach it?
Behavioral detection is the foundation. This means establishing baselines for normal activity across users, systems, and network traffic, then building detections around deviations from those baselines. A user account suddenly authenticating from an unusual geography, a service account accessing file shares it has never touched, a process spawning child processes in an unusual sequence, these are the signals that distinguish threat actor activity from routine operations.
Threat-informed detection takes this further by mapping your detection coverage directly to the TTPs of the threat actors most likely to target your organization. If you’re in financial services and FIN7 has a documented history of targeting your sector, your detection engineering should explicitly cover FIN7’s known techniques, not as the only priority, but as a verified coverage area. MITRE ATT&CK provides the framework for this kind of structured detection gap analysis.
Reducing dwell time is the operational objective. The longer a threat actor remains undetected within an environment, the greater the potential damage. Industry data consistently shows that organizations with active threat hunting programs, where analysts proactively search for signs of compromise rather than waiting for alerts, detect intrusions significantly faster than those relying solely on automated detection.
Threat Actor Tracking, Tools, and Methodologies
Tracking threat actors over time, across campaigns, infrastructure changes, and tactical evolutions, requires a combination of tooling and analytical methodology that goes beyond what standard security operations centers typically maintain.
Threat intelligence platforms (TIPs) serve as the operational hub for tracking threat actors in mature security programs. They aggregate indicators of compromise, actor profiles, campaign data, and intelligence feeds from multiple sources into a unified environment where analysts can query, correlate, and share intelligence. The quality of a TIP is largely determined by the depth and freshness of its underlying data, which is why feed selection and dark web source coverage matter enormously.
MITRE ATT&CK Navigator is widely used for mapping known threat actor TTPs against an organization’s detection and control coverage, identifying gaps that need to be addressed. Malware analysis sandboxes allow analysts to safely detonate suspected malicious files and extract behavioral indicators that can be tied back to known actor toolsets. Network traffic analysis platforms provide the packet-level visibility needed to detect C2 communications, lateral movement, and data exfiltration attempts that endpoint tools might miss.
Passive DNS and domain analysis tools are essential for tracking threat actor infrastructure over time. Threat actors regularly rotate domains and IP addresses, but their registration patterns, hosting preferences, and certificate behaviors often remain consistent, creating trackable signatures that persist even as individual indicators change.
Data Capture From Leak Sites and Threat Actor Infrastructure
Ransomware groups and data extortion actors maintain public-facing infrastructure, leak sites hosted on the Tor network, dedicated data publication portals, and countdown timers designed to pressure victims into paying. For threat intelligence teams, this infrastructure is a continuous and highly valuable data source.
Systematic monitoring of leak sites provides early warning when an organization or a known partner, supplier, or customer has been compromised, often before the victim organization itself has made a public disclosure or even fully assessed the breach internally. It also provides a running picture of which threat actor groups are most active, which sectors they’re targeting, and how their operational tempo is shifting over time.
Beyond leak sites, threat actor infrastructure monitoring extends to dark web forums where actors advertise initial access to compromised networks, paste sites where credentials and configuration data are dumped, and Telegram channels where groups coordinate operations and recruit affiliates. Capturing data from these sources at scale requires automation; the volume of content across criminal infrastructure is far beyond what manual monitoring can cover, and analyst oversight is needed to assess relevance and filter signal from noise.
Infrastructure overlap analysis adds another dimension: when a newly observed domain shares registration details, hosting history, or certificate patterns with infrastructure previously attributed to a known threat actor, that overlap is an attribution signal. Tracking these connections over time builds a progressively richer map of how specific actors maintain and evolve their operational infrastructure.
Dark Web Threat Actor Monitoring
The dark web is where the operational reality of the threat actor ecosystem is most visible. Stolen credentials are bought and sold. Network access is advertised and auctioned. Ransomware affiliates are recruited. Data breach victims are named before public disclosure. Fraud toolkits are distributed. Criminal reputations are built and destroyed.
For organizations serious about threat actor monitoring, dark web visibility isn’t optional; it’s a core intelligence requirement. The question isn’t whether your organization’s data will appear on dark web forums and marketplaces. It’s whether you’ll know about it when it does, and how quickly you can respond.
Effective dark web monitoring goes beyond simple credential scanning. It includes tracking mentions of your organization’s name, domains, and executive identities across criminal forums; monitoring for the sale of access to your network or cloud infrastructure; identifying third-party and supply chain exposures before they propagate to your own environment; and capturing intelligence about threat actor campaigns that are targeting your sector before those campaigns reach you.
The challenge is coverage. The dark web is vast, fragmented, and constantly shifting; forums go offline, move, or require vetting for membership. Intelligence sources that provide genuine depth across this environment require sustained, specialized investment that most organizations can’t build internally.
Real-Time Threat Actor Intelligence With DeXpose
DeXpose is built specifically for the monitoring challenge that makes dark web threat actor intelligence so difficult to operationalize at scale. The platform provides continuous visibility into dark web markets, data breach sources, ransomware leak sites, and criminal forum infrastructure, delivering real-time alerts when your organization’s assets, credentials, or data are involved in threat actor activity.
Rather than periodic scans that leave detection gaps between sweeps, DeXpose monitors continuously, so you know immediately when a threat actor advertises access to your network, posts your stolen data, or lists your employees’ credentials for sale.
For security teams building out threat actor monitoring capabilities, DeXpose eliminates the need to maintain internal dark web collection infrastructure, providing the depth of coverage of a dedicated intelligence operation through a platform designed for operational teams rather than specialist analysts alone.
Start with a free dark web report for your organization at Dark Web Monitoring, and see exactly what threat actors already know about you.
Current Threat Actor Trends (2025–2026)
The threat actor landscape doesn’t stand still. Groups emerge, rebrand, dissolve, and reconstitute. Tactics that worked last year get detected and retired; new techniques get developed and deployed at scale. Staying current on threat actor trends isn’t an academic exercise; it’s what separates organizations that anticipate attacks from those that are perpetually surprised by them. Here’s where the landscape stands heading into 2026.

Top Active Threat Actors Right Now
The most consequential threat actors currently operating span both nation-state and cybercriminal categories, and several have demonstrated a concerning convergence of the two.
On the nation-state side, Salt Typhoon remains one of the most actively discussed threat actors in intelligence circles following its sustained campaign against telecommunications infrastructure. This operation gave the group access to sensitive communications data at a scale that continues to have unresolved national security implications. Volt Typhoon’s pre-positioning activity within U.S. critical infrastructure has similarly remained a priority concern for government cybersecurity agencies, with the group’s patient, low-noise approach making it particularly difficult to eradicate once fully identified.
In the ransomware space, RansomHub has rapidly consolidated as one of the most active operations following the disruption of LockBit and the exit of ALPHV, absorbing affiliates from both and producing a high volume of confirmed victims across the healthcare, legal, and manufacturing sectors. Akira continues its steady targeting of mid-market organizations. Fog, Play, and Qilin maintain active operations with consistent victim publication cadence on their respective leak sites.
Among data extortion and breach actors, IntelBroker and the 888 threat actor remain prolific on criminal forums, regularly publishing claimed breaches of high-profile organizations and selling data packages that include employee credentials, customer records, and internal documentation.
How Threat Actor Behavior Has Evolved With AI
Artificial intelligence has introduced a capability step-change for threat actors that security teams are still fully reckoning with. The changes aren’t hypothetical or future-facing; they’re already visible in active campaigns across multiple threat actor categories.
The most immediate and widespread impact has been on the quality and scale of social engineering operations. AI-generated phishing content has effectively eliminated the grammatical and stylistic errors that previously served as primary indicators of malicious email. Spear-phishing messages are now generated at an individual scale, personalized with target-specific context, written in fluent native-language prose, and calibrated to the precise psychological triggers most likely to produce the desired action. What previously required a skilled human social engineer to craft for each target can now be produced in volume with minimal effort.
Voice cloning and deepfake audio have moved from a theoretical concern to documented operational use. Business email compromise attacks increasingly incorporate AI-generated voice impersonation of executives, phone calls that convincingly replicate a CEO’s voice authorizing an urgent wire transfer, or IT support calls that pass basic voice recognition checks. Several cases of successful deepfake-enabled BEC fraud have been publicly documented, resulting in losses in the millions.
On the malware development side, AI assistance has accelerated the production of novel malware variants specifically designed to evade current signature-based detection. Threat actors are using large language models to generate code variations, identify obfuscation techniques, and produce functional exploit code from vulnerability descriptions, tasks that previously required deep technical expertise and significant development time.
The defensive implication is clear: detection strategies built around content patterns, linguistic signals, and known malware signatures are becoming progressively less reliable. Behavioral detection, anomaly analysis, and AI-driven defensive tooling are no longer optional investments for organizations facing sophisticated threat actors.
Ransomware-as-a-Service, The Industrialization of Cybercrime
Ransomware-as-a-Service has fundamentally restructured how ransomware threat actors operate, dramatically expanding the scale and reach of ransomware as an attack category. The RaaS model separates the development and maintenance of ransomware infrastructure from the actual execution of attacks, enabling a division of labor that mirrors legitimate software business models with unsettling fidelity.
Core developers build and maintain the ransomware platform, the encryption engine, the negotiation portal, the leak site infrastructure, and the affiliate management backend. Affiliates pay a percentage of ransom proceeds, typically between 20 and 30 percent, in exchange for access to the platform and support from the core team. The affiliates handle everything else: gaining initial access, deploying the payload, and managing victim negotiations.
The consequences of this model are significant. It means that the technical barrier to conducting a sophisticated ransomware attack has dropped to near zero; an affiliate needs only social engineering skills and initial access, not the ability to write functional ransomware code. It means that disrupting a ransomware group’s core infrastructure, while valuable, doesn’t eliminate the threat posed by its affiliate network, which can simply migrate to a competing platform. And it means the ransomware ecosystem has become self-sustaining, making it deeply resilient to law enforcement action.
The 2024 disruptions of LockBit and ALPHV illustrated this dynamic clearly. Both operations were significantly disrupted; infrastructure seized; administrators identified; decryption keys released. Within weeks, affiliates from both programs had migrated to RansomHub and other active platforms, and victim counts continued to climb. The platform changed; the ecosystem persisted.
Threat Actors Targeting Financial Services and Critical Infrastructure
Financial services and critical infrastructure have long been high-value targets for threat actors across all motivation categories. In 2025–2026, both sectors are experiencing sustained, escalating pressure from multiple directions simultaneously.
Financial services organizations face a layered threat: ransomware groups targeting operational disruption and extortion, nation-state actors conducting long-term espionage and pre-positioning, fraud networks running account takeover and social engineering campaigns, and data extortion actors specifically hunting for customer financial records that command premium prices on dark web markets. The convergence of these threats means that financial institutions are effectively managing four distinct threat actor categories with different objectives, different TTPs, and different response requirements, all at the same time.
Critical infrastructure, energy, water, telecommunications, transportation, and healthcare have become the focus of nation-state pre-positioning activity at a scale that has drawn explicit warnings from government cybersecurity agencies across multiple Western nations. Volt Typhoon’s documented presence inside U.S. energy and water infrastructure, Salt Typhoon’s telecommunications intrusions, and Sandworm’s demonstrated willingness to execute destructive attacks against power grids represent a category of threat that goes beyond data theft into genuine physical consequence territory.
The healthcare sector deserves specific mention. Ransomware attacks against hospitals and healthcare networks have continued at a devastating pace, with the Change Healthcare attack of early 2024, attributed to ALPHV/BlackCat, serving as a stark illustration of how a single ransomware incident in a healthcare supply chain can cascade into disruption affecting patient care across an entire national system.
State-Sponsored Threats to Government Systems
Government systems at every level, federal agencies, defense contractors, legislative bodies, diplomatic missions, and municipal infrastructure, remain primary targets for state-sponsored threat actors pursuing intelligence collection, influence operations, and strategic pre-positioning.
The scale and persistence of nation-state targeting of government systems has grown markedly in the current geopolitical environment. Russia’s continued focus on NATO-member government networks, China’s systematic targeting of defense industrial base contractors and government research institutions, Iran’s campaigns against policy organizations and government-adjacent think tanks, and North Korea’s targeting of sanctions-related agencies and cryptocurrency regulatory bodies all reflect deliberate, strategically directed operations rather than opportunistic attacks.
What makes state-sponsored threats to government systems particularly challenging to defend against is the combination of resources, patience, and intelligence that backs them. These threat actors conduct extensive pre-attack reconnaissance, invest in custom tooling designed to evade security controls known to be deployed in their target environments, and maintain operational discipline to move slowly enough to avoid triggering behavioral detection. Midnight Blizzard’s sustained campaigns against government and diplomatic networks, including the 2023 Microsoft email compromise that gave the group access to communications between Microsoft and U.S. government customers, exemplify the kind of methodical, high-value targeting that state-sponsored groups excel at.
The trend heading into 2026 is toward greater integration of cyber operations with broader geopolitical and information operations, attacks designed not just to collect intelligence or cause disruption in isolation, but to support influence campaigns, shape diplomatic outcomes, and create ambiguity about what has actually occurred and who is responsible. For government security teams, this means threat actor monitoring can no longer be siloed from the broader intelligence and geopolitical context in which these operations take place.
Conclusion
Threat actors are not a monolithic force; they’re a diverse ecosystem of adversaries defined by different origins, motivations, and methods. Understanding who they are, how they operate, and where they leave traces is what separates organizations that get breached and stay breached from those that detect early, respond fast, and build defenses that actually fit the threat they face.
The intelligence exists. The patterns are documented. The question is whether your organization has the visibility to act on them before the damage is done.
Find out what threat actors already know about your organization, Run a free dark web report
Frequently Asked Questions (FAQ’s)
What is a threat actor in cybersecurity?
A threat actor is any individual, group, or organization that intentionally attempts to compromise the security of a system, network, or data. The term covers a wide range of adversaries, from nation-state operatives and ransomware gangs to insider threats and opportunistic criminals, all defined by their intent to cause harm or gain unauthorized access.
What are the 5 types of threat actors?
The five primary types of threat actors are nation-state actors, cybercriminal organizations, hacktivists, insider threats, and advanced persistent threat (APT) groups. Each category is defined by different motivations, capabilities, and targeting behaviors, from government-backed espionage operations to financially motivated ransomware crews to ideologically driven hacktivist collectives.
What is the most common motivation for a threat actor?
Financial gain is the most common motivation for threat actors by a significant margin. The majority of cyberattacks, including ransomware deployments, credential theft, business email compromise, and social media fraud, are ultimately driven by the pursuit of money, whether through direct extortion, data sales, or large-scale fraud operations.
What is the difference between a threat actor and a hacker?
A hacker is defined by technical capability, the skill to manipulate systems in unintended ways, while a threat actor is defined by intent and role. Not all hackers are threat actors; ethical hackers and security researchers use the same skills defensively. A threat actor is always operating with a harmful or unauthorized objective, making intent the critical distinction between the two.
Who are the most dangerous threat actors right now?
The most dangerous threat actors currently active include nation-state groups such as Midnight Blizzard, Volt Typhoon, and Salt Typhoon, as well as ransomware operations such as RansomHub, Akira, and Clop. Data extortion actors, including IntelBroker and ShinyHunters, also rank among the most consequential, having been responsible for some of the largest breach events of 2024–2025.
What do threat actors do with stolen data?
Financially motivated threat actors typically sell stolen data on dark web marketplaces, use credentials for account takeover fraud, or leverage sensitive files for double extortion, threatening public release unless a ransom is paid. Nation-state actors, by contrast, generally retain stolen data for intelligence purposes, using it to inform espionage operations, build targeting profiles, or support future campaigns rather than monetizing it directly.
How do you detect a threat actor in your network?
Effective threat actor detection relies on behavioral analytics to identify deviations from established user and system baselines, threat-informed detection engineering mapped to known adversary TTPs, and active threat hunting rather than passive alert monitoring. Dark web monitoring adds an external layer, alerting organizations when their credentials or network access appear in criminal markets before an active intrusion is even detected internally.
What is an advanced persistent threat (APT) actor?
An advanced persistent threat actor is a highly capable adversary, typically nation-state affiliated, that gains access to a target environment and maintains that presence over an extended period to achieve a specific long-term objective. APT actors are characterized by advanced technical capability, deliberate stealth, and sustained focus on high-value targets such as government agencies, defense contractors, and critical infrastructure operators.
What is a nation-state threat actor?
A nation-state threat actor is a government-backed group that conducts cyber operations in the service of national interests, including espionage, intellectual property theft, infrastructure disruption, and political influence. Examples include Russia’s Midnight Blizzard, China’s Volt Typhoon, Iran’s Charming Kitten, and North Korea’s Lazarus Group, each operating with government resources, specialized tooling, and strategic direction from their respective intelligence or military apparatus.
Which threat actors are motivated purely by financial gain?
Cybercriminal organizations are the category most purely driven by financial motivation. This includes ransomware groups like LockBit, Akira, and RansomHub; data extortion actors like ShinyHunters and IntelBroker; fraud networks running impersonation and business email compromise operations; and financially motivated groups like FIN7, FIN8, and TA505 that specialize in payment card theft, malware distribution, and initial access brokering. Unlike nation-state actors, these groups select targets based on revenue potential rather than strategic or ideological criteria.